
[ad_1]
Learn the technical particulars a few new AiTM phishing assault mixed with a BEC marketing campaign as revealed by Microsoft, and discover ways to mitigate this menace.

A report from the Microsoft Defender Specialists reveals a brand new multi-staged adversary within the center phishing assault mixed with a enterprise electronic mail compromise assault focusing on banking and monetary establishments. The complicated assault abuses trusted relationships between distributors, suppliers and extra organizations concerned in monetary transactions.
Leap to:
Stage one: Launching an AiTM phishing assault
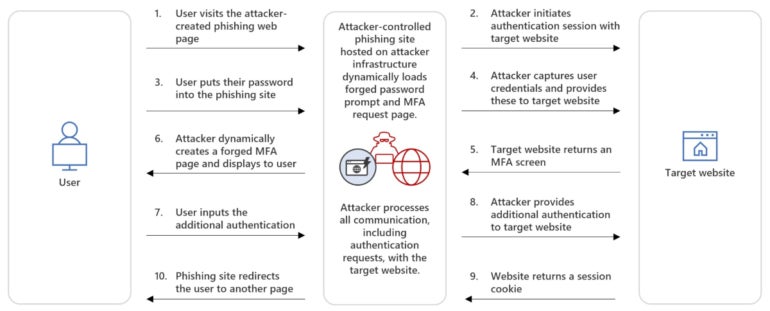
AiTM assaults are operations through which a nasty actor intercepts and modifies communications between two events, usually a person and a reliable authentication service, to steal delicate or monetary data, comparable to log-in credentials and bank card knowledge. It may also be used to bypass multifactor authentication by stealing customers’ session cookies.
Whereas earlier AiTM assaults typically used reverse proxy methods to deal with the visitors between the person and the authentication service, this time the attackers used an oblique proxy methodology. This system is barely completely different because the attacker controls the whole lot instantly from a phishing web site that mimics the sign-in web page of the focused service. The web site processes all communication, together with authentication requests, with the goal.
The person is enticed to go to the phishing web page, enters their credentials and fills within the further MFA authentication, which is a pretend MFA request coming instantly from the attackers. Within the background and straight from the phishing server, the attacker initiates communication with the focused service and enters the legitimate customers’ credentials after which the MFA data. The person is being redirected to a different web page at that second, whereas the attacker receives a sound session cookie impersonating the person (Determine A).
Determine A
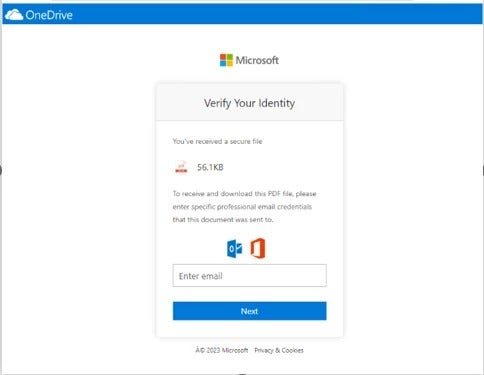
Within the assault reported by Microsoft and run by a menace actor dubbed Storm-1167, the AiTM hyperlink is distributed to the sufferer by way of electronic mail. The phishing electronic mail impersonates one of many goal’s trusted distributors to look extra reliable and mix with reliable electronic mail visitors and bypass detections, particularly when a company has insurance policies to mechanically enable emails from trusted distributors.
In Microsoft’s instance, the menace actor abused Canva’s reliable graphic design platform to host a web page displaying a pretend OneDrive doc resulting in the phishing URL (Determine B).
Determine B
Stage two: Modifying the person’s account
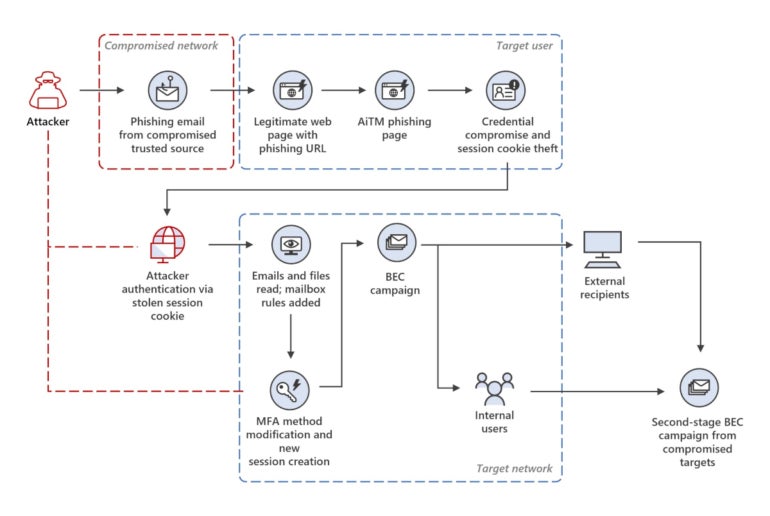
As soon as the attacker was in possession of a sound session cookie, they began accessing electronic mail conversations and paperwork hosted within the cloud and generated a brand new entry token in an effort to use the stolen session for longer.
Then, the Storm-1167 group added a brand new MFA methodology to the stolen person’s account for future use — as soon as once more displaying its issues for staying longer within the atmosphere. Since including a brand new MFA methodology doesn’t require re-authentication, the attackers quietly added OneWaySMS, an SMS-based one-time password authentication service.
The ultimate step for the attacker at this stage was to create new inbox guidelines to maneuver all incoming emails on the person’s mailbox to its archive folder and mark all of the emails as learn.
Stage three: BEC marketing campaign begins
Subsequent, the attacker — in full management of the goal’s mailbox — initiated an enormous phishing marketing campaign of greater than 16,000 emails, specializing in the person’s contacts and distribution lists, all of which have been recognized in earlier electronic mail threads from the person’s mailbox.
After the phishing emails have been despatched, the attacker monitored the mailbox and responded to the recipients, who answered with doubts in regards to the phishing electronic mail, to falsely affirm that the e-mail was reliable. Undelivered and out-of-office replies have been deleted.
This whole exercise enabled the attacker to gather extra legitimate electronic mail accounts in several organizations and in addition provoke the BEC fraud (Determine C).
Determine C
Whereas Microsoft doesn’t go additional in explaining the BEC fraud from the menace actor, it’s anticipated at this level that the actor would impersonate one of many folks concerned in common cash switch operations to have the sufferer ship the cash to a cybercriminal-owned banking account.
The right way to keep secure from this cybersecurity menace
Because the preliminary assault vector is a phishing electronic mail, it’s essential to deploy mailbox safety options that may detect phishing makes an attempt and lift alerts on emails coming from outdoors of the corporate after they comply with suspicious behavioral patterns.
Electronic mail field configuration adjustments must also be fastidiously monitored. Electronic mail bins abruptly beginning to ship an enormous variety of emails or abruptly forwarding lots of emails to a different electronic mail tackle ought to increase alerts and be analyzed fastidiously.
When attainable, electronic mail entry needs to be restricted to trusted IP addresses through company digital personal networks, for instance; MFA needs to be deployed on these companies. In case such restrictions can’t be deployed, cautious monitoring of each sign-in operation needs to be performed to detect any makes an attempt that present anomalies.
SEE: Finest VPNs for small companies in 2023 (TechRepublic)
Deploying safety options that allow the profiling of customers can also be advisable. Any uncommon attribute of a sign-in operation from a person will increase alerts and could be analyzed with such options.
As for the BEC fraud, any change concerning cash transactions needs to be fastidiously investigated. If a trusted accomplice abruptly asks to vary a wire switch vacation spot, the request needs to be investigated with that accomplice by way of a communication channel aside from electronic mail, and ideally not utilizing computer systems — maybe telephones as an alternative — in case the attacker planted malware on the goal’s laptop and will intercept all communications.
Disclosure: I work for Development Micro, however the views expressed on this article are mine.
[ad_2]