
[ad_1]
If you happen to function a cybercrime enterprise that depends on disseminating malicious software program, you most likely additionally spend a great deal of time attempting to disguise or “crypt” your malware in order that it seems benign to antivirus and safety merchandise. In reality, the method of “crypting” malware is sufficiently advanced and time-consuming that almost all critical cybercrooks will outsource this essential perform to a handful of trusted third events. This story explores the historical past and id behind Cryptor[.]biz, a long-running crypting service that’s trusted by a few of the greatest names in cybercrime.
Just about all malware that’s deployed to be used in knowledge stealing in some unspecified time in the future must be crypted. This extremely technical, laborious course of entails iteratively altering the looks and conduct of a malicious file till it now not units off alarm bells when scanned by completely different antivirus instruments.
Skilled malware purveyors perceive that in the event that they’re not constantly crypting their malware earlier than sending it out, then much more of no matter digital illness they’re attempting to unfold goes to get flagged by safety instruments. In brief, if you’re operating a cybercrime enterprise and also you’re not outfitted to deal with this crypting course of your self, you most likely must pay another person to do it for you.
Because of the excessive demand for dependable crypting providers, there are numerous cybercriminals who’ve frolicked their shingles as crypting service suppliers. Nonetheless, most of those folks don’t look like excellent at what they do, as a result of most are quickly out of enterprise.
One standout is Cryptor[.]biz. This service is definitely really helpful by the purveyors of the RedLine data stealer malware, which is a well-liked and highly effective malware package that focuses on stealing sufferer knowledge and is usually used to put the groundwork for ransomware assaults. Cryptor[.]biz additionally has been really helpful to prospects of the Vidar data stealer malware household (through the malware’s Telegram help channels).
WHO RUNS CRYPTOR[.]BIZ?
Pretty much as good as Cryptor[.]biz could also be at obfuscating malware, its proprietor doesn’t seem to have executed a terrific job masking his personal tracks. The registration data for the web site Cryptor[.]biz are hidden behind privateness safety providers, however the website’s homepage says potential prospects ought to register by visiting the area crypt[.]guru, or by sending a Jabber prompt message to the tackle “masscrypt@exploit.im.”
Crypt[.]guru’s registration data are also hidden, but passive area identify system (DNS) data for each cryptor[.]biz and crypt[.]guru present that in 2018 the domains had been forwarding incoming e-mail to the tackle obelisk57@gmail.com.
Cyber intelligence agency Intel 471 reviews that obelisk57@gmail.com was used to register an account on the discussion board Blacksoftware beneath the nickname “Kerens.” In the meantime, the Jabber tackle masscrypt@exploit.im has been related to the consumer Kerens on the Russian hacking discussion board Exploit from 2011 to the current day.
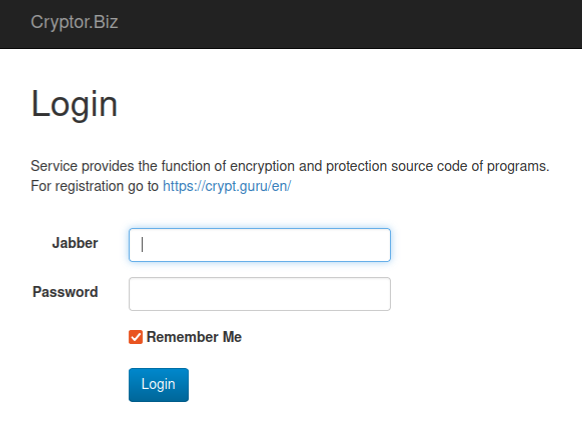
The login web page for Cryptor dot biz accommodates a number of clues about who runs the service.
The very first publish by Kerens on Exploit in 2011 was a damaging overview of a well-liked crypting service that predated Cryptor[.]biz known as VIP Crypt, which Kerens accused of being “shitty” and unreliable. However Intel 471 finds that after his essential overview of VIP Crypt, Kerens didn’t publish publicly on Exploit once more for an additional 4 years till October 2016, after they all of the sudden started promoting Cryptor[.]biz.
Intel 471 discovered that Kerens used the e-mail tackle pepyak@gmail.com, which additionally was used to register Kerens accounts on the Russian language hacking boards Verified and Damagelab.
Mockingly, Verified has itself been hacked a number of instances over time, with its personal messages and consumer registration particulars leaked on-line. These data point out the consumer Kerens registered on Verified in March 2009 from an Web tackle in Novosibirsk, a metropolis within the southern Siberian area of Russia.
In 2010, somebody with the username Pepyak on the Russian language affiliate discussion board GoFuckBiz[.]com shared that they usually cut up their time through the yr between dwelling in Siberia (through the milder months) and Thailand (when Novosibirsk is often -15 °C/°5F).
For instance, in a single dialog about the perfect automobile to purchase for navigating shoddy roads, Pepyak declared, “We’ve shitty roads in Siberia.” In January 2010, Pepyak requested the GoFuckBiz neighborhood the place one may discover a good USB-based modem in Phuket, Thailand.
DomainTools.com says the e-mail tackle pepyak@gmail.com was used to register 28 domains over time, together with a now-defunct Russian vehicle gross sales web site known as “autodoska[.]biz.” DomainTools reveals this web site was registered in 2008 to a Yuri Churnov from Sevastpol, Crimea (previous to Russia’s annexation of Crimea in 2014, the peninsula was a part of Ukraine).
The WHOIS data for autodoska[.]biz had been modified in 2010 to Sergey Purtov (pepyak@gmail.com) from Yurga, a city in Russia’s Kemerovo Oblast, which is a comparatively populous space in Western Siberia that’s adjoining to Novosibirsk.
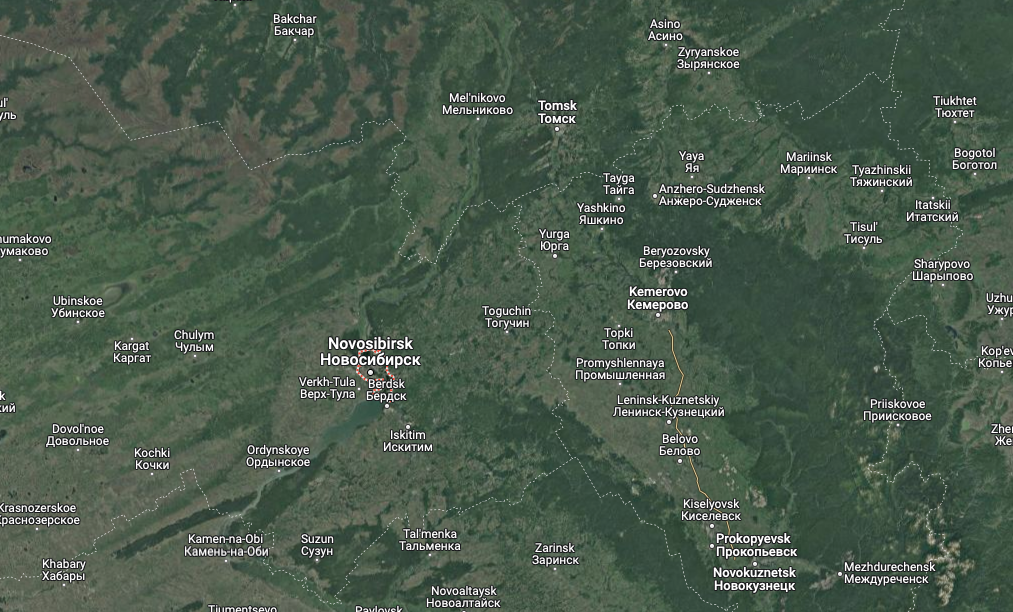
A satellite tv for pc view of the area together with Novosibirsk, Yurga and Kemerovo Oblast. Picture: Google Maps.
Most of the 28 domains registered to pepyak@gmail.com have one other e-mail tackle of their registration data: unforgiven57@mail.ru. Based on DomainTools, the Unforgiven e-mail tackle was used to register roughly a dozen domains, together with three that had been initially registered to Keren’s e-mail tackle — pepyak@gmail.com (e.g., antivirusxp09[.]com).
One of many domains registered in 2006 to the tackle unforgiven57@mail.ru was thelib[.]ru, which for a few years was a spot to obtain pirated e-books. DomainTools says thelib[.]ru was initially registered to a Sergey U Purtov.
A lot of the two-dozen domains registered to pepyak@gmail.com shared a server at one level with a small variety of different domains, together with mobile-soft[.]su, which was registered to the e-mail tackle spurtov@gmail.com.
CDEK, an specific supply firm primarily based in Novosibirsk, was apparently hacked in some unspecified time in the future as a result of cyber intelligence agency Constella Intelligence discovered that its database reveals the e-mail tackle spurtov@gmail.com was assigned to a Sergey Yurievich Purtov (Сергей Юрьевич Пуртов).
DomainTools says the identical cellphone quantity within the registration data for autodoska[.]biz (+7.9235059268) was used to safe two different domains — bile[.]ru and thelibrary[.]ru, each of which had been registered to a Sergey Y Purtov.
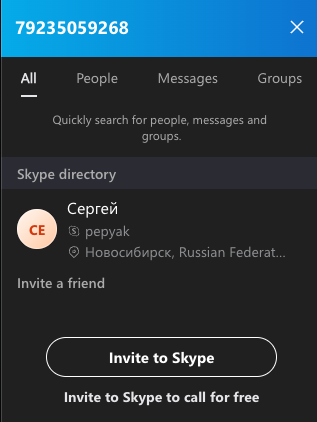 A search on the cellphone quantity 79235059268 in Skype reveals these digits belong to a “Sergey” from Novosibirsk with the now-familiar username — Pepyak.
A search on the cellphone quantity 79235059268 in Skype reveals these digits belong to a “Sergey” from Novosibirsk with the now-familiar username — Pepyak.
Bringing issues full circle, Constella Intelligence reveals that varied on-line accounts tied to the e-mail tackle unforgiven57@mail.ru continuously relied on the considerably distinctive password, “plk139t51z.” Constella says that very same password was used for only a handful of different e-mail addresses, together with gumboldt@gmail.com.
Hacked buyer data from CDEK present gumboldt@gmail.com was tied to a buyer named Sergey Yurievich Purtov. DomainTools discovered that nearly the entire 15 domains registered to gumboldt@gmail.com (together with the aforementioned mobile-soft[.]su) had been at one level registered to spurtov@gmail.com.
Intel 471 reviews that gumboldt@gmail.com was utilized in 2009 to register a consumer by the nickname “Kolumb” on the Russian hacking discussion board Antichat. From Kolumb’s posts on Antichat, it appears this consumer was largely concerned about shopping for entry to compromised computer systems within Russia.
Then in December 2009, Kolumb mentioned they had been in determined want of a dependable crypting service or full-time cryptor.
“We’d like an individual who will crypt software program on daily basis, generally even a few instances a day,” Kolumb wrote on Antichat.
Mr. Purtov didn’t reply to requests for remark despatched to any of the e-mail addresses referenced on this report. Mail.ru responded that the e-mail tackle spurtov@mail.ru is now not lively.
ANALYSIS
As KrebsOnSecurity opined on Mastodon earlier this week, it makes numerous sense for cybersecurity researchers and regulation enforcement alike to focus consideration on the highest gamers within the crypting area — for a number of causes. Most critically, the cybercriminals providing time-tested crypting providers additionally are typically among the many most skilled and related malicious coders on the planet.
Consider it this manner: By definition, a crypting service scans and examines all varieties of malware earlier than these new nasties are first set free within the wild. This reality alone ought to make these felony enterprises a major goal of cybersecurity companies seeking to achieve extra well timed intelligence about new malware.
Additionally, a overview of numerous posts and personal messages from Pepyak and different crypting suppliers reveals {that a} profitable crypting service could have direct and frequent contact with a few of the world’s most superior malware authors.
In brief, infiltrating or disrupting a trusted crypting service may be a superb strategy to decelerate and even sideline a lot of cybercrime operations unexpectedly.
Additional studying on the crypting business:
This Service Helps Malware Authors Repair Flaws in Their Code
Antivirus is Lifeless: Lengthy Stay Antivirus!
[ad_2]