
[ad_1]
ESET researchers found a Ballistic Bobcat marketing campaign concentrating on varied entities in Brazil, Israel, and the United Arab Emirates, utilizing a novel backdoor we’ve got named Sponsor.
We found Sponsor after we analyzed an fascinating pattern we detected on a sufferer’s system in Israel in Might 2022 and scoped the victim-set by nation. Upon examination, it grew to become evident to us that the pattern was a novel backdoor deployed by the Ballistic Bobcat APT group.
Ballistic Bobcat, beforehand tracked by ESET Analysis as APT35/APT42 (aka Charming Kitten, TA453, or PHOSPHORUS), is a suspected Iran-aligned superior persistent risk group that targets training, authorities, and healthcare organizations, in addition to human rights activists and journalists. It’s most energetic in Israel, the Center East, and the US. Notably, through the pandemic, it was concentrating on COVID-19-related organizations, together with the World Well being Group and Gilead Prescribed drugs, and medical analysis personnel.
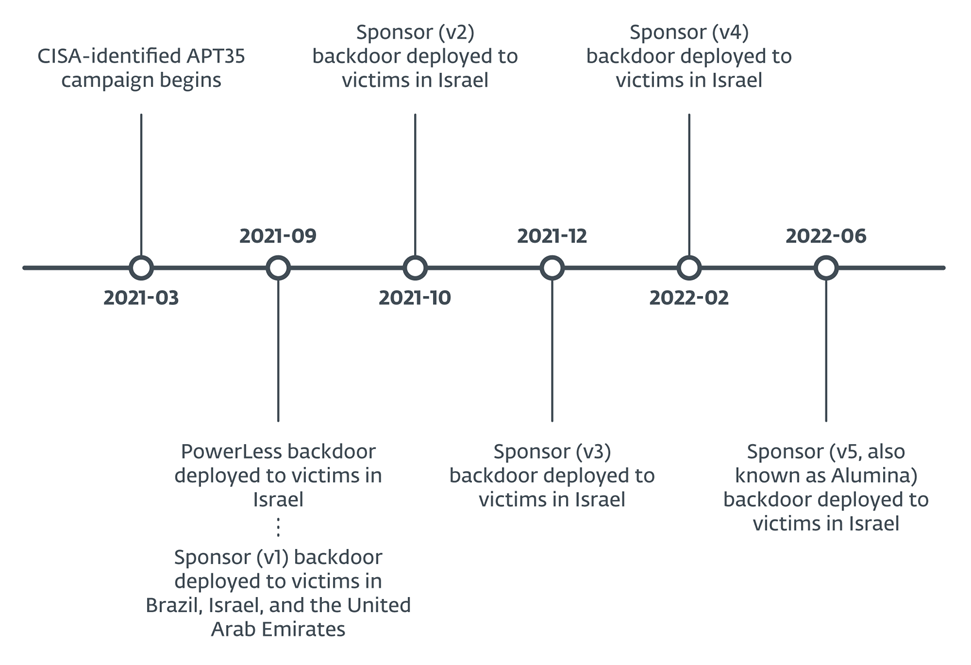
Overlaps between Ballistic Bobcat campaigns and Sponsor backdoor variations present a reasonably clear sample of software improvement and deployment, with narrowly focused campaigns, every of restricted period. We subsequently found 4 different variations of the Sponsor backdoor. In whole, we noticed Sponsor deployed to a minimum of 34 victims in Brazil, Israel, and the United Arab Emirates, as outlined in Determine 1.
Key factors of this blogpost:
- We found a brand new backdoor deployed by Ballistic Bobcat that we subsequently named Sponsor.
- Ballistic Bobcat deployed the brand new backdoor in September 2021, whereas it was wrapping up the marketing campaign documented in CISA Alert AA21-321A and the PowerLess marketing campaign.
- The Sponsor backdoor makes use of configuration recordsdata saved on disk. These recordsdata are discreetly deployed by batch recordsdata and intentionally designed to seem innocuous, thereby making an attempt to evade detection by scanning engines.
- Sponsor was deployed to a minimum of 34 victims in Brazil, Israel, and the United Arab Emirates; we’ve got named this exercise the Sponsoring Entry marketing campaign.
Preliminary entry
Ballistic Bobcat obtained preliminary entry by exploiting identified vulnerabilities in internet-exposed Microsoft Alternate servers by first conducting meticulous scans of the system or community to determine potential weaknesses or vulnerabilities, and subsequently concentrating on and exploiting these recognized weaknesses. The group has been identified to interact on this conduct for a while. Nevertheless, lots of the 34 victims recognized in ESET telemetry may greatest be described as victims of alternative slightly than preselected and researched victims, as we suspect Ballistic Bobcat engaged within the above-described scan-and-exploit conduct as a result of it was not the one risk actor with entry to those programs. We now have named this Ballistic Bobcat exercise using the Sponsor backdoor the Sponsoring Entry marketing campaign.
The Sponsor backdoor makes use of configuration recordsdata on disk, dropped by batch recordsdata, and each are innocuous in order to bypass scanning engines. This modular strategy is one which Ballistic Bobcat has used very often and with modest success up to now two and a half years. On compromised programs, Ballistic Bobcat additionally continues to make use of quite a lot of open-source instruments, which we describe – along with the Sponsor backdoor – on this blogpost.
Victimology

A major majority of the 34 victims had been positioned in Israel, with solely two positioned in different nations:
- Brazil, at a medical cooperative and medical health insurance operator, and
- the United Arab Emirates, at an unidentified group.
Desk 1 describes the verticals, and organizational particulars, for victims in Israel.
Desk 1. Verticals and organizational particulars for victims in Israel
|
Vertical |
Particulars |
|
Automotive |
· An automotive firm specializing in customized modifications. · An automotive restore and upkeep firm. |
|
Communications |
· An Israeli media outlet. |
|
Engineering |
· A civil engineering agency. · An environmental engineering agency. · An architectural design agency. |
|
Monetary providers |
· A monetary providers firm that focuses on funding counseling. · An organization that manages royalties. |
|
Healthcare |
· A medical care supplier. |
|
Insurance coverage |
· An insurance coverage firm that operates an insurance coverage market. · A business insurance coverage firm. |
|
Legislation |
· A agency specializing in medical legislation. |
|
Manufacturing |
· A number of electronics manufacturing corporations. · An organization that manufactures metal-based business merchandise. · A multinational expertise manufacturing firm. |
|
Retail |
· A meals retailer. · A multinational diamond retailer. · A skincare merchandise retailer. · A window therapy retailer and installer. · A world digital components provider. · A bodily entry management provider. |
|
Expertise |
· An IT providers expertise firm. · An IT options supplier. |
|
Telecommunications |
· A telecommunications firm. |
|
Unidentified |
· A number of unidentified organizations. |
Attribution
In August 2021, the Israeli sufferer above that operates an insurance coverage market was attacked by Ballistic Bobcat with the instruments CISA reported in November 2021. The symptoms of compromise we noticed are:
- MicrosoftOutlookUpdateSchedule,
- MicrosoftOutlookUpdateSchedule.xml,
- GoogleChangeManagement, and
- GoogleChangeManagement.xml.
Ballistic Bobcat instruments communicated with the identical command and management (C&C) server as within the CISA report: 162.55.137[.]20.
Then, in September 2021, the identical sufferer obtained the subsequent era of Ballistic Bobcat instruments: the PowerLess backdoor and its supporting toolset. The symptoms of compromise we noticed had been:
- http://162.55.137[.]20/gsdhdDdfgA5sS/ff/dll.dll,
- windowsprocesses.exe, and
- http://162.55.137[.]20/gsdhdDdfgA5sS/ff/windowsprocesses.exe.
On November 18th, 2021, the group then deployed one other software (Plink) that was lined within the CISA report, as MicrosoftOutLookUpdater.exe. Ten days later, on November 28th, 2021, Ballistic Bobcat deployed the Merlin agent (the agent portion of an open-source post-exploitation C&C server and agent written in Go). On disk, this Merlin agent was named googleUpdate.exe, utilizing the identical naming conference as described within the CISA report to cover in plain sight.
The Merlin agent executed a Meterpreter reverse shell that known as again to a brand new C&C server, 37.120.222[.]168:80. On December 12th, 2021, the reverse shell dropped a batch file, set up.bat, and inside minutes of executing the batch file, Ballistic Bobcat operators pushed their latest backdoor, Sponsor. This is able to change into the third model of the backdoor.
Technical evaluation
Preliminary entry
We had been capable of determine a possible technique of preliminary entry for 23 of the 34 victims that we noticed in ESET telemetry. Much like what was reported within the PowerLess and CISA stories, Ballistic Bobcat most likely exploited a identified vulnerability, CVE-2021-26855, in Microsoft Alternate servers to realize a foothold on these programs.
For 16 of the 34 victims, it seems Ballistic Bobcat was not the one risk actor with entry to their programs. This will likely point out, together with the wide range of victims and the obvious lack of apparent intelligence worth of some victims, that Ballistic Bobcat engaged in scan-and-exploit conduct, versus a focused marketing campaign towards preselected victims.
Toolset
Open-source instruments
Ballistic Bobcat employed quite a few open-source instruments through the Sponsoring Entry marketing campaign. These instruments and their capabilities are listed in Desk 2.
Desk 2. Open-source instruments utilized by Ballistic Bobcat
|
Filename |
Description |
host2ip.exe
|
Maps a hostname to an IP deal with throughout the native community. |
CSRSS.EXE
|
RevSocks, a reverse tunnel software. |
mi.exe
|
Mimikatz, with an authentic filename of midongle.exe and filled with the Armadillo PE packer. |
gost.exe
|
GO Easy Tunnel (GOST), a tunneling software written in Go. |
chisel.exe
|
Chisel, a TCP/UDP tunnel over HTTP utilizing SSH layers. |
csrss_protected.exe
|
RevSocks tunnel, protected with the trial model of the Enigma Protector software program safety. |
plink.exe
|
Plink (PuTTY Hyperlink), a command line connection software. |
|
WebBrowserPassView.exe
|
A password restoration software for passwords saved in net browsers.
|
sqlextractor.exe
|
A software for interacting with, and extracting information from, SQL databases. |
procdump64.exe
|
ProcDump, a Sysinternals command line utility for monitoring functions and producing crash dumps. |
Batch recordsdata
Ballistic Bobcat deployed batch recordsdata to victims’ programs moments earlier than deploying the Sponsor backdoor. File paths we’re conscious of are:
- C:inetpubwwwrootaspnet_clientInstall.bat
- %USERPROFILEpercentDesktopInstall.bat
- %WINDOWSpercentTasksInstall.bat
Sadly, we had been unable to acquire any of those batch recordsdata. Nevertheless, we imagine they write innocuous configuration recordsdata to disk, which the Sponsor backdoor requires to perform absolutely. These configuration filenames had been taken from the Sponsor backdoors however had been by no means collected:
- config.txt
- node.txt
- error.txt
- Uninstall.bat
We imagine that the batch recordsdata and configuration recordsdata are a part of the modular improvement course of that Ballistic Bobcat has favored over the previous few years.
Sponsor backdoor
Sponsor backdoors are written in C++ with compilation timestamps and Program Database (PDB) paths as proven in Desk 3. A word on model numbers: the column Model represents the model that we observe internally based mostly on the linear development of Sponsor backdoors the place modifications are comprised of one model to the subsequent. The Inner model column incorporates the model numbers noticed in every Sponsor backdoor and are included for ease of comparability when analyzing these and different potential Sponsor samples.
Desk 3. Sponsor compilation timestamps and PDBs
|
Model |
Inner model |
Compilation timestamp |
PDB |
|
1 |
1.0.0 |
2021-08-29 09:12:51 |
D:TempBD_Plus_SrvcReleaseBD_Plus_Srvc.pdb |
|
2 |
1.0.0 |
2021-10-09 12:39:15 |
D:TempSponsorReleaseSponsor.pdb |
|
3 |
1.4.0 |
2021-11-24 11:51:55 |
D:TempSponsorReleaseSponsor.pdb |
|
4 |
2.1.1 |
2022-02-19 13:12:07 |
D:TempSponsorReleaseSponsor.pdb |
|
5 |
1.2.3.0 |
2022-06-19 14:14:13 |
D:TempAluminaReleaseAlumina.pdb |
The preliminary execution of Sponsor requires the runtime argument set up, with out which Sponsor gracefully exits, doubtless a easy anti-emulation/anti-sandbox approach. If handed that argument, Sponsor creates a service known as SystemNetwork (in v1) and Replace (in all the opposite variations). It units the service’s Startup Kind to Automated, and units it to run its personal Sponsor course of, and grants it full entry. It then begins the service.
Sponsor, now operating as a service, makes an attempt to open the aforementioned configuration recordsdata beforehand positioned on disk. It seems for config.txt and node.txt, each within the present working listing. If the primary is lacking, Sponsor units the service to Stopped and gracefully exits.
Backdoor configuration
Sponsor’s configuration, saved in config.txt, incorporates two fields:
- An replace interval, in seconds, to periodically contact the C&C server for instructions.
- A listing of C&C servers, known as relays in Sponsor’s binaries.
The C&C servers are saved encrypted (RC4), and the decryption secret is current within the first line of config.txt. Every of the fields, together with the decryption key, have the format proven in Determine 3.
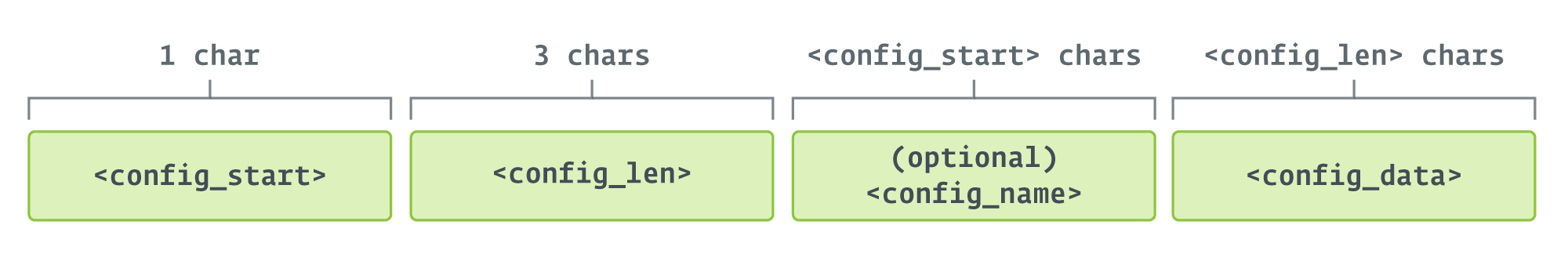
These subfields are:
- config_start: signifies the size of config_name, if current, or zero, if not. Utilized by the backdoor to know the place config_data begins.
- config_len: size of config_data.
- config_name: optionally available, incorporates a reputation given to the configuration area.
- config_data: the configuration itself, encrypted (within the case of C&C servers) or not (all the opposite fields).
Determine 4 reveals an instance with color-coded contents of a doable config.txt file. Notice that this isn’t an precise file we noticed, however a fabricated instance.
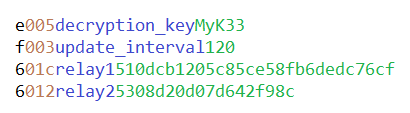
The final two fields in config.txt are encrypted with RC4, utilizing the string illustration of the SHA-256 hash of the required decryption key, as the important thing to encrypt the information. We see that the encrypted bytes are saved hex-encoded as ASCII textual content.
Host data gathering
Sponsor gathers details about the host on which it’s operating, stories all the gathered data to the C&C server, and receives a node ID, which is written to node.txt. Desk 4 lists keys and values within the Home windows registry that Sponsor makes use of to get the knowledge, and offers an instance of the information collected.
Desk 4. Data gathered by Sponsor
|
Registry key |
Worth |
Instance |
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetServicesTcpipParameters
|
Hostname
|
D-835MK12
|
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlTimeZoneInformation
|
TimeZoneKeyName
|
Israel Commonplace Time
|
HKEY_USERS.DEFAULTControl PanelInternational
|
LocaleName
|
he-IL
|
HKEY_LOCAL_MACHINEHARDWAREDESCRIPTIONSystemBIOS
|
BaseBoardProduct
|
10NX0010IL
|
HKEY_LOCAL_MACHINEHARDWAREDESCRIPTIONSystemCentralProcessor�
|
ProcessorNameString
|
Intel(R) Core(TM) i7-8565U CPU @ 1.80GHz
|
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersion
|
ProductName
|
Home windows 10 Enterprise N
|
CurrentVersion
|
6.3
|
|
CurrentBuildNumber
|
19044
|
|
InstallationType
|
Shopper
|
Sponsor additionally collects the host’s Home windows area by utilizing the next WMIC command:
wmic computersystem get area
Lastly, Sponsor makes use of Home windows APIs to gather the present username (GetUserNameW), decide if the present Sponsor course of is operating as a 32- or 64-bit software (GetCurrentProcess, then IsWow64Process(CurrentProcess)), and determines whether or not the system is operating on battery energy or related to an AC or DC energy supply (GetSystemPowerStatus).
One oddity relating to the 32- or 64-bit software test is that every one noticed samples of Sponsor had been 32-bit. This might imply that a few of the subsequent stage instruments require this data.
The collected data is shipped in a base64-encoded message that, earlier than encoding, begins with r and has the format proven in Determine 5.
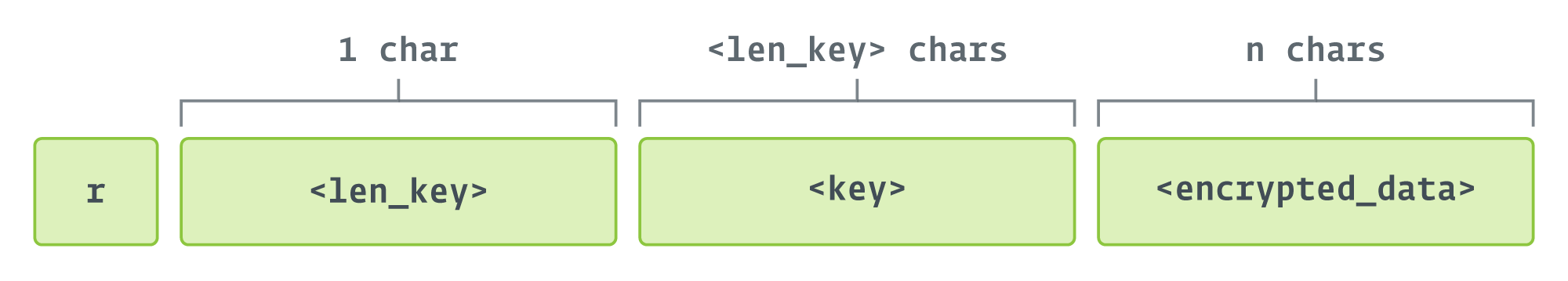
The knowledge is encrypted with RC4, and the encryption secret is a random quantity generated on the spot. The bottom line is hashed with the MD5 algorithm, not SHA-256 as beforehand talked about. That is the case for all communications the place Sponsor has to ship encrypted information.
The C&C server replies with a quantity used to determine the victimized pc in later communications, which is written to node.txt. Notice that the C&C server is randomly chosen from the record when the r message is shipped, and the identical server is utilized in all subsequent communications.
Command processing loop
Sponsor requests instructions in a loop, sleeping based on the interval outlined in config.txt. The steps are:
- Ship a chk=Take a look at message repeatedly, till the C&C server replies Okay.
- Ship a c (IS_CMD_AVAIL) message to the C&C server, and obtain an operator command.
- Course of the command.
- If there may be output to be despatched to the C&C server, ship an a (ACK) message, together with the output (encrypted), or
- If execution failed, ship an f
(FAILED) message. The error message shouldn’t be despatched.
- Sleep.
The c message is shipped to request a command to execute, and has the format (earlier than base64 encoding) proven in Determine 6.
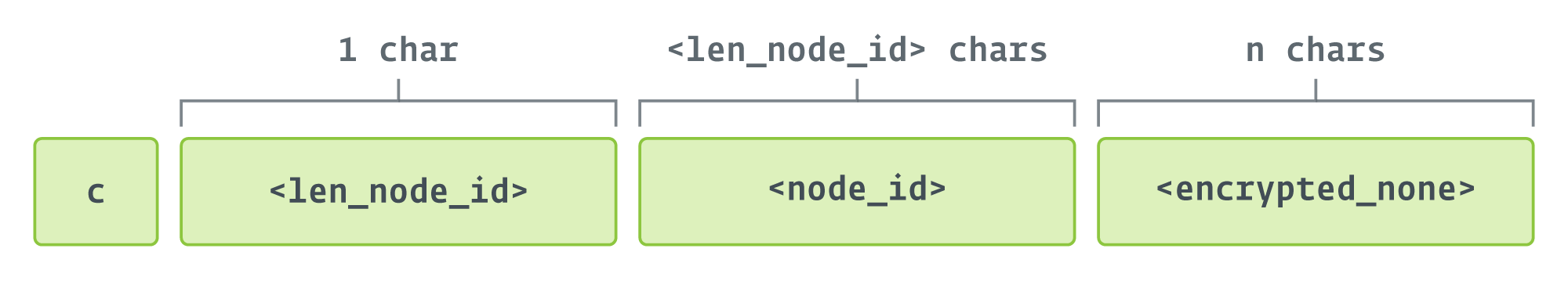
The encrypted_none area within the determine is the results of encrypting the hardcoded string None with RC4. The important thing for encryption is the MD5 hash of node_id.
The URL used to contact the C&C server is constructed as: http://<IP_or_domain>:80. This will likely point out that 37.120.222[.]168:80 is the one C&C server used all through the Sponsoring Entry marketing campaign, because it was the one IP deal with we noticed sufferer machines reaching out to on port 80.
Operator instructions
Operator instructions are delineated in Desk 5 and seem within the order wherein they’re discovered within the code. Communication with the C&C server happens over port 80.
Desk 5. Operator instructions and descriptions
|
Command |
Description |
|
p |
Sends the method ID for the operating Sponsor course of. |
|
e |
Executes a command, as laid out in a subsequent further argument, on the Sponsor host utilizing the next string: c:windowssystem32cmd.exe /c <cmd> > end result.txt 2>&1 Outcomes are saved in end result.txt within the present working listing. Sends an a message with the encrypted output to the C&C server if efficiently executed. If failed, sends an f message (with out specifying the error). |
|
d |
Receives a file from the C&C server and executes it. This command has many arguments: the goal filename to put in writing the file into, the MD5 hash of the file, a listing to put in writing the file to (or the present working listing, by default), a Boolean to point whether or not to run the file or not, and the contents of the executable file, base64-encoded. If no errors happen, an a message is shipped to the C&C server with Add and execute file efficiently or Add file efficiently with out execute (encrypted). If errors happen throughout execution of the file, an f message is shipped. If the MD5 hash of the contents of the file doesn’t match the supplied hash, an e (CRC_ERROR) message is shipped to the C&C server (together with solely the encryption key used, and no different data). Using the time period Add right here is probably complicated because the Ballistic Bobcat operators and coders take the viewpoint from the server aspect, whereas many may view this as a obtain based mostly on the pulling of the file (i.e., downloading it) by the system utilizing the Sponsor backdoor. |
|
u |
Makes an attempt to obtain a file utilizing the URLDownloadFileW Home windows API and execute it. Success sends an a message with the encryption key used, and no different data. Failure sends an f message with the same construction. |
|
s |
Executes a file already on disk, Uninstall.bat within the present working listing, that more than likely incorporates instructions to delete recordsdata associated to the backdoor. |
|
n |
This command may be explicitly equipped by an operator or may be inferred by Sponsor because the command to execute within the absence of some other command. Referred to inside Sponsor as NO_CMD, it executes a randomized sleep earlier than checking again in with the C&C server. |
|
b |
Updates the record of C&Cs saved in config.txt within the present working listing. The brand new C&C addresses exchange the earlier ones; they aren’t added to the record. It sends an a message with |
|
i |
Updates the predetermined check-in interval laid out in config.txt. It sends an a message with New interval changed efficiently to the C&C server if efficiently up to date. |
Updates to Sponsor
Ballistic Bobcat coders made code revisions between Sponsor v1 and v2. The 2 most vital modifications within the latter are:
- Optimization of code the place a number of longer capabilities had been minimized into capabilities and subfunctions, and
- Disguising Sponsor as an updater program by together with the next message within the service configuration:
App updates are nice for each app customers and apps – updates imply that builders are at all times engaged on bettering the app, conserving in thoughts a greater buyer expertise with every replace.
Community infrastructure
Along with piggybacking on the C&C infrastructure used within the PowerLess marketing campaign, Ballistic Bobcat additionally launched a brand new C&C server. The group additionally utilized a number of IPs to retailer and ship assist instruments through the Sponsoring Entry marketing campaign. We now have confirmed that none of those IPs are in operation presently.
Conclusion
Ballistic Bobcat continues to function on a scan-and-exploit mannequin, on the lookout for targets of alternative with unpatched vulnerabilities in internet-exposed Microsoft Alternate servers. The group continues to make use of a various open-source toolset supplemented with a number of customized functions, together with its Sponsor backdoor. Defenders can be nicely suggested to patch any internet-exposed gadgets and stay vigilant for brand new functions popping up inside their organizations.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.com.
ESET Analysis presents non-public APT intelligence stories and information feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IoCs
Recordsdata
|
SHA-1 |
Filename |
Detection |
Description |
098B9A6CE722311553E1D8AC5849BA1DC5834C52
|
N/A |
Win32/Agent.UXG |
Ballistic Bobcat backdoor, Sponsor (v1). |
5AEE3C957056A8640041ABC108D0B8A3D7A02EBD
|
N/A |
Win32/Agent.UXG |
Ballistic Bobcat backdoor, Sponsor (v2). |
764EB6CA3752576C182FC19CFF3E86C38DD51475
|
N/A |
Win32/Agent.UXG |
Ballistic Bobcat backdoor, Sponsor (v3). |
2F3EDA9D788A35F4C467B63860E73C3B010529CC
|
N/A |
Win32/Agent.UXG |
Ballistic Bobcat backdoor, Sponsor (v4). |
E443DC53284537513C00818392E569C79328F56F
|
N/A |
Win32/Agent.UXG |
Ballistic Bobcat backdoor, Sponsor (v5, aka Alumina). |
C4BC1A5A02F8AC3CF642880DC1FC3B1E46E4DA61
|
N/A |
WinGo/Agent.BT |
RevSocks reverse tunnel. |
39AE8BA8C5280A09BA638DF4C9D64AC0F3F706B6
|
N/A |
clear |
ProcDump, a command line utility for monitoring functions and producing crash dumps. |
A200BE662CDC0ECE2A2C8FC4DBBC8C574D31848A
|
N/A |
Generik.EYWYQYF |
Mimikatz. |
5D60C8507AC9B840A13FFDF19E3315A3E14DE66A
|
N/A |
WinGo/Riskware.Gost.D |
GO Easy Tunnel (GOST). |
50CFB3CF1A0FE5EC2264ACE53F96FADFE99CC617
|
N/A |
WinGo/HackTool.Chisel.A |
Chisel reverse tunnel. |
1AAE62ACEE3C04A6728F9EDC3756FABD6E342252
|
N/A |
N/A |
Host2IP discovery software. |
519CA93366F1B1D71052C6CE140F5C80CE885181
|
N/A |
Win64/Packed.Enigma.BV |
RevSocks tunnel, protected with the trial model of the Enigma Protector software program safety. |
4709827C7A95012AB970BF651ED5183083366C79
|
N/A |
N/A |
Plink (PuTTY Hyperlink), a command line connection software. |
99C7B5827DF89B4FAFC2B565ABED97C58A3C65B8
|
N/A |
Win32/PSWTool.WebBrowserPassView.I |
A password restoration software for passwords saved in net browsers. |
E52AA118A59502790A4DD6625854BD93C0DEAF27
|
N/A |
MSIL/HackTool.SQLDump.A |
A software for interacting with, and extracting information from, SQL databases. |
File paths
The next is an inventory of paths the place the Sponsor backdoor was deployed on victimized machines.
%SYSTEMDRIVEpercentinetpubwwwrootaspnet_client
%USERPROFILEpercentAppDataLocalTempfile
%USERPROFILEpercentAppDataLocalTemp2low
%USERPROFILEpercentDesktop
%USERPROFILEpercentDownloadsa
%WINDIR%
%WINDIRpercentINFMSExchange Supply DSN
%WINDIRpercentTasks
%WINDIRpercentTemppercentWINDIRpercentTempcrashpad1Files
Community
IP
Supplier
First seen
Final seen
Particulars
162.55.137[.]20
Hetzner On-line GMBH
2021-06-14
2021-06-15
PowerLess C&C.
37.120.222[.]168
M247 LTD
2021-11-28
2021-12-12
Sponsor C&C.
198.144.189[.]74
Colocrossing
2021-11-29
2021-11-29
Assist instruments obtain web site.
5.255.97[.]172
The Infrastructure Group B.V.
2021-09-05
2021-10-28
Assist instruments obtain web site.
IP
Supplier
First seen
Final seen
Particulars
162.55.137[.]20
Hetzner On-line GMBH
2021-06-14
2021-06-15
PowerLess C&C.
37.120.222[.]168
M247 LTD
2021-11-28
2021-12-12
Sponsor C&C.
198.144.189[.]74
Colocrossing
2021-11-29
2021-11-29
Assist instruments obtain web site.
5.255.97[.]172
The Infrastructure Group B.V.
2021-09-05
2021-10-28
Assist instruments obtain web site.
This desk was constructed utilizing model 13 of the MITRE ATT&CK framework.
|
Tactic |
ID |
Identify |
Description |
|
Reconnaissance |
Lively Scanning: Vulnerability Scanning |
Ballistic Bobcat scans for susceptible variations of Microsoft Alternate Servers to use. |
|
|
Useful resource Improvement |
Develop Capabilities: Malware |
Ballistic Bobcat designed and coded the Sponsor backdoor. |
|
|
Get hold of Capabilities: Instrument |
Ballistic Bobcat makes use of varied open-source instruments as a part of the Sponsoring Entry marketing campaign. |
||
|
Preliminary Entry |
Exploit Public-Dealing with Software |
Ballistic Bobcat targets internet-exposed Microsoft Alternate Servers. |
|
|
Execution |
Command and Scripting Interpreter: Home windows Command Shell |
The Sponsor backdoor makes use of the Home windows command shell to execute instructions on the sufferer’s system. |
|
|
System Providers: Service Execution |
The Sponsor backdoor units itself as a service and initiates its major capabilities after the service is executed. |
||
|
Persistence |
Create or Modify System Course of: Home windows Service |
Sponsor maintains persistence by making a service with computerized startup that executes its major capabilities in a loop. |
|
|
Privilege Escalation |
Legitimate Accounts: Native Accounts |
Ballistic Bobcat operators try to steal credentials of legitimate customers after initially exploiting a system earlier than deploying the Sponsor backdoor. |
|
|
Protection Evasion |
Deobfuscate/Decode Recordsdata or Data |
Sponsor shops data on disk that’s encrypted and obfuscated, and deobfuscates it at runtime. |
|
|
Obfuscated Recordsdata or Data |
Configuration recordsdata that the Sponsor backdoor requires on disk are encrypted and obfuscated. |
||
|
Legitimate Accounts: Native Accounts |
Sponsor is executed with admin privileges, doubtless utilizing credentials that operators discovered on disk; together with Ballistic Bobcat’s innocuous naming conventions, this enables Sponsor to mix into the background. |
||
|
Credential Entry |
Credentials from Password Shops: Credentials from Net Browsers |
Ballistic Bobcat operators use open-source instruments to steal credentials from password shops inside net browsers. |
|
|
Discovery |
Distant System Discovery |
Ballistic Bobcat makes use of the Host2IP software, beforehand utilized by Agrius, to find different programs inside reachable networks and correlate their hostnames and IP addresses. |
|
|
Command and Management |
Knowledge Obfuscation |
The Sponsor backdoor obfuscates information earlier than sending it to the C&C server. |
[ad_2]
