[ad_1]
Ransomware is likely one of the most important threats going through organizations in the present day. Battling it’s no simple activity, notably provided that menace actors are frequently refining their strategies and approaches. Current shifts, for instance, embrace tweaks to ransomware-as-a-service (RaaS) fashions; the adoption of recent programming languages; evolutions in concentrating on and deployment; and more and more launching assaults after enterprise hours and at weekends to hinder detection and incident response efforts.
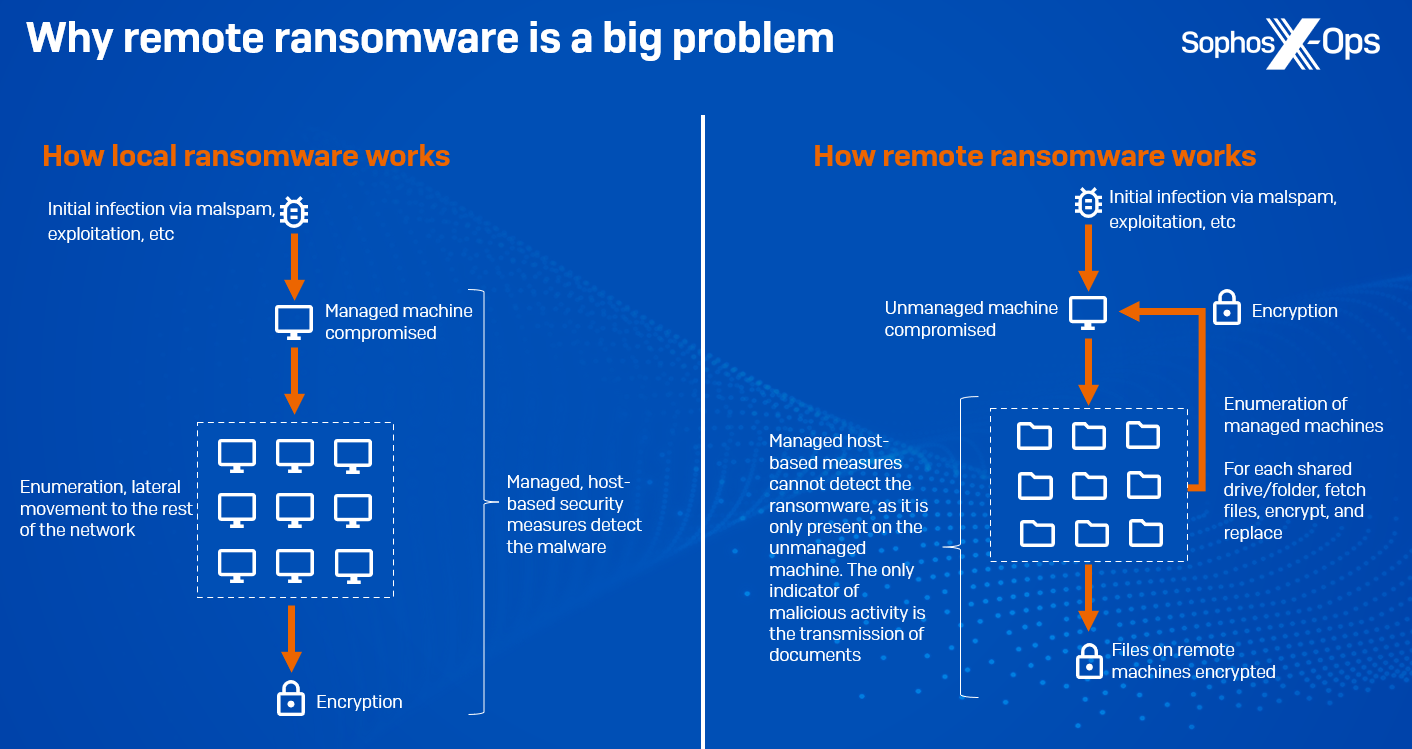
One of many extra substantial developments is a rise in distant ransomware: leveraging a corporation’s area structure to encrypt information on managed domain-joined machines. All of the malicious exercise – ingress, payload execution, and encryption – happens on an unmanaged machine, due to this fact bypassing trendy safety stacks, with the one indication of compromise being the transmission of paperwork to and from different machines. Our telemetry signifies that there was a 62% year-on-year improve in intentional distant encryption assaults since 2022. And Microsoft’s 2023 Digital Protection Report states that round 60% of human-operated ransomware assaults contain distant encryption, with 80% of all compromises originating from unmanaged gadgets, indicating a scarcity of energetic asset administration. Ransomware households recognized to help distant encryption embrace Akira, ALPHV/BlackCat, BlackMatter, LockBit, and Royal, and it’s a way that’s been round for a while – way back to 2013, CryptoLocker was concentrating on community shares.
Determine 1: A simplified rationalization of how distant ransomware works
Unsurprisingly, the rise and persevering with improvement of ransomware has led to a plethora of analysis geared toward detecting and stopping it – with teachers, safety researchers, and distributors all proposing varied options. Ransomware, as a type of malware, presents distinctive sensible and mental challenges, and the vary of options displays this. Many such options goal a number of of ransomware’s distinct behavioral traits: enumerating filesystems, accessing and encrypting information, and producing ransom notes. Others are extra generic, making use of widespread anti-malware strategies to ransomware.
On this, the second situation of our new technical thought management sequence (the primary, on reminiscence scanning, is obtainable right here), we’ll present a quick overview of a few of these strategies and their benefits and downsides, earlier than taking an in-depth have a look at our personal contribution to the sector: CryptoGuard.
Earlier than we begin, one factor to notice: a ransomware assault has a number of phases, and the vast majority of these will happen earlier than the options we focus on on this article come into play. A well-defended enterprise may have a number of layers of safety which ought to cease assaults at varied factors, which means that in lots of instances particular anti-ransomware options shouldn’t be required. However when all else fails, and a decided adversary reaches the encryption stage, we want a expertise to forestall irreparable injury. Different phases of an assault – preliminary an infection, persistence, lateral motion, and so forth – are reversible, however encryption is just not.
Anti-ransomware strategies
Static options
Static strategies (i.e., these which might be performed passively, with out requiring execution of the malware) for ransomware detection should not markedly totally different from these used to detect another form of malware. Options on this vein embrace signature-matching, evaluating strings; evaluating file operations; inspecting behavioral traits; deep studying strategies; and inspecting PE headers.
Whereas static strategies have the benefit of being comparatively speedy and low-cost, decided attackers may also evade them by modifying code till signature detections are damaged. They’re additionally much less efficient towards new variants, packers, obfuscators, and in-memory threats, in addition to distant ransomware.
Dynamic options
Dynamic options, then again, are typically extra computationally costly, however provide higher protection. Dynamic anti-ransomware options on this vein embrace the next:
Filesystem interactions
Some safety options will monitor for adjustments to file extensions, high-frequency learn/write and renaming operations, or new information which have extensions related to ransomware variants. Alternatively, some options leverage different interactions; the open-source challenge Raccine, for instance, is predicated on the premise that many ransomware variants delete shadow copies utilizing vssadmin. Raccine works by intercepting requests to vssadmin and killing the method accountable.
Since ransomware targets information, it appears logical that quite a few approaches ought to give attention to filesystem interactions. Nonetheless, a lot of them are reliant on evaluation inside a sandboxed atmosphere; are predicated on anomalous patterns which menace actors might attempt to keep away from producing; or might be resource-intensive because of the quantity of monitoring concerned (though it’s potential to dynamically adapt the diploma of monitoring) Some filesystem-based strategies may not be efficient in terms of distant ransomware.
Folder shielding
Whereas options like Managed Folder Entry (CAF) in Home windows Defender restrict entry to folders to particular purposes, such an method is primarily geared in the direction of particular person customers. CAF helps shield towards ransomware by limiting unauthorized entry to designated folders, permitting solely trusted purposes to change information inside them. Nonetheless, for enterprise networks, this technique could also be much less sensible because of the ongoing want for meticulous administration of folders and purposes. Moreover, it doesn’t handle the chance of assaults seizing management of trusted apps, a prevalent tactic in ransomware assaults
API calls
Some safety options will assess API calls invoked by a course of, both by flagging suspicious and seldom-seen calls or by figuring out doubtlessly malicious name sequences.
Most ransomware employs API calls, though some variants use evasive measures to disguise these (notably for API calls that are recognized to be suspicious, corresponding to CreateRemoteThread or VirtualAllocEx, generally utilized in course of injection; or API calls associated to encryption). Monitoring API calls on the kernel degree actually appears to be a worthwhile method, however such monitoring is resource-intensive, can generate false positives, and is difficult to implement at scale. Moreover, in terms of distant ransomware, the method itself is probably not on the host being attacked, which may frustrate this method.
Honeyfiles
Many safety merchandise make use of ‘honeyfiles’, ‘decoy information’, ‘bait information’, or ‘canary information’ as an anti-ransomware resolution – inconspicuous information that are positioned in a listing and which authentic customers are requested to not contact. A separate monitoring system, both on the user-level or the kernel-level, is triggered if these information are accessed or modified by any course of, at which level an alert is generated.
Honeyfiles are light-weight, low-effort, and may present an early warning that an assault could also be in progress. Nonetheless, they do include some caveats. Defenders should be sure that any alert is obtained and acted upon rapidly sufficient, as by design an assault will already be in progress when a honeyfile is triggered. In addition they should be strategically positioned – deep sufficient inside filesystems to make sure that regular, authentic customers and processes gained’t unintentionally journey them, however not so deep that vital paperwork are encrypted earlier than they’re accessed.
Fingerprinting
A much less widespread method is to ‘fingerprint’ sure malicious patterns – in community (C2) visitors, CPU consumption, or CPU indicators.
As regards to community visitors, it’s price noting that in trendy human-led ransomware assaults, menace actors tailor and compile the ransomware binary uniquely for every sufferer, a strategic transfer supposed to impede detection and complicate the decryption course of. This tradition-built ransomware usually incorporates a victim-specific ransom notice and is deployed in a ‘fire-and-forget’ method, omitting the necessity for direct communication again to the menace actor, because the encryption course of is self-contained inside the malware, leveraging a victim-specific embedded public key.
An rising expertise from Intel referred to as TDT (Menace Detection Know-how) affords the power to detect ransomware on the {hardware} degree. A assessment by SE Labs demonstrates a outstanding effectiveness towards a various array of encryption schemes. Nonetheless, that is confined to particular Intel CPUs, excluding ARM and AMD architectures. This limitation stems from TDT’s reliance on a machine studying mannequin educated on CPU efficiency indicators from particular ransomware households’ encryption profiles. The mannequin, educated by Intel, relies on vendor help and doesn’t work with distant encryption. A drawback of this expertise is that some ransomware strains, corresponding to LockBit and Akira, are intentionally configured to encrypt solely a portion of every file. This accelerates the impression of the assault, affecting extra information in much less time. It additionally signifies that detection by Intel TDT happens after a major variety of information have already been compromised.
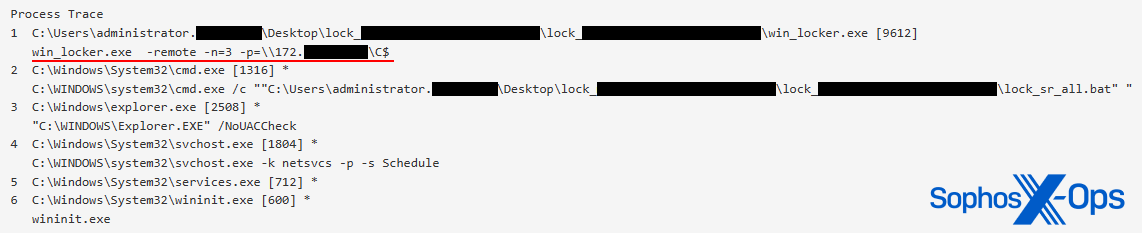
Determine 2: Akira ransomware, particularly attacking solely distant information, and encrypting solely 3% of every file
Automated telemetry-driven containment
Most trendy endpoint safety options transmit information to the cloud for incident response and alert evaluation. Nonetheless, mechanically piecing collectively the small print of an energetic human-led ransomware assault from alert telemetry can take wherever from a couple of minutes to a number of hours. This latency depends upon the configured telemetry reporting frequency, the presence of different alert indicators, and the cloud’s processing capability to assemble and correlate particular occasions from a number of protected machines.
Following detection, an automatic response can contain deploying a containment coverage to managed gadgets, to isolate a selected consumer account suspected of compromise by the attacker. Whereas this motion goals to forestall an imminent or ongoing (distant) ransomware encryption assault originating from the recognized account, you will need to notice that the distribution of this coverage additionally requires time (as much as hours). Furthermore, in situations the place the attacker begins encryption with out triggering prior alerts on managed machines (as famous above, 80% of assaults contain unmanaged machines) or opts to start the encryption course of from an alternate consumer account, the circumstances don’t all the time favour an efficient cloud-driven dynamic containment technique. However it may be useful in some cases.
Rollback
Basically, dynamic anti-ransomware options generally require some degree of encryption or information manipulation to have taken place earlier than detecting the assault. Consequently, a sure variety of information will seemingly grow to be encrypted, necessitating a backup and restore perform to get well affected information.
To revert unencrypted file variations, some endpoint safety merchandise leverage Quantity Shadow Copies, a Home windows function that generates information snapshots at particular time factors. These ‘shadow copies’ seize file or quantity states, even whereas they’re in use. However, this technique has its limitations: attackers generally delete the shadow copies; they don’t shield information on community mapped drives; and efficient rollback depends on detecting and addressing the ransomware incident earlier than the next scheduled snapshot (which usually happens each 4 hours). And, as famous beforehand, most assaults occur after workplace hours, which may complicate restoration makes an attempt utilizing this technique.
Abstract
Usually, many of those approaches give attention to searching for ‘badness’: characterizing and figuring out behavioral traits that are indicative of ransomware exercise. Whereas this looks as if a rational determination, it does have a vital weak spot, in that menace actors have an incentive to disguise or obfuscate these traits and due to this fact evade detection. CryptoGuard, then again, takes a special method.
CryptoGuard
CryptoGuard – previously generally known as HitmanPro.Alert, and a part of Intercept X since 2016 – was first developed in 2013, and is meant to be a final layer of defence towards each native and distant ransomware, when decided menace actors have evaded all different protections and are ready to start encryption. Its notable successes embrace blocking WannaCry, LockBit, and REvil ransomware. Whereas we hold a really watchful eye on developments within the ransomware house, CryptoGuard hasn’t modified considerably over time, primarily as a result of it hasn’t wanted to.
An uneven method
In contrast to the vast majority of the approaches described above, CryptoGuard doesn’t search for attackers, ransomware executables, or malicious behavioral patterns in any respect. Different safety options, together with Sophos merchandise, do these items, in fact – it’s a elementary a part of a layered defence, which ideally prevents attackers from attending to the encryption stage – however CryptoGuard itself employs a extra uneven method, for when these layers have been circumvented.
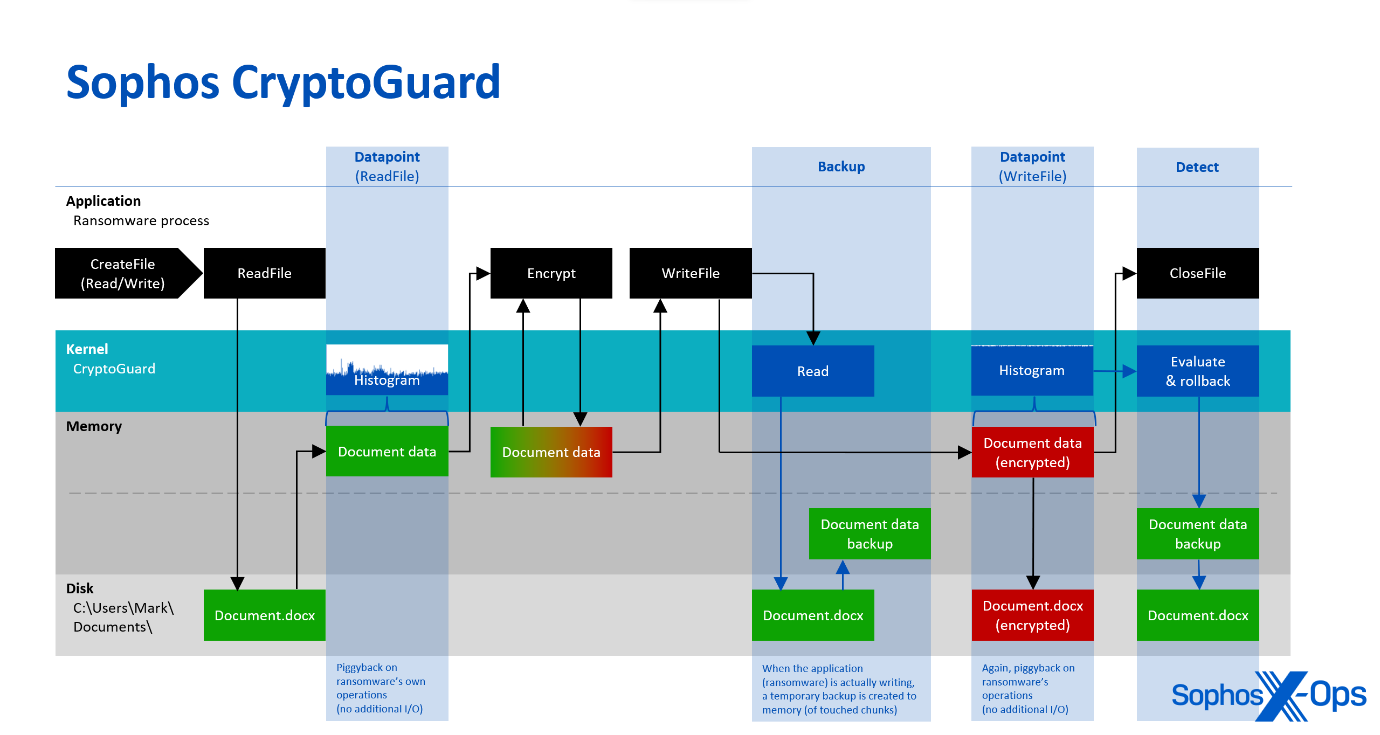
Relatively than searching for ‘badness,’ CryptoGuard focuses on the contents of information, by analyzing their patterns with a mathematical algorithm. Each time a course of opens a file for studying and writing, CryptoGuard’s minifilter driver – which operates inside the Home windows working system kernel – repeatedly generates histograms of the learn and written information. These histograms serve to know the general sample and traits of the info. They bear analysis to find out their entropy and statistically analyze whether or not the learn and written information is unencrypted, compressed, or encrypted. The built-in evaluators make use of mathematical fashions to categorise information. For the reason that evaluation makes use of the identical reminiscence buffers offered by the working system for the requesting course of, it is extremely environment friendly because it doesn’t trigger extra disk enter/output (I/O).
Determine 3: An summary of CryptoGuard’s operations
This functionality offers uneven safety, even in situations the place an unprotected distant machine on the community is attacking shared paperwork on a Sophos-protected file server, for instance. As famous above, most human-led ransomware assaults intention to additionally encrypt shared information on distant machines. In such instances, the ransomware itself is just not executed on the protected distant machine (both as a result of it wasn’t deployed there by the attacker or was blocked by endpoint safety). Because of this, the ransomware binary itself or the attacker-controlled course of (that performs the encryption) can’t be noticed from the machine that holds the focused information.
So, as a result of there isn’t a malicious code to be detected on the attacked machine, applied sciences like antivirus, machine studying, indicators of breach, and so forth.—all targeted on figuring out adversaries and their malicious code—are utterly sidelined and never in play (even when it’s a well-known years-old pattern chargeable for the encryption). Nonetheless, CryptoGuard can acknowledge when a distant machine replaces paperwork within the shared folder with encrypted variations, and mechanically takes motion by blocking the IP handle of the distant machine and reversing the adjustments it made. It creates non permanent backups of any modified information, in order that the adjustments might be rolled again if mass encryption is detected, and may also detect the deployment of ransom notes inside the folders the place the ransomware has encrypted information. Consequently, it generally identifies cases of information exfiltration, regardless that it was not explicitly designed for that objective.
Zero-trust
Adversaries will generally abuse an current course of, or bundle a usually benign course of that hundreds a malicious DLL (generally known as DLL side-loading), in an effort to carry out encryption. The encryption exercise is carried out underneath the identification of the benign course of, now operating attacker-code, and encrypting paperwork.
An actual-world instance of that is the Kaseya VSA incident, the place the REvil menace actor embedded a malicious DLL to be side-loaded in an outdated however weak Home windows Defender executable. The menace actor purposely selected Defender, as a result of protections usually belief code signed by Microsoft. Moreover, a DLL can’t be examined as completely as an executable in a sandbox atmosphere, which means it could be ‘accredited’ sooner.
On that event, Sophos detected each the REvil payload itself, in addition to an REvil-specific code certificates. And whereas Kayesa’s safety exclusions allowed the REvil dropper to be put in on machines, CryptoGuard detected the ransomware, as a result of it’s not constrained by such exclusions and blocks file encryption wherever on protected drives.
A walkthrough
Conclusion
There isn’t a panacea in terms of battling ransomware. An efficient defence ought to embrace a myriad of layers, from vulnerability remediation and configuration opinions to consumer schooling and safety options. However, no matter which layers organizations make use of, and what number of, an vital facet to think about is the robustness and effectiveness of the final layer, when all different measures have failed and menace actors are ready to execute their ransomware. At that time, the options we’ve coated right here come into their very own.
These options are various, masking quite a few totally different behavioral traits and exercise. Many range broadly by way of their scalability, versatility, and cost-benefit ratios, and have distinct strengths and weaknesses. A key commonality is that the majority options give attention to ‘detecting badness’ not directly – whether or not via API name evaluation, honeyfiles, or some type of fingerprinting. That’s not essentially a drawback, and a layered and various defence stack is a stable method. However, as we’ve proven, the CryptoGuard method inside Intercept X is barely totally different, and extra uneven: specializing in file contents quite than the behaviors of ransomware or its operators.
Ransomware continues to evolve, and increasingly options and strategies are prone to seem in response. As we’ve been doing for the final ten years, we’ll proceed to trace adjustments in each ransomware and the options designed to detect and stop it.
[ad_2]