
[ad_1]

Anybody who works in laptop safety is aware of that they need to have two-factor authentication (2FA) enabled on their accounts.
2FA gives a further layer of safety. A hacker may be capable of guess, steal, or brute pressure the password in your accounts – however they received’t be capable of achieve entry except in addition they have a time-based one-time password.
So, how come Mandiant didn’t have 2FA defending its Twitter account, which was hacked final week to advertise a cryptocurrency rip-off?
Mandiant promised within the wake of the hack that it will share particulars of what had occurred, and – true to its phrase – it’s accomplished simply that.
However Mandiant’s clarification of the way it was hacked raises some extra questions.
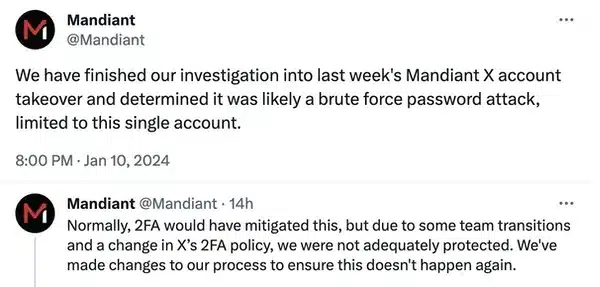
We’ve got completed our investigation into final week’s Mandiant X account
takeover and decided it was doubtless a brute pressure password assault,
restricted to this single account.
What they appear to be saying is that somebody tried over-and-over-and-over-and-over once more once more to interrupt into Mandiant’s Twitter account, or relatively used a pc to do it for them… and ultimately they acquired fortunate.
You must surprise simply how lengthy and sophisticated Mandiant’s Twitter password was if that actually was the case.
Presumably Mandiant has now modified the password, so why don’t they inform us what it was? Possibly we may all study one thing if we knew simply how a lot effort the hackers needed to go to to bruteforce Mandiant’s password, and the way lengthy it may need taken them.
PS. “doubtless”? Appears like Mandiant isn’t actually certain.
My guess had been that maybe Mandiant’s Twitter account was compromised in the same option to that of one other agency hacked across the similar time – CertiK.
In that case the hackers contacted CertiK posing as a Forbes journalist, and tricked an worker into clicking on a hyperlink that posed as a calendar scheduling hyperlink for an interview.
Anyway, lets look additional at what Mandiant has to say about its safety breach:
Usually, 2FA would have mitigated this, however attributable to some staff transitions and a change in X’s 2FA coverage, we weren’t adequately protected. We’ve made adjustments to our course of to make sure this doesn’t occur once more.
Properly, there’s a fastidiously worded sentence! Mandiant appears to be going out of its option to keep away from saying that it didn’t have 2FA enabled on its Twitter account, nevertheless it’s the one approach I can interpret it.
I suppose it’s fairly embarrassing for a cybersecurity firm to confess it doesn’t have 2FA enabled.
However then there’s the half about “a change in X’s 2FA coverage” (X is the daft identify we’re supposed to make use of for Twitter lately, however I’m not enjoying that recreation proper now…).
My guess is that Mandiant is referring to is the change Twitter introduced relating to 2FA final February. Twitter stated that it will be eradicating SMS-based 2FA for all however paid-up Twitter Blue subscribers in March 2023, and that anybody who didn’t wish to lose entry to Twitter must disable 2FA upfront.
On the time I criticised Twitter’s determination, believing that it will scale back safety for some customers.
SMS-based 2FA is likely one of the weakest methods to implement 2FA (due to SIM swap assaults), nevertheless it’s nonetheless higher than no 2FA in any respect.
It sounds to me like Mandiant eliminated SMS-based 2FA safety from its account (presumably out of concern that it will be locked out when Twitter made the characteristic premium-only), however by no means changed it with a stronger various, corresponding to a hardware-based safety key or app-based authenticator.
I do know that whenever you’re coping with accounts which are utilized by a staff of individuals relatively than a person that there may be further complexities in establishing multi-factor authentication, however there are methods round this. The reality is that there is no such thing as a affordable excuse for any firm (particularly a safety agency) to don’t have any 2FA in any respect defending its accounts.
Mandiant has revealed a weblog put up concerning the hackers and CLINKSLINK wallet-draining malware that it was linked to the assault.
[ad_2]