
[ad_1]
Report-Breaking Safety Vulnerabilities in 2023
In keeping with information from Statista, the quantity of vulnerabilities recorded in 2023 hit a file quantity with 29,000 new vulnerabilities reported. It is a 16% enhance since 2022 and a doubling since 2017. Within the first week of 2024 there have been 612 vulnerabilities reported.
This sheer quantity of vulnerabilities being launched, coupled with the rising prices of cybercrime, is stressing present operations groups in maintaining with the quantity. Doing all the pieces was by no means doable, and now it’s not even aspirational. Prioritizing time to make the best impression is vital in sustaining a powerful safety posture.
The Problem of Vulnerability Remediation
Telling groups to remediate vulnerabilities is like telling firefighters to place out forest fires within the southwest throughout summer time. There are at all times fires; you’ll by no means get all of them put out. Given budgetary and real-world useful resource constraints, what’s the stack ranked significance of various priorities during which to speculate assets for the utmost impression? That is vital as maintaining with this has develop into a full-time job as monetary companies search to stay compliant and safe. It’s not sensible or doable to right away tackle all vulnerabilities in a monetary companies firm’s giant heterogeneous IT environments. Prioritization of risk-based vulnerabilities is vital to make sure organizations can handle safety danger whereas managing operational availability.
Cisco’s Impression on Vulnerability Administration
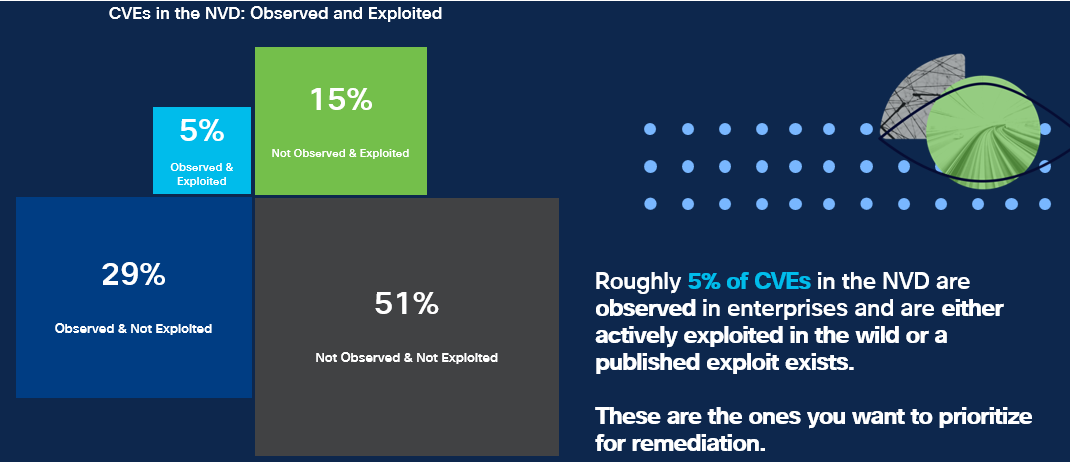
Particularly, Fortune 500 monetary companies corporations who use Cisco Vulnerability Administration report an 82% discount in high-risk vulnerabilities after Cisco Vulnerability Administration offered a complete view into the context of the vulnerabilities. That is carried out by monitoring Frequent Vulnerabilities and Exposures (CVE) throughout the lifecycle, from preliminary creation to real-world exploitation. This evaluation consists of the next information sources:
- Open-source databases similar to MITRE and the NVD (Nationwide Vulnerability Database)
- Different vulnerability scoring sources like IBM X-Pressure, Silobreaker, and distinctive analysis from famend analysis groups
- Early warning indicators derived from darkish net sources, blogs, social media, and extra
- Exploit databases like Exploit DB, Metasploit, GitHub, and others
- Malware evaluation, using information from ReversingLabs to find out if a selected CVE is incessantly utilized by malware
- Info on malware households and menace actors
- Information on the quantity and velocity of profitable exploits noticed within the wild
Important Reductions in Remediation Efforts
By utilizing the Cisco Vulnerability Administration strategy, Mattel reported a 50% discount in time spent on remediation. A worldwide 500 hospitality firm reported a 75% discount in time spent on vulnerability investigation. And Constitution reported a 75% discount in time spent on reporting. Scaling the safety groups to prioritized response maximizes the concentrate on the very best threats, and is the aim of Cisco Vulnerability administration.
Prioritizing with Quantity and Velocity Information
The gathering of quantity and velocity information is especially essential for safety groups in search of to prioritize vulnerabilities. Whereas most vulnerability administration distributors monitor binary sure/no indicators of exploitation, Cisco goes past that. Our information offers insights into the variety of machines exploited by a selected CVE throughout the previous 24 hours, permitting us to evaluate if a vulnerability is presently extra dangerous in comparison with earlier days.
All of this information is fed into Cisco Vulnerability Administration’s machine studying model-based danger scoring, which includes our patented exploit prediction capabilities. The result’s the Cisco Safety Threat Rating (previously the Kenna Threat Rating), which informs our clients in regards to the stage of danger related to a vulnerability primarily based on real-world attacker exercise.
Integration with Current Monetary Providers Instruments
One other key worth of Cisco’s Vulnerability administration strategy is the combination with present device units that Monetary Providers use. By increasing the capabilities of present belongings already in use, we create additive worth to safety groups in making a complimentary answer that gives enumeration of dangers from these different instruments.

Key Options of Cisco VM particular to regulated financials
Cisco Vulnerability administration helps financials focus their danger priorities to make the most important impression. It additionally helps financials in assembly regulatory necessities, similar to these current within the PCI steerage and FFIEC regulatory necessities. Among the areas Cisco VM can assist financials meet regulatory necessities embrace:
- Threat-based Vulnerability Administration: Monetary establishments are required to handle and mitigate cybersecurity dangers. Cisco’s platform makes use of superior algorithms to research vulnerabilities primarily based on the danger they pose, enabling monetary establishments to prioritize and tackle probably the most vital threats first, which is usually a requirement in monetary laws.
- Compliance Reporting: Regulatory our bodies usually require detailed studies on the safety posture of economic establishments. Cisco’s platform can generate studies that exhibit compliance with numerous regulatory requirements, such because the Cost Card Business Information Safety Commonplace (PCI DSS) and others.
- Risk Intelligence: Cisco’s platform offers menace intelligence that may assist monetary establishments keep conscious of the most recent cybersecurity threats. This intelligence can be utilized to proactively put together in opposition to in opposition to potential assaults, which is consistent with the proactive stance anticipated by many monetary regulators.
- Automated Asset Discovery: Monitoring all belongings inside a monetary establishment is vital for compliance. Cisco’s options can routinely uncover and stock digital belongings, making certain nothing is missed within the vulnerability administration course of.
- Patch Effectiveness: Cisco’s platform not solely helps prioritize which vulnerabilities to patch but in addition offers insights into the effectiveness of patches which have been utilized. This helps be sure that remediation efforts are profitable, important for sustaining a powerful safety posture and compliance.
- Integrations with Different Safety Instruments: The integrations listed above will not be solely vital to addressing safety however vital for assembly reporting on, monitoring, and assembly regulatory necessities. There isn’t one device that by itself can resolve for this, and the combination helps instruments centered on audit perceive the state of the vulnerability panorama.
- Steady Monitoring: Regulatory necessities usually mandate steady monitoring for vulnerabilities and incidents. Cisco’s platform can constantly scan and monitor the surroundings, offering up-to-date details about the establishment’s safety state. By partnerships, the continual monitoring element may be even stronger and match right into a monetary methodology.
Cisco Vulnerability Administration is vital to serving to financials guarantee they’re getting the best impression out of their safety actions via addressing prioritized threats, and making certain compliance to regulatory necessities.
For extra info on how Cisco can assist your monetary companies wants,
discover all of our options at Cisco for Monetary Providers
Share:
[ad_2]