
[ad_1]
Authored by Yukihiro Okutomi
McAfee’s Cellular crew noticed a smishing marketing campaign in opposition to Japanese Android customers posing as an influence and water infrastructure firm in early June 2023. This marketing campaign ran for a brief time from June 7. The SMS message alerts about cost issues to lure victims to a phishing web site to contaminate the goal units with a remote-controlled SpyNote malware. Prior to now, cybercriminals have typically focused monetary establishments. Nevertheless, on this event, public utilities have been the goal to generate a way of urgency and push victims to behave instantly. Defend your Android and iOS cell units with McAfee Cellular Safety.
Smishing Assault Marketing campaign
A phishing SMS message impersonating a energy or water provider claims a cost drawback, as proven within the screenshot under. The URL within the message directs the sufferer to a phishing web site to obtain cell malware.
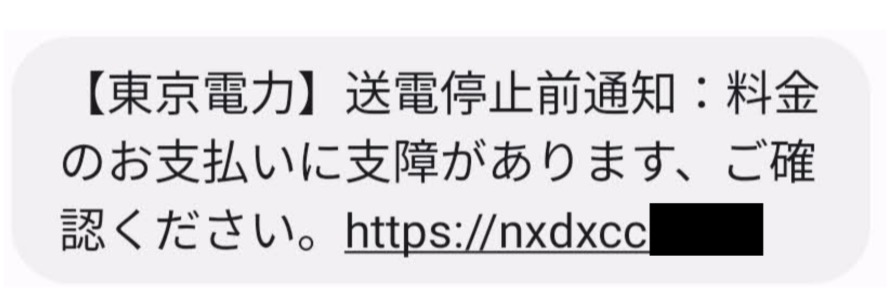
Discover of suspension of energy transmission due to non-payment of expenses from an influence firm in Tokyo (Supply: Twitter)
Discover of suspension of water provide due to non-payment of expenses from a water firm in Tokyo (Supply: Twitter)
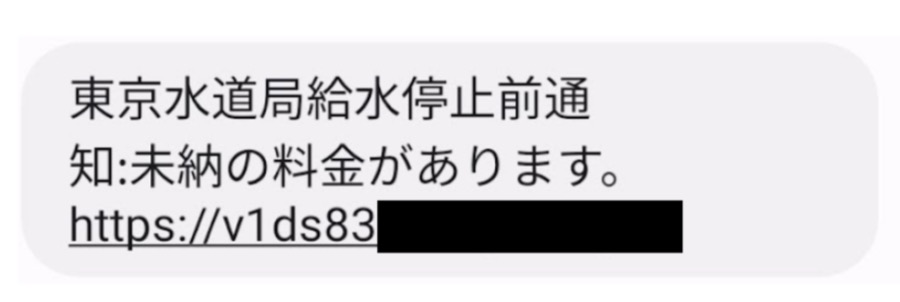
When accessed with a cell browser, it can begin downloading malware and show a malware set up affirmation dialog.
The affirmation dialog of Adware set up through browser (Supply: Twitter)
SpyNote malware
SpyNote is a identified household of malware that proliferated after its supply code was leaked in October 2022. Not too long ago, the malware was utilized in a marketing campaign focusing on monetary establishments in January and focusing on Financial institution of Japan in April 2023.
The SpyNote malware is remotely managed spyware and adware that exploits accessibility companies and gadget administrator privileges. It steals gadget info and delicate person info akin to gadget location, contacts, incoming and outgoing SMS messages, and telephone calls. The malware deceives customers through the use of reputable app icons to look actual.

Software Icons disguised by malware.
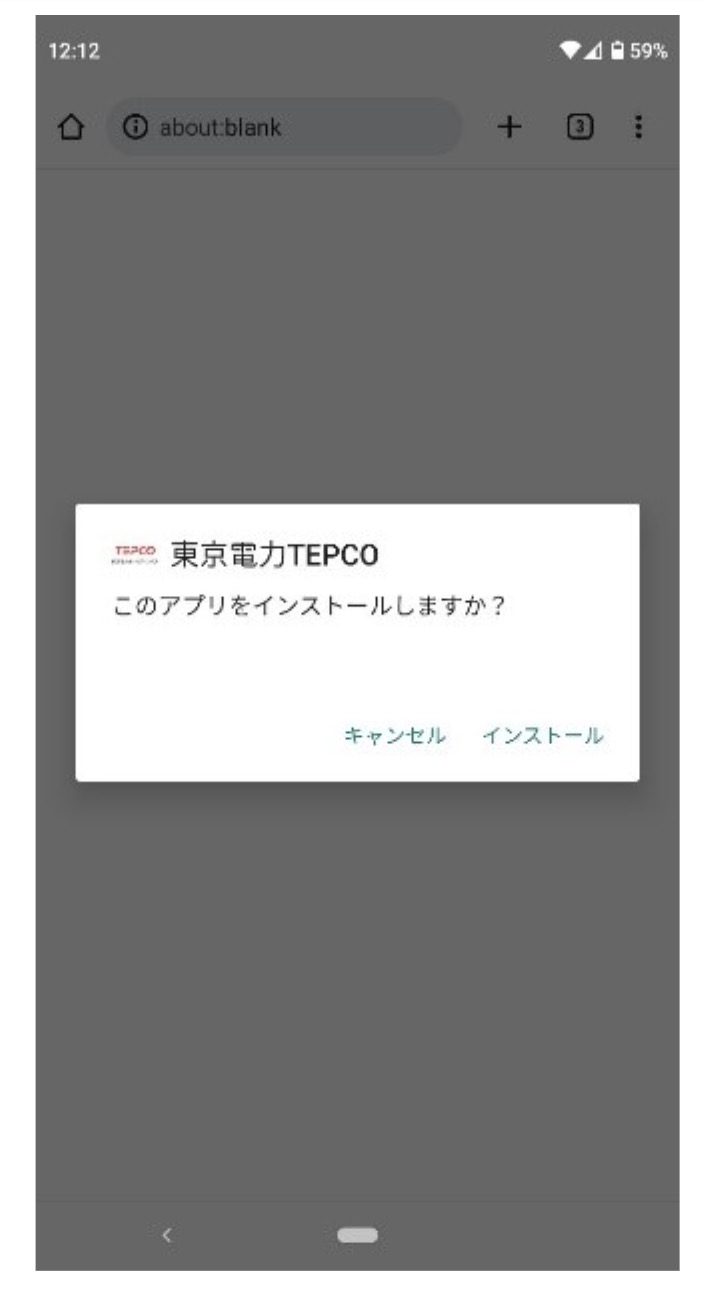
After launching the malware, the app opens a faux settings display screen and prompts the person to allow the Accessibility function. When the person clicks the arrow on the backside of the display screen, the system Accessibility service settings display screen is displayed.
A faux setting display screen (left), system setting display screen (heart and proper)
By permitting the Accessibility service, the malware disables battery optimization in order that it might probably run within the background and mechanically grants unknown supply set up permission to put in one other malware with out the person’s information. Along with spying on the sufferer’s gadget, it additionally steals two-factor authentication on Google Authenticator and Gmail and Fb info from the contaminated gadget.
Though the distribution methodology is completely different, the step of requesting Accessibility service after launching the app is much like the case of the Financial institution of Japan that occurred in April.
Scammers sustain with present occasions and try and impersonate well-known firms which have a cause to succeed in out to their prospects. The cell malware assault utilizing SpyNote found this time targets cell apps for all times infrastructure akin to electrical energy and water. One of many causes for that is that electrical payments and water payments, which was once issued on paper, at the moment are managed on the internet and cell app. If you wish to study smishing, seek the advice of this text “What Is Smishing? Right here’s The right way to Spot Pretend Texts and Maintain Your Information Secure”. McAfee Cellular Safety detects this risk as Android/SpyNote and alerts cell customers whether it is current and additional protects them from any information loss. For extra info, go to McAfee Cellular Safety.
Indicators of compromise (IoC)
C2 Server:
Malware Samples:
| SHA256 Hash | Bundle title | Software title |
| 075909870a3d16a194e084fbe7a98d2da07c8317fcbfe1f25e5478e585be1954 | com.faceai.boot | キャリア安全設定 |
| e2c7d2acb56be38c19980e6e2c91b00a958c93adb37cb19d65400d9912e6333f | com.faceai.boot | 東京電力 |
| a532c43202c98f6b37489fb019ebe166ad5f32de5e9b395b3fc41404bf60d734 | com.faceai.boot | 東京電力TEPCO |
| cb9e6522755fbf618c57ebb11d88160fb5aeb9ae96c846ed10d6213cdd8a4f5d | com.faceai.boot | 東京電力TEPCO |
| 59cdbe8e4d265d7e3f4deec3cf69039143b27c1b594dbe3f0473a1b7f7ade9a6 | com.faceai.boot | 東京電力TEPCO |
| 8d6e1f448ae3e00c06983471ee26e16f6ab357ee6467b7dce2454fb0814a34d2 | com.faceai.boot | 東京電力TEPCO |
| 5bdbd8895b9adf39aa8bead0e3587cc786e375ecd2e1519ad5291147a8ca00b6 | com.faceai.boot | 東京電力TEPCO |
| a6f9fa36701be31597ad10e1cec51ebf855644b090ed42ed57316c2f0b57ea3c | com.faceai.boot | 東京電力TEPCO |
| f6e2addd189bb534863afeb0d06bcda01d0174f5eac6ee4deeb3d85f35449422 | com.faceai.boot | 東京電力TEPCO |
| 755585571f47cd71df72af0fad880db5a4d443dacd5ace9cc6ed7a931cb9c21d | com.faceai.boot | 東京電力TEPCO |
| 2352887e3fc1e9070850115243fad85c6f1b367d9e645ad8fc7ba28192d6fb85 | com.faceai.boot | 東京電力TEPCO |
| 90edb28b349db35d32c0190433d3b82949b45e0b1d7f7288c08e56ede81615ba | com.faceai.boot | 東京電力TEPCO |
| 513dbe3ff2b4e8caf3a8040f3412620a3627c74a7a79cce7d9fab5e3d08b447b | com.faceai.boot | 東京電力TEPCO |
| f6e2addd189bb534863afeb0d06bcda01d0174f5eac6ee4deeb3d85f35449422 | com.faceai.boot | 東京電力TEPCO |
| 0fd87da37712e31d39781456c9c1fef48566eee3f616fbcb57a81deb5c66cbc1 | com.faceai.increase | 東京水道局アプリ |
| acd36f7e896e3e3806114d397240bd7431fcef9d7f0b268a4e889161e51d802b | com.faceai.increase | 東京水道局アプリ |
| 91e2f316871704ad7ef1ec74c84e3e4e41f557269453351771223496d5de594e | com.faceai.increase | 東京水道局アプリ |
[ad_2]
