
[ad_1]
Authored by Dexter Shin
McAfee Cellular Analysis Staff discovered an Android banking trojan signed with a key utilized by reputable apps in South Korea final 12 months. By design, Android requires that each one functions should be signed with a key, in different phrases a keystore, to allow them to be put in or replaced. As a result of this key can solely be utilized by the developer who created it, an software signed with the identical key is assumed to belong to the identical developer. That’s the case of this Android banking trojan that makes use of this reputable signing key to bypass signature-based detection strategies. And these banking trojans weren’t distributed on Google Play or official app shops till now. This menace had been disclosed to the firm that owns the reputable key final 12 months and the firm has taken precautions. The firm has confirmed that they’ve changed the signing key and at the moment, all of their reputable apps are signed with a brand new signing key.
Android malware utilizing a reputable signing key
Whereas monitoring the Android banking trojan Fakecalls we discovered a pattern utilizing the identical signing key as a properly–identified app in Korea. This app is developed by a respected IT companies firm with in depth enterprisees throughout varied sectors, together with however not restricted to IT, gaming, cost, and advertising. We confirmed that a lot of the malicious samples utilizing this key fake to be a financial institutioning app as they use the similar icon as the actual banking apps.
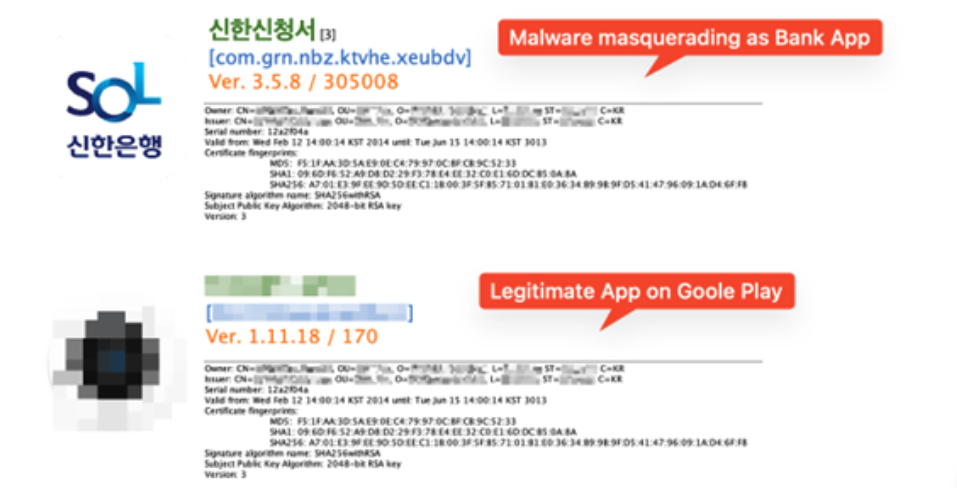
Determine 1. Malware and reputable app on Google Play
Distribution methodology and newest status
Domains verified final August once we first found the samples at the moment are down. Nevertheless, we investigated URLs associated to this malware and we discovered comparable ones associated to this menace. Amongst them, we recognized a phishing web site that is nonetheless alive throughout our analysis. The positioning can also be disguised as a banking web site.

Determine 2. A phishing web page disguised as a Korean banking web site
We additionally discovered that they up to date the area info of this internet web page a couple of days earlier than our investigation.
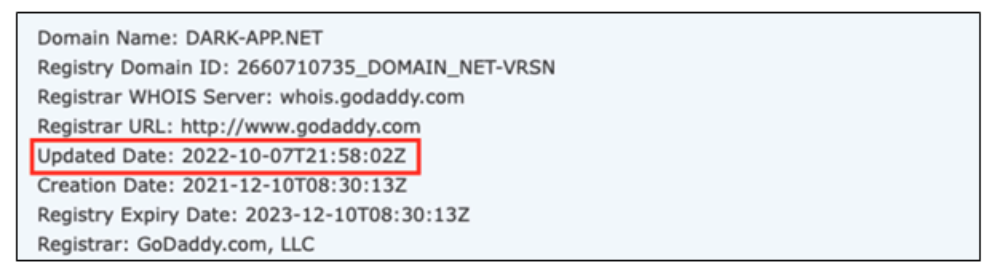
So we took a deeper look into this area and we discovered extra uncommon IP addresses that led us to the Command and control(C2) server admin pages utilized by the cybercriminals to regulate the contaminated units.
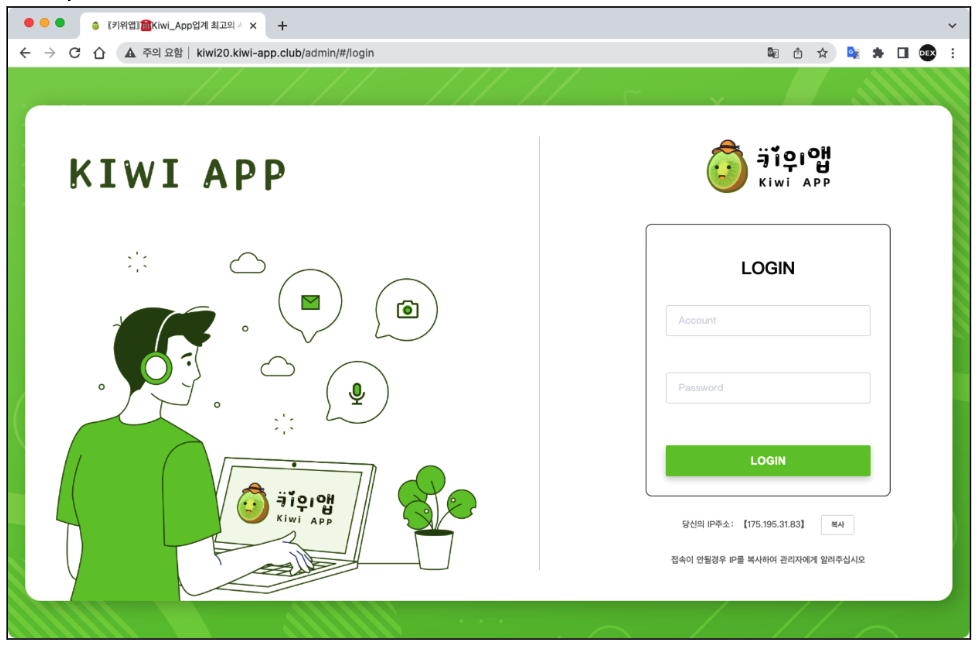
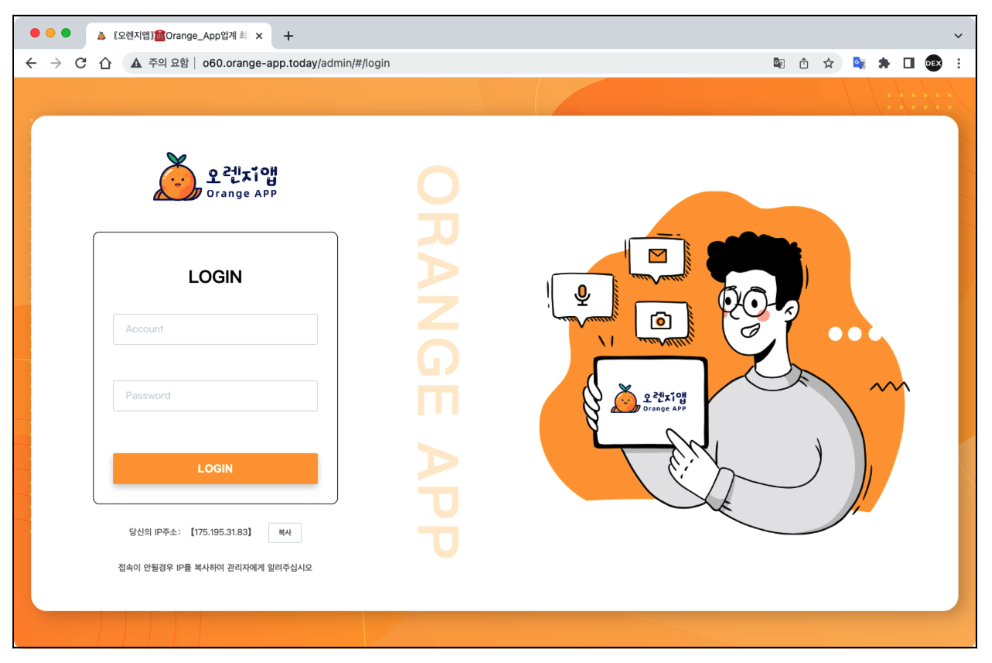
Determine 3. Fakecalls Command and management(C2) admin web pages
How does it work
When we examine the APK file construction, we are able to see that this malware makes use of a packer to keep away from evaluation and detection. The malicious code is encrypted in one of many recordsdata beneath.
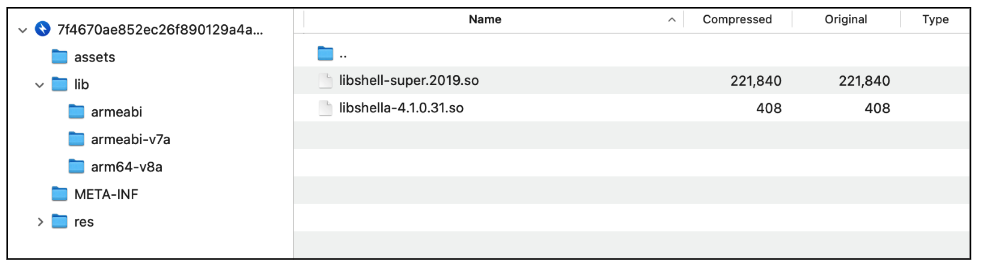
Determine 4. Tencent’s Legu Packer libraries
After decrypting the DEX file, we discovered some uncommon performance. The code beneath will get the Android package deal info from a file with a HTML extension.
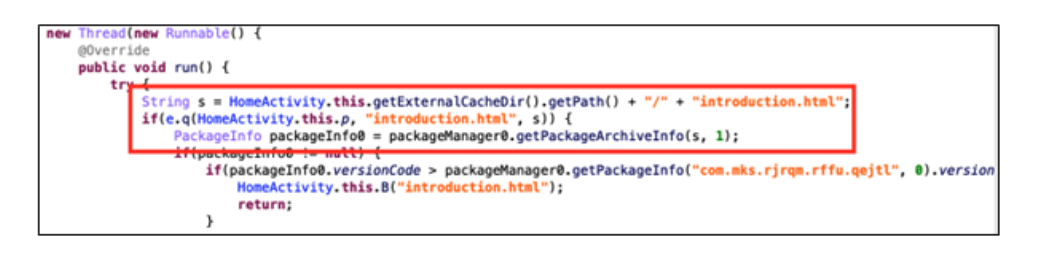 Determine 5. Questionable code within the decrypted DEX file
Determine 5. Questionable code within the decrypted DEX file
This file is in truth one other APK (Android Software) quite than a conventional HTML file designed to be displayed in an online browser.
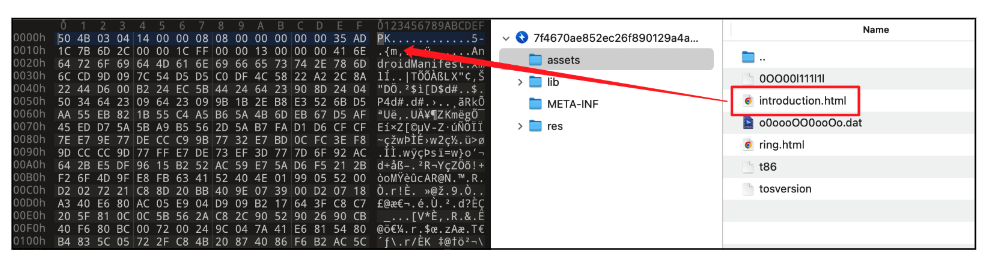 Determine 6. APK file disguised as an HTML file
Determine 6. APK file disguised as an HTML file
When the consumer launches the malware, it instantly asks for permission to put in one other app. Then it tries to put in an software saved in the “property” listing as “introduction.html”. The “introduction.html” is an APK file and actual malicious habits occurs right here.
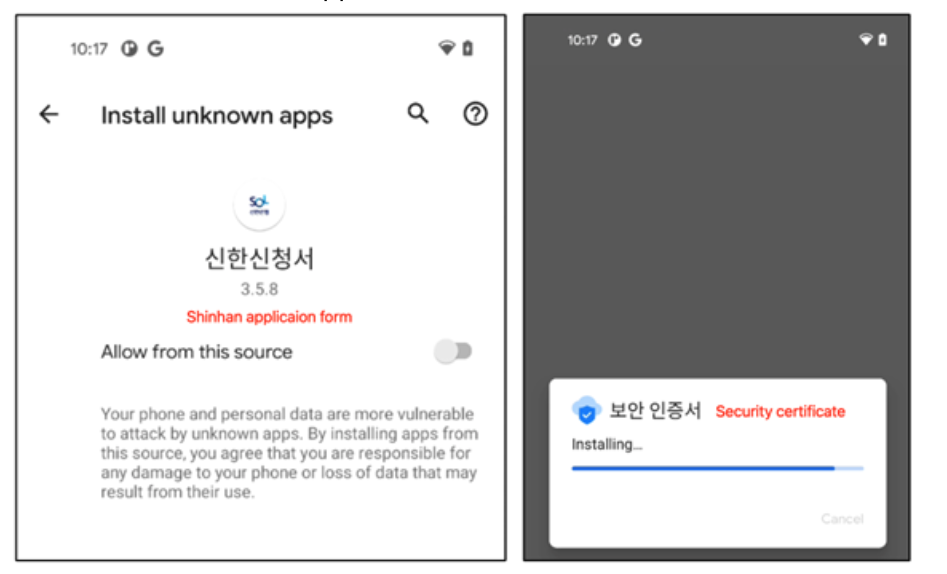
Determine 7. Dropper asks you to put in the primary payload
When the dropped payload is about to be put in, it asks for a number of permissions to entry delicate private info.
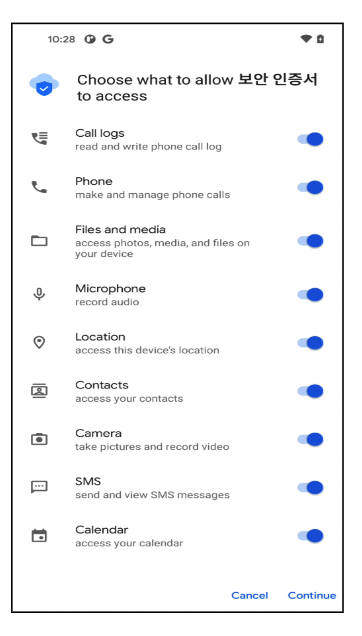
Determine 8. Permissions required by the primary malicious software
It additionally registers a number of companies and receivers to regulate notifications from the machine and to obtain instructions from a distant Command and Management server.
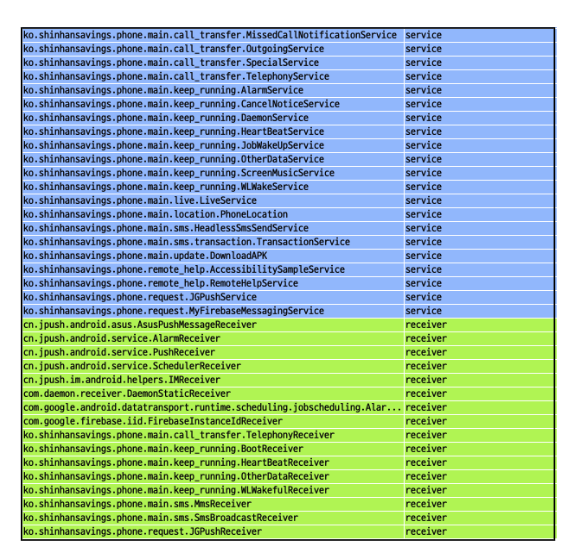
Determine 9. Providers and receivers registered by the primary payload
In contrast, the malware makes use of a reputable push SDK to obtain commands from a distant server. Listed here are the full record of instructions and their function.
| Command title | Objective |
| notice | sms message add |
| incoming_transfer | caller quantity add |
| del_phone_record | delete name log |
| zhuanyi | set name forwarding with parameter |
| clear_note | delete sms message |
| assign_zhuanyi | set name forwarding |
| file | file add |
| lanjie | block sms message from specified numbers |
| allfiles | discover all attainable recordsdata and add them |
| email_send | ship electronic mail |
| record_telephone | name recording on |
| inout | re-mapping on C2 server |
| blacklist | register as blacklist |
| listener_num | no operate |
| no_listener_num | disable monitoring a selected quantity |
| rebuild | reset and reconnect with C2 |
| deleteFile | delete file |
| num_address_list | contacts add |
| addContact | add contacts |
| all_address_list | name file add |
| deleteContact | delete contacts |
| note_intercept | intercept sms message from specified numbers |
| intercept_all_phone | intercept sms message from all |
| clear_date | delete all file |
| clear_phone_contact | delete all contacts |
| clear_phone_record | delete all name log |
| per_note | fast sms message add |
| soft_name | app title add |
Cybercriminals are continuously evolving and utilizing new methods to bypass safety checks, akin to abusing reputable signing keys. Happily, there was no injury to customers because of this signing key leak. Nevertheless, we suggest that customers set up safety software program on their units to answer these threats. Additionally, customers are advisable to obtain and use apps from the official app shops.
McAfee Cellular Safety detects this menace as Android/Banker whatever the software, is signed with the beforehand reputable signing key.
Indicators of Compromise
| SHA256 | Identify | Sort |
| 7f4670ae852ec26f890129a4a3d3e95c079f2f289e16f1aa089c86ea7077b3d8 | 신한신청서 | Dropper |
| 9e7c9b04afe839d1b7d7959ad0092524fd4c6b67d1b6e5c2cb07bb67b8465eda | 신한신청서 | Dropper |
| 21ec124012faad074ee1881236c6cde7691e3932276af9d59259df707c68f9dc | 신한신청서 | Dropper |
| 9621d951c8115e1cc4cf7bd1838b8e659c7dea5d338a80e29ca52a8a58812579 | 신한신청서 | Dropper |
| 60f5deb79791d2e8c2799e9af52adca5df66d1304310d1f185cec9163deb37a2 | 보안인증서 | Banker |
| 756cffef2dc660a241ed0f52c07134b7ea7419402a89d700dffee4cc6e9d5bb6 | 보안인증서 | Banker |
| 6634fdaa22db46a6f231c827106485b8572d066498fc0c39bf8e9beb22c028f6 | 보안인증서 | Banker |
| 52021a13e2cd7bead4f338c8342cc933010478a18dfa4275bf999d2bc777dc6b | 보안인증서 | Banker |
| 125772aac026d7783b50a2a7e17e65b9256db5c8585324d34b2e066b13fc9e12 | 보안인증서 | Banker |
| a320c0815e09138541e9a03c030f30214c4ebaa9106b25d3a20177b5c0ef38b3 | 보안인증서 | Banker |
| c7f32890d6d8c3402601743655f4ac2f7390351046f6d454387c874f5c6fe31f | 보안인증서 | Banker |
| dbc7a29f6e1e91780916be66c5bdaa609371b026d2a8f9a640563b4a47ceaf92 | 보안인증서 | Banker |
| e6c74ef62c0e267d1990d8b4d0a620a7d090bfb38545cc966b5ef5fc8731bc24 | 보안인증서 | Banker |
Domains:
- http[://]o20-app.dark-app.web
- http[://]o20.orange-app.in the present day
- http[://]orange20.orange-app.in the present day
[ad_2]