
[ad_1]

Hackers are more and more abusing the authentic Cloudflare Tunnels function to create stealthy HTTPS connections from compromised gadgets, bypass firewalls, and keep long-term persistence.
The approach is not solely new, as Phylum reported in January 2023 that risk actors created malicious PyPI packages that used Cloudflare Tunnels to stealthy steal knowledge or remotely entry gadgets.
Nonetheless, it seems that extra risk actors have began to make use of this tactic, as GuidePoint’s DFIR and GRIT groups reported final week, seeing an uptick in exercise.
Abusing Cloudflare Tunnels
CloudFlare Tunnels is a well-liked function supplied by Cloudflare, permitting customers to create safe, outbound-only connections to the Cloudflare community for net servers or purposes.
Customers can deploy a tunnel just by putting in one of many accessible cloudflared purchasers for Linux, Home windows, macOS, and Docker.
From there, the service is uncovered to the web on a user-specified hostname to accommodate authentic use-case eventualities equivalent to useful resource sharing, testing, and many others.
Cloudflare Tunnels present a variety of entry controls, gateway configurations, workforce administration, and consumer analytics, giving customers a excessive diploma of management over the tunnel and the uncovered compromised providers.
In GuidePoint’s report, the researchers say that extra risk actors abuse Cloudflare Tunnels for nefarious functions, equivalent to gaining stealthy persistent entry to the sufferer’s community, evading detection, and exfiltrating compromised gadgets’ knowledge.
A single command from the sufferer’s system, which does not expose something apart from the attacker’s distinctive tunnel token, is sufficient to arrange the discreet communication channel. On the identical time, the risk actor can modify a tunnel’s configuration, disable, and allow it as wanted in real-time.
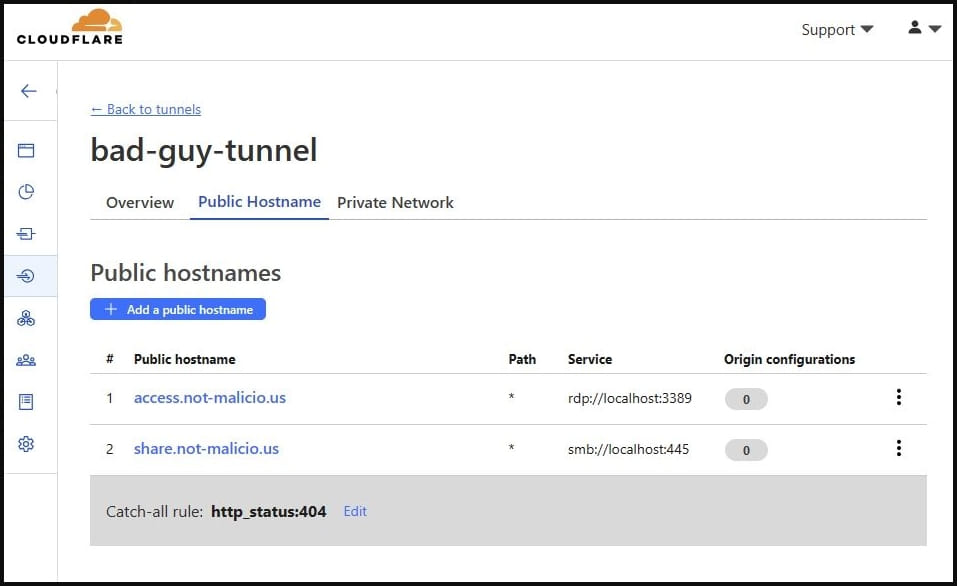
Supply: GuidePoint
“The tunnel updates as quickly because the configuration change is made within the Cloudflare Dashboard, permitting TAs to allow performance solely once they need to conduct actions on the sufferer machine, then disable performance to forestall publicity of their infrastructure,” explains GuidePoint.
“For instance, the TA may allow RDP connectivity, acquire info from the sufferer machine, then disable RDP till the next day, thus decreasing the prospect of detection or the flexibility to watch the area utilized to determine the connection.”
As a result of the HTTPS connection and knowledge trade happens over QUIC on port 7844, it’s unlikely that firewalls or different community safety options will flag this course of until they’re particularly configured to take action.
Supply: GuidePoint
Additionally, if the attacker needs to be much more stealthy, they’ll abuse Cloudflare’s ‘TryCloudflare‘ function that lets customers create one-time tunnels with out creating an account.
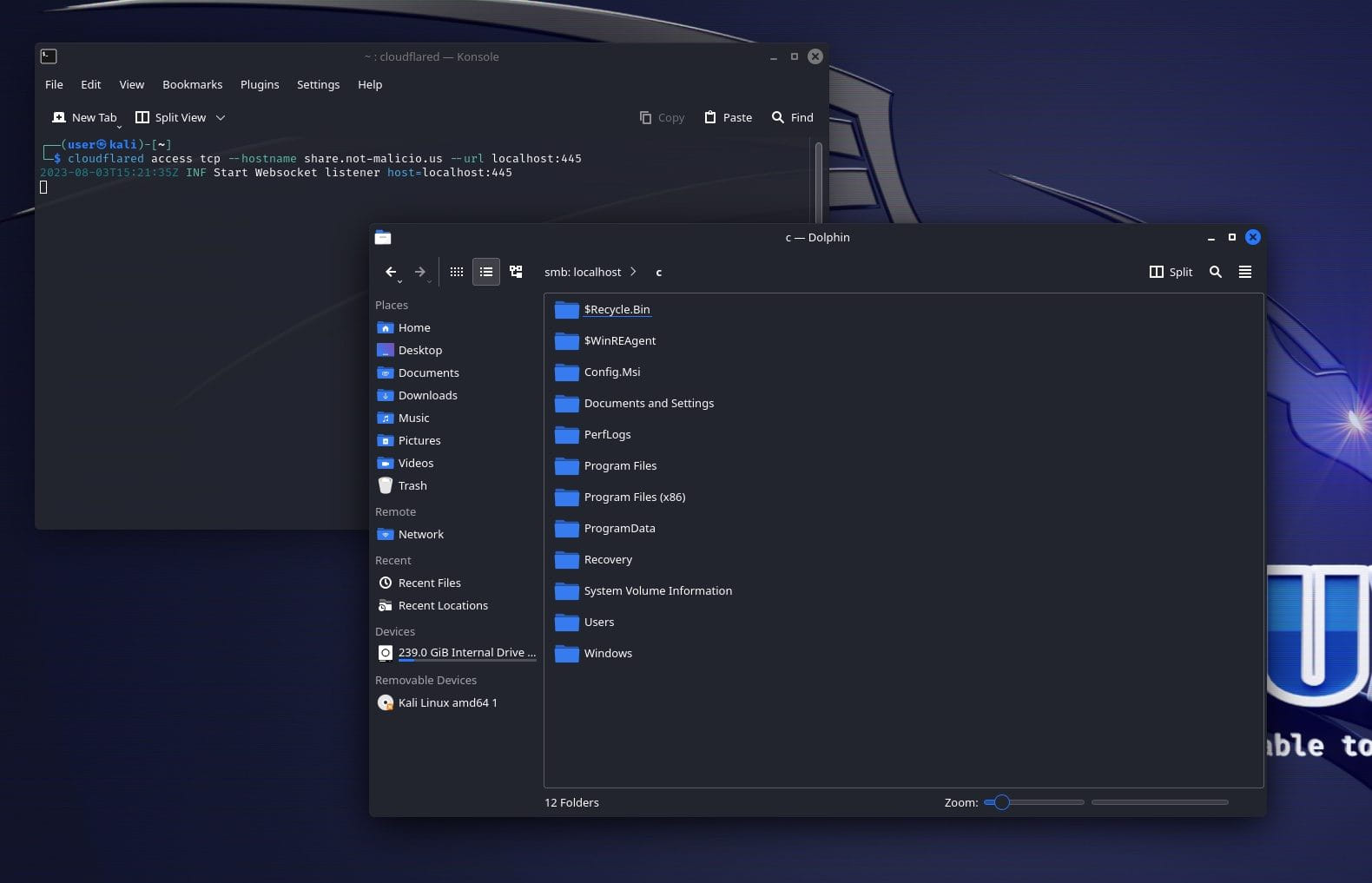
To make issues worse, GuidePoint says it is also doable to abuse Cloudflare’s ‘Personal Networks’ function to permit an attacker who has established a tunnel to a single shopper (sufferer) system to entry a complete vary of inside IP addresses remotely.
“Now that the personal community is configured, I can pivot to gadgets on the native community, accessing providers which might be restricted to native community customers,” warned GuidePoint researcher Nic Finn.
To detect unauthorized use of Cloudflare Tunnels, GuidePoint recommends that organizations monitor for particular DNS queries (shared within the report) and use non-standard ports like 7844.
Moreover, as Cloudflare Tunnel requires the set up of the ‘cloudflared‘ shopper, defenders can detect its use by monitoring file hashes related to shopper releases.
[ad_2]