
[ad_1]
The password supervisor service LastPass is now forcing a few of its customers to select longer grasp passwords. LastPass says the modifications are wanted to make sure all prospects are protected by their newest safety enhancements. However critics say the transfer is little greater than a public relations stunt that can do nothing to assist numerous early adopters whose password vaults had been uncovered in a 2022 breach at LastPass.
LastPass despatched this notification to customers earlier this week.
LastPass instructed prospects this week they might be pressured to replace their grasp password if it was lower than 12 characters. LastPass formally instituted this variation again in 2018, however some undisclosed variety of the corporate’s earlier prospects had been by no means required to extend the size of their grasp passwords.
That is vital as a result of in November 2022, LastPass disclosed a breach during which hackers stole password vaults containing each encrypted and plaintext knowledge for greater than 25 million customers.
Since then, a gradual trickle of six-figure cryptocurrency heists focusing on security-conscious folks all through the tech business has led some safety consultants to conclude that crooks possible have succeeded at cracking open a number of the stolen LastPass vaults.
KrebsOnSecurity final month interviewed a sufferer who lately noticed greater than three million {dollars} price of cryptocurrency siphoned from his account. That person signed up with LastPass almost a decade in the past, saved their cryptocurrency seed phrase there, and but by no means modified his grasp password — which was simply eight characters. Nor was he ever pressured to enhance his grasp password.
That story cited analysis from Adblock Plus creator Wladimir Palant, who mentioned LastPass didn’t improve many older, authentic prospects to safer encryption protections that had been provided to newer prospects over time.
For instance, one other necessary default setting in LastPass is the variety of “iterations,” or what number of occasions your grasp password is run by way of the corporate’s encryption routines. The extra iterations, the longer it takes an offline attacker to crack your grasp password.
Palant mentioned that for a lot of older LastPass customers, the preliminary default setting for iterations was wherever from “1” to “500.” By 2013, new LastPass prospects got 5,000 iterations by default. In February 2018, LastPass modified the default to 100,100 iterations. And really lately, it upped that once more to 600,000. Nonetheless, Palant and others impacted by the 2022 breach at LastPass say their account safety settings had been by no means forcibly upgraded.
Palant known as this newest motion by LastPass a PR stunt.
“They despatched this message to everybody, whether or not they have a weak grasp password or not – this fashion they will once more blame the customers for not respecting their insurance policies,” Palant mentioned. “However I simply logged in with my weak password, and I’m not pressured to vary it. Sending emails is reasonable, however they as soon as once more didn’t implement any technical measures to implement this coverage change.”
Both means, Palant mentioned, the modifications gained’t assist folks affected by the 2022 breach.
“These folks want to vary all their passwords, one thing that LastPass nonetheless gained’t suggest,” Palant mentioned. “However it should considerably assist with the breaches to come back.”
LastPass CEO Karim Toubba mentioned altering grasp password size (and even the grasp password itself) will not be designed to deal with already stolen vaults which are offline.
“That is meant to higher defend prospects’ on-line vaults and encourage them to convey their accounts as much as the 2018 LastPass commonplace default setting of a 12-character minimal (however might choose out from),” Toubba mentioned in an emailed assertion. “We all know that some prospects might have chosen comfort over safety and utilized much less complicated grasp passwords regardless of encouragement to make use of our (or others) password generator to do in any other case.”
A primary performance of LastPass is that it’ll choose and bear in mind prolonged, complicated passwords for every of your web sites or on-line companies. To routinely populate the suitable credentials at any web site going ahead, you merely authenticate to LastPass utilizing your grasp password.
LastPass has at all times emphasised that in the event you lose this grasp password, that’s too unhealthy as a result of they don’t retailer it and their encryption is so robust that even they will’t assist you to recuperate it.
However consultants say all bets are off when cybercrooks can get their fingers on the encrypted vault knowledge itself — versus having to work together with LastPass through its web site. These so-called “offline” assaults permit the unhealthy guys to conduct limitless and unfettered “brute power” password cracking makes an attempt in opposition to the encrypted knowledge utilizing highly effective computer systems that may every strive hundreds of thousands of password guesses per second.
A chart on Palant’s weblog put up presents an concept of how growing password iterations dramatically will increase the prices and time wanted by the attackers to crack somebody’s grasp password. Palant mentioned it might take a single high-powered graphics card a couple of 12 months to crack a password of common complexity with 500 iterations, and about 10 years to crack the identical password run by way of 5,000 iterations.
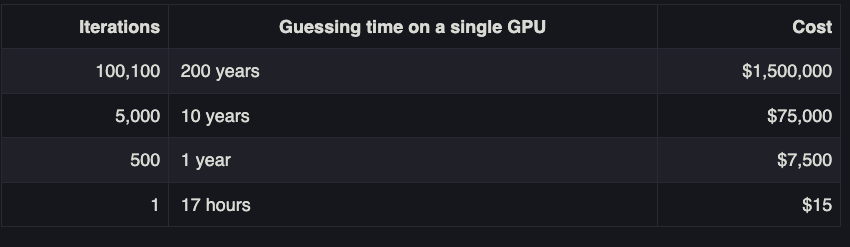
Picture: palant.data
Nevertheless, these numbers radically come down when a decided adversary additionally has different large-scale computational belongings at their disposal, comparable to a bitcoin mining operation that may coordinate the password-cracking exercise throughout a number of highly effective programs concurrently.
That means, LastPass customers whose vaults had been by no means upgraded to larger iterations and whose grasp passwords had been weak (lower than 12 characters) possible have been a major goal of distributed password-cracking assaults ever because the LastPass person vaults had been stolen late final 12 months.
Requested why some LastPass customers had been left behind on older safety minimums, Toubba mentioned a “small share” of shoppers had corrupted objects of their password vaults that prevented these accounts from correctly upgrading to the brand new necessities and settings.
“We’ve got been capable of decide {that a} small share of shoppers have objects of their vaults which are corrupt and after we beforehand utilized automated scripts designed to re-encrypt vaults when the grasp password or iteration depend is modified, they didn’t full,” Toubba mentioned. “These errors weren’t initially obvious as a part of these efforts and, as we have now found them, we have now been working to have the ability to treatment this and end the re-encryption.”
Nicholas Weaver, a researcher at College of California, Berkeley’s Worldwide Pc Science Institute (ICSI) and lecturer at UC Davis, mentioned LastPass made an enormous mistake years in the past by not force-upgrading the iteration depend for present customers.
“And now that is blaming the customers — ‘it is best to have used an extended passphrase’ — not them for having weak defaults that had been by no means upgraded for present customers,” Weaver mentioned. “LastPass in my e book is one step above snake-oil. I was, ‘Decide whichever password supervisor you need,’ however now I’m very a lot, ‘Decide any password supervisor however LastPass.’”
Requested why LastPass isn’t recommending that customers change all the passwords secured by the encrypted grasp password that was stolen when the corporate acquired hacked final 12 months, Toubba mentioned it’s as a result of “the information demonstrates that almost all of our prospects comply with our suggestions (or better), and the likelihood of efficiently brute forcing vault encryption is enormously decreased accordingly.”
“We’ve been telling prospects since December of 2022 that they need to be following really useful tips,” Toubba continued. “And in the event that they haven’t adopted the rules we really useful that they modify their downstream passwords.”
[ad_2]