[ad_1]
Quantum computer systems are altering the cryptography guidelines
Beneath Knowledge Encryption, the CISA Zero Belief Maturity Mannequin v2.0 cites the criticality of “cryptographic agility” on the third (out of 4) stage of maturity. Cryptographic agility is the power to vary the underlying cryptographic algorithms in purposes and communications channels. I imagine this highlights the significance for organizations to have the ability to pivot their encryption algorithms to a post-quantum cryptographic world. As quantum computing turns into extra extensively out there, the power to crack sturdy encryption turns into weaker.
In August 2016, NIST revealed a request for touch upon necessities and standards for submission for nominations for Public-key Put up-quantum Cryptographic (PQC) Algorithms. That implies that 7 years in the past, the hunt for a PQC began. In 2024, that is anticipated to be finalized. Nevertheless, there are steps that organizations must be taking now to arrange for this. To know why PQC is so essential, you will need to comply with the evolution of public-key cryptography.
Public-key cryptography
Public-key cryptography is what permits safe connections equivalent to over the Web. With out these safe connections, there could be no on-line banking, purchasing, or personal messaging. Public-key cryptography depends on algorithms which might be primarily unbreakable with at the moment’s know-how.
This wasn’t all the time the case. Attributable to more and more extra highly effective computer systems, older algorithms turned extra vulnerable to brute-force assaults. For example, RC5-64 was cracked in slightly below 5 years utilizing 2002 know-how –that’s primarily an Intel Pentium II operating Home windows NT– with teams of individuals donating private pc cycles. Evaluating present know-how vs. 2002, we will simply throw a lot processing energy, together with renting from a cloud present, that the auto-generated abstract from that comparability hyperlink is astonishing:
“In single core, the distinction is 8100%. In multi-core, the distinction when it comes to hole is 42425%.”
This is likely one of the causes we moved from SSL to TLS1.0 and have continued to advance to TLS1.3. Older legacy algorithms develop into deprecated and are now not in use.
Public-key cryptography isn’t simply used for internet servers for SSL/TLS. They’re used to safe electronic mail, SSH/SFTP connections, digital signatures, Cryptocurrencies, and anyplace PKI (Public Key Infrastructure) is used together with Microsoft Lively Listing. If the present set of algorithms might be breached through brute pressure assault, the Web might collapse, and this may have a devastating impact on the worldwide financial system and even scale back the effectiveness of navy communications.
Fortuitously, with many present “classical” applied sciences, we now have been ready so as to add extra bits in algorithms to make them harder, making brute pressure assaults more durable over time. For example, SHA-2 went from 224 to 256 to 384 all the best way to 512 earlier than being largely changed by SHA-3, which is safer with similar variety of bits. No less than, this was the trail ahead earlier than quantum computing turned a brand new viable option to crack these legacy algorithms.
What’s a quantum pc?
You might be conversant in Diffie-Hellman key trade, the RSA (Rivest-Shamir-Adleman) cryptosystem, and elliptic curve cryptosystems at the moment in use at the moment. The safety of those is dependent upon the problem of sure quantity theoretic issues equivalent to Integer Factorization or the Discrete Log Downside over varied teams.
In 1994, Shor’s algorithm was developed that might effectively resolve every of those applied sciences. Nevertheless, this algorithm relied on a totally totally different structure: quantum computer systems. Within the final 29 years, work has progressed to not solely create new quantum algorithms however the precise {hardware} to run them on (preliminary quantum computer systems have been emulated utilizing classical computer systems and really sluggish). Just lately, Google has developed a 70-qubit quantum pc. A qubit is the quantum pc equal of classical pc 1’s and 0’s, and extra qubits imply a extra highly effective system. This Google system referred to as the Sycamore Quantum Pc can resolve a fancy benchmark in a number of seconds. The world’s present quickest classical supercomputer, referred to as Frontier from Hewlett Packard, would take 47 years on that very same benchmark.
Whereas this can be a extremely particular check, it did exhibit “quantum supremacy”: that quantum computer systems can outpace classical computing programs. If you’re not involved as a result of these computer systems are costly, know that cloud suppliers have already got choices you need to use at the moment: Azure Quantum, IBM and AWS Braket allow you to lease time at underneath $100 an hour. Google Quantum Computing Service seems to solely permit entry from an authorized listing, not (but) giving entry to the general public. Just lately. the Gemini Mine, which is a 2-qubit quantum pc, turned out there to purchase immediately for about $5,000. This isn’t a robust machine however might be used to invisibly develop and check malicious quantum software program.
Nevertheless, the longer term is evident: Quantum computing breaks the present cryptographic algorithms.
What’s a PQC and why do I want to make use of it?
Put up-quantum Cryptography (PQC) relies on algorithms that may resist each classical and quantum computer systems. Because the present algorithms should not PQC, they’re going to be focused by dangerous actors and something utilizing them will now not be successfully encrypted.
Whereas quantum computer systems are nonetheless of their infancy, you would possibly assume which you could sit again after which after they go mainstream, merely transfer to a PQC algorithm when the danger turns into excessive sufficient. Nevertheless, there’s a want to maneuver to a PQC as quickly as doable: any encrypted knowledge equivalent to web transmissions might be saved, after which later decrypted. Organizations should assume that something utilizing present encryption algorithms must be handled as cleartext.
Utilizing PQC will then set up a line within the sand: even when transmissions are recorded or encrypted drives are stolen, they will be unable to be decrypted by quantum computer systems or classical supercomputers. Backups utilizing previous algorithms? Assume they’re cleartext and erase them. Any secrets and techniques that have been despatched over the web? Assume they’re now within the public area.
Whereas governments have lengthy remoted communications channels so even encrypted communications are onerous to smell, most personal organizations don’t – and may try to maneuver to PQC as quickly as doable.
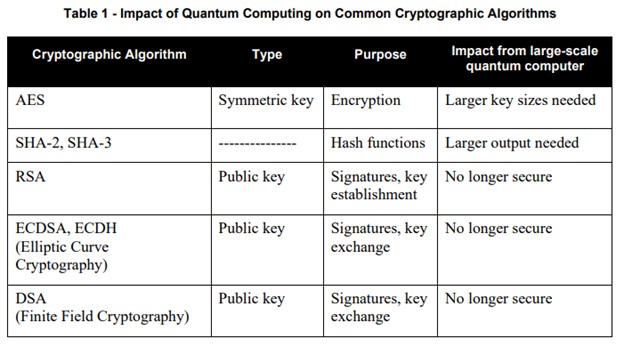
Desk 1 from NIST IR 8105 exhibits the most well-liked cryptographic algorithms and the impression quantum computer systems could have on them.
NOTE: This was revealed in April 2016.
How ought to my group put together?
Though a PQC algorithm isn’t anticipated till 2024, organizations ought to put together and take steps to make the migration a fast course of:
- Stock all cryptographic algorithms at the moment in use.
- What programs are used?
- Is that this knowledge at relaxation or in transmission?
- Prioritize this stock in order that when your group must implement it, the high-risk assets are addressed first – equivalent to Web-facing programs or programs that home your most delicate knowledge.
- Doc for every system kind the method required to change the in-use algorithm.
- Do we have to improve the important thing size (AES and SHA2 or SHA-3) or substitute the algorithm completely (RSA, ECDSA, ECDH, DSA)
- System updates or PQC algorithm set up
- Configuration file modification
- Restarting important providers
- Testing course of to make sure PQC algorithms are most popular/prioritized between programs when they’re negotiating which algorithm to make use of.
- Assessment your provide chain and perceive the place you want third events to ship PQC.
- For example, if you’re operating accounting software program SaaS, you need to have the ability to hook up with it out of your workstation securely. You’re reliant on that SaaS to assist PQC and must be asking for that as quickly as doable. Relying on the danger profile, it’s possible you’ll wish to deal with that in any contractual negotiations to assist guarantee it occurs.
These preparation steps ought to both be added to your regular governance processes or made right into a venture. Determine if you need to use inside assets or should you ought to herald a 3rd celebration like AT&T Cybersecurity to assist. In any case, be certain that is in your radar prefer it now could be on mine. As soon as post-quantum cryptographic algorithms develop into out there, all organizations must be trying to implement them.
Sources to study extra:
DHS: Making ready for Put up-Quantum Cryptography Infographic (dhs.gov)
NIST: Report on Put up-Quantum Cryptography (nist.gov)
CISA: Quantum-Readiness: Migration to Put up-Quantum Cryptography (cisa.gov)
NSA: The Industrial Nationwide Safety Algorithm Suite 2.0 and Quantum Computing FAQ (protection.gov)
[ad_2]