[ad_1]
Safety engineering is a fast-moving area with an outsize influence throughout all facets of enterprise—estimates point out that there are trillions of {dollars} at stake. On this ask-me-anything-style Q&A, Toptal safety engineer Gökay Pekşen solutions questions from software program builders around the globe, overlaying main compliance frameworks, high cloud and AWS safety checks, and the significance of DevSecOps within the cloud.
Early in his profession, Gökay grew to become considered one of Turkey’s first Licensed Moral Hackers; he later constructed Turkey’s first DevSecOps steady integration and steady supply (CI/CD) pipeline. He’s the founder and CEO of Prime Risk, a cybersecurity consultancy that helps companies navigate GDPR compliance and threat administration, and brings 15 years of expertise in IT safety to this dialog.
Editor’s notice: Some questions and solutions have been edited for readability and brevity.
Getting Began With DevOps and Safety Engineering
What does a safety engineer do? What sorts of duties do you’re employed on everyday?
—M.D., Seattle, United States
A safety engineer safeguards a corporation’s digital belongings and knowledge from cyberthreats. They assess dangers, design and implement safety measures, and implement insurance policies and procedures to make sure the integrity and confidentiality of IT assets. Safety engineers conduct common audits, handle vulnerabilities, and reply to safety incidents, working to stop breaches and mitigate their influence.
My day-to-day work varies vastly relying on what sort of mission I’m engaged on. If it’s an data safety mission, I normally analyze the technique, examine the processes, modify them to the dynamics of the respective firm, and write documentation. If it’s a cybersecurity mission, I normally conduct penetration checks, management the principles and configurations, and implement or enhance safeguards. I like working with corporations as a Digital Chief Data Safety Officer (vCISO) as a result of I get pleasure from creating methods and guiding groups on the right way to implement them.
Are you able to inform us extra about the right way to grow to be a safety engineer? What was your path into this profession?
—S.S., Minneapolis, United States
Whereas engaged on my bachelor’s diploma in laptop engineering, I grew to become one of many first Licensed Moral Hackers in Turkey. This naturally drove me to grow to be a safety skilled. All through my profession, I’ve at all times stayed targeted on the basics, significantly Linux, networking, and C. I’ve additionally invested time in coaching and mentoring others, which has developed my skilled community and additional superior my very own expertise over time.
To grow to be a safety engineer, you might need to pursue increased schooling in laptop science, data know-how, or cybersecurity. Contemplate in search of out internships in considered one of these fields as effectively. It’s going to take time to develop foundational technical experience with programming languages, working methods, and networking ideas. Familiarize your self with cybersecurity and DevOps fundamentals, together with encryption, entry management, and safety protocols. Past technical expertise, efficient communication and problem-solving expertise are essential for fulfillment on this area.
What path do you recommend for somebody in DevOps and cloud infrastructure to increase their area information into cybersecurity and DevSecOps? Are there books or programs you’d suggest?
—W.Y., Vancouver, Canada
In case you are a newbie, you might begin by pursuing a CEH or OSCP course—however you want extra than simply certifications to hone your experience. Books like Cybersecurity Necessities by Charles J. Brooks et al. can present a complete introduction to cybersecurity fundamentals. These with a DevOps and cloud infrastructure background ought to deal with cloud safety and should profit from studying Cloud Safety and Privateness by Tim Mather, Subra Kumaraswamy, and Shahid Latif. From there, you possibly can additional discover DevOps safety integrations by studying DevOpsSec by Jim Chook and Securing DevOps by Julien Vehent; each books present perception into this space.
What’s DevSecOps precisely, and the way can organizations simply getting began with it easily incorporate safety into DevOps? For these ranging from scratch, what’s the optimum strategy to arrange a security-focused tradition?
—Okay.S., Montreal, Canada
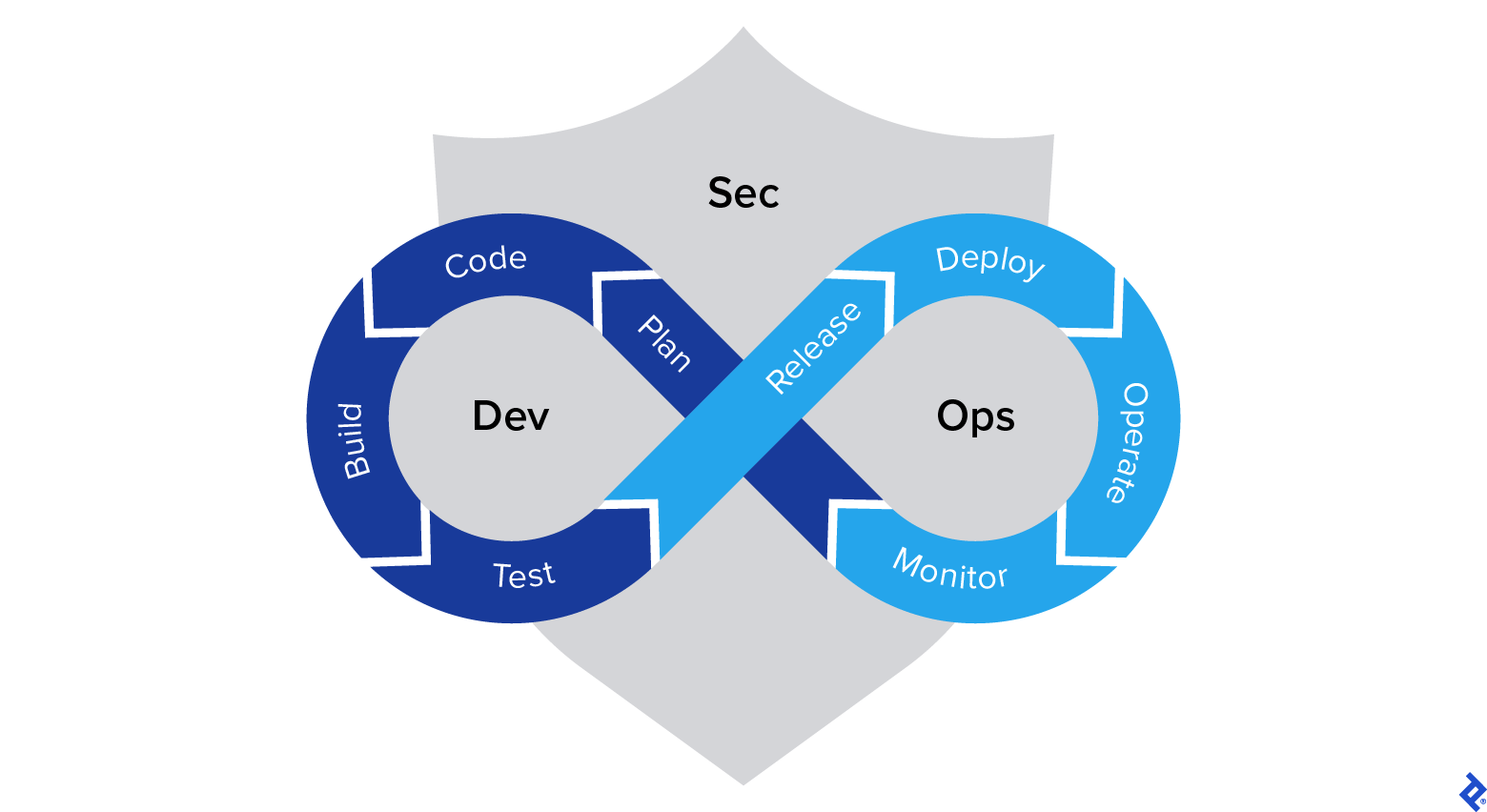
For my part, DevSecOps represents essentially the most essential transformation {that a} enterprise can spend money on proper now. Automation is a caretaker: It eliminates the danger of error, and acts independently of the destructive facets of human nature. Routines is usually a burden, and handbook operations invite too many alternatives for errors or carelessness. Repeating the identical duties could make us inefficient and trigger us to lose focus and curiosity. As human beings we’d like challenges and new experiences. Who needs to deploy equivalent machines from a template, run the identical guidelines again and again, or learn supply code till the tip of time? I don’t suppose anybody does.
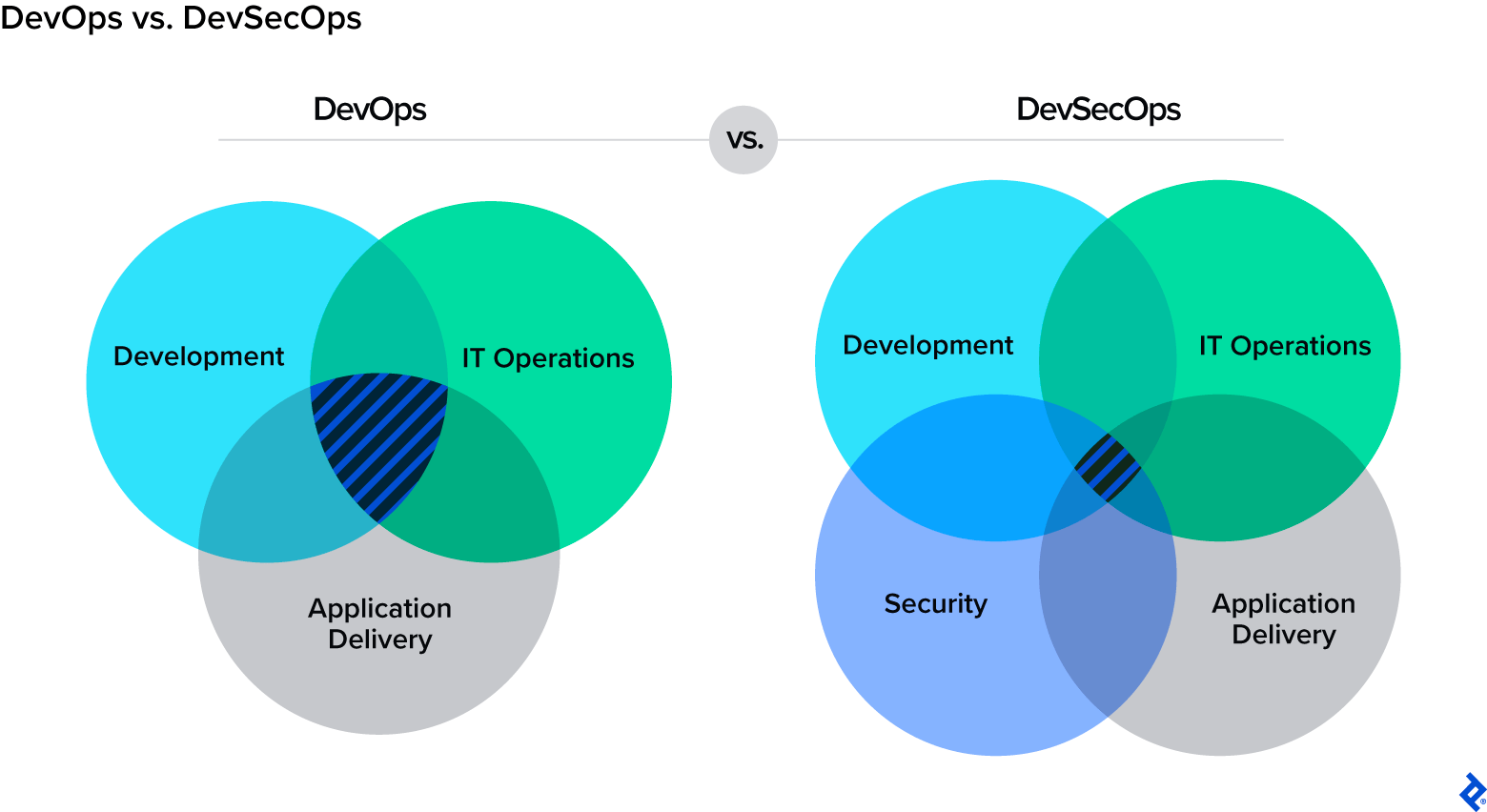
DevSecOps mixes three essential components of IT into one pot: growth, safety, and IT operations. It’s difficult to assemble these big subjects collectively, and it’s even more durable to handle them as one cohesive unit. I’ve carried out or in any other case been concerned in many various CI/CD pipelines, and I’ve noticed firsthand how operations immediately grow to be extra environment friendly if you get rid of the burden of handbook operations.
Establishing a safety tradition is difficult; in truth, I’d say it’s almost not possible to domesticate from the within. There might be resistance from workers who could also be set of their methods, and you will have somebody to information you and illuminate the trail. More often than not this implies you’ll require a consultancy to step in.
Safety Issues and Greatest Practices for Companies
What are the principle variations between main compliance frameworks? Are any significantly suited to particular industries?
—Okay.S., Montreal, Canada
Frameworks and requirements are equivalent when utilized to entities or belongings, however they differ for industries. Consider it this manner: A firewall is a firewall—regardless of the place you place it. When you consider entities by their attributes, they may act the identical in each framework. However the objective of the entities or belongings will differ from trade to trade. For instance, an internet server might deal with monetary knowledge for a banking firm, however it can deal with private identifiable data (PII) for a well being establishment: similar entity, totally different sector, totally different outcomes.
ISO 27001 is the commonest commonplace for safety. A lot of the requirements and frameworks are constructed on ISO 27001, in order that’s one of the best place to begin, whatever the trade. Making use of it to your each day job is the best strategy to understand it.
What primary safety checks would you suggest to check an internet software?
—Okay.G., Łódź, Poland
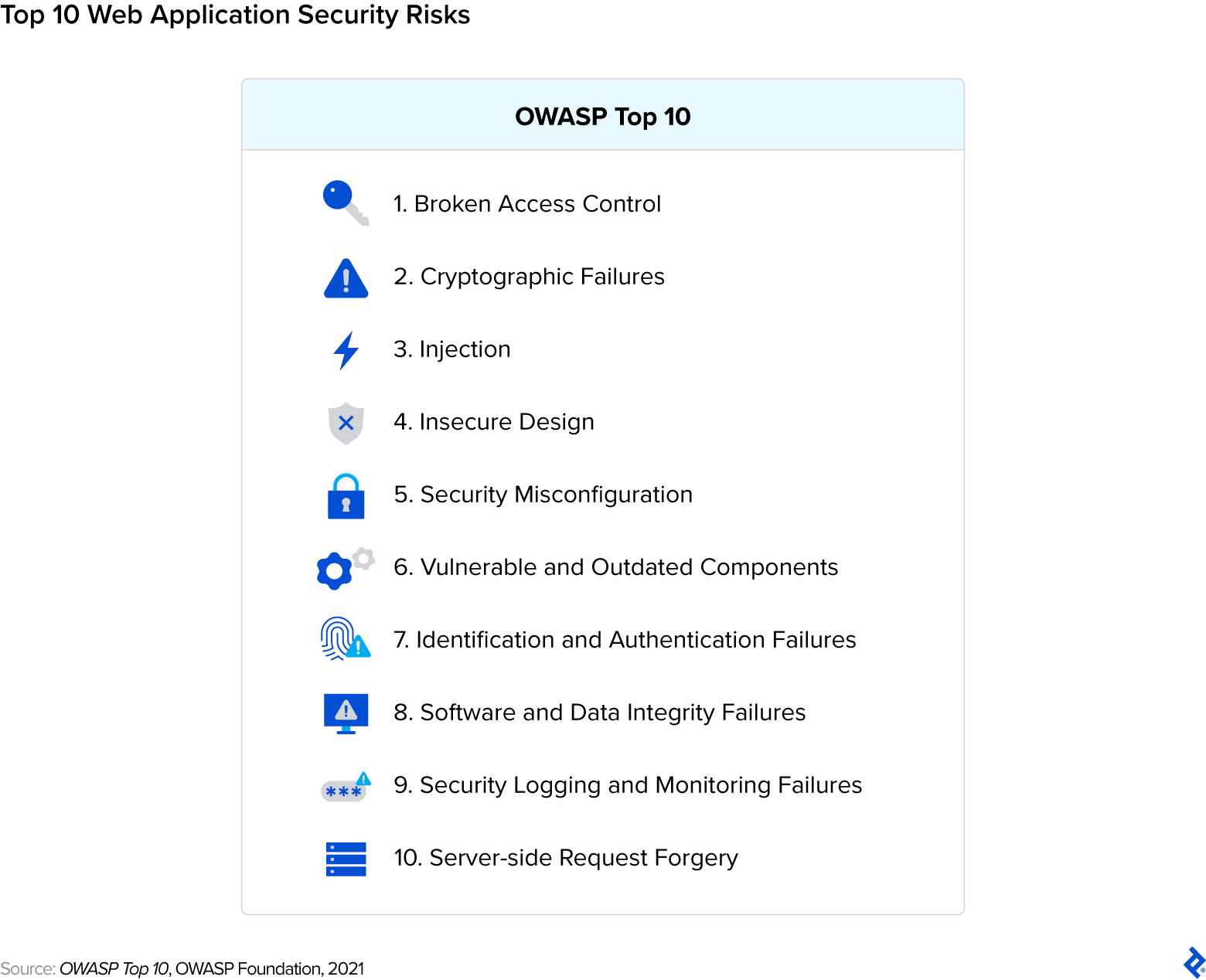
The highest 10 checklist from Open Internet Utility Safety Mission (OWASP) is a should for net software safety; I like to recommend it to everybody. It’s a group of standardized and developer-friendly assets to assist organizations determine, prioritize, and mitigate essentially the most essential safety vulnerabilities in net purposes. It’s additionally up to date frequently.
With so many various AWS choices, the place ought to groups get began with regard to AWS safety finest practices? What are essentially the most essential companies to safe?
—Okay.S., Montreal, Canada
The reply to this query largely depends upon what companies you’re utilizing. AWS is an enormous world; there are such a lot of totally different instruments and companies at each degree of the tech stack. Establish and entry administration (IAM), net software firewall (WAF), digital personal cloud (VPC), CloudTrail, S3 bucket safety, and infrastructure as code (IaC) instruments are all nice locations to begin, and relevant to most AWS customers working at scale. There are extra instruments accessible for knowledge safety and automation that you could be need to look into, relying in your particular use case. I’d suggest consulting with an AWS specialist to find out your wants.
The Way forward for Cybersecurity
Might you define the influence of the advances in generative AI in your work?
—J.B., Vienna, Austria
I create the way in which, and generative AI walks the trail. I inform it to create distinctive documentation units to adjust to particular frameworks for the businesses. I ask it to examine code to see whether it is susceptible to any exploits or to find out whether or not a configuration file might result in a cybersecurity assault.
Generative AI looks like a complete new frontier on this area. I take advantage of it each day. It’s particularly useful after I must shortly discover ways to use new instruments and applied sciences.
What are the challenges when implementing zero belief structure (ZTA) in cloud-based environments?
—O.T., Istanbul, Turkey
Zero belief places the precept of “by no means belief, at all times confirm” into motion, as a response to the extra conventional method of “implicit belief,” wherein customers and their units are assumed to be reliable after they’re verified and linked to a permissioned community. ZTA is about privilege administration: It goals to stop malicious actors from shifting laterally via the community to achieve delicate supplies to which they weren’t explicitly granted entry.
Nevertheless, ZTA is a generally misunderstood matter as a result of safety distributors are more and more remarketing their merchandise to capitalize on the novelty of this time period, even when it may not be related or relevant. They usually describe any firewall, endpoint safety platform, or entry administration device (like IAM) as performing like ZTA—however this isn’t technically true. Merely making use of a safety product to a community is a a lot totally different expertise than sustaining a tradition of safety inside that community; no particular person product can substitute the continued work required to place ZTA into observe.
Earlier than you implement ZTA, you will need to take all related stakeholder, shareholder, provider, and connection relationships into severe consideration. The cloud is supposed to be a extra versatile and free atmosphere than what we work with in enterprise software program. To make {that a} actuality, corporations must be meticulous about figuring out what’s really essential to safeguard. Defending confidential data isn’t just an moral obligation—it’s additionally good for enterprise. By securing your financial engine, you construct belief and preserve a aggressive edge.
How do you suppose exploits will proceed to evolve? Initially we had binary injections, net exploitation, SQL injection, and HTTP compromise—to not point out good old school social engineering, like phishing. What’s subsequent? What’s the most recent development?
—J.O., Fortaleza, Brazil
Generative AI is simply now starting to point out us distinctive exploits and payloads which have by no means been seen earlier than. It really works in opposition to us. Earlier than lengthy, we are going to begin to see totally different assault strategies and exploits due to the brand new vectors created by AI. I want I might say extra about this, however it will be harmful to share too many particulars.
Going ahead, each new assault will evolve and alter itself by gathering and responding to data in its atmosphere. We’re additionally starting to see assaults on AI-based operations, like knowledge poisoning within the generative AI ecosystem. Issues will change. Safety professionals are already devising immediate firewalls to stop ChatGPT knowledge leakage.
The subsequent huge factor might be quantum safety, however it could be too quickly to debate it. Quantum safety is an interdisciplinary area that mixes facets of quantum physics, arithmetic, and laptop science, and opens up alternatives for collaboration throughout these domains. Ahead-thinking organizations, particularly these with long-term knowledge safety wants, are exploring and adopting quantum-resistant encryption options to future-proof their knowledge safety.
Nevertheless, it’s important to notice that whereas quantum safety is gaining momentum, it could solely partially substitute conventional encryption in some use circumstances. Some cryptographic algorithms are computationally safe even in opposition to quantum assaults, and never all knowledge requires quantum-resistant encryption.
[ad_2]