
[ad_1]
In right this moment’s fast-paced and hyper-connected world, gone are the times when deploying community units required sending an knowledgeable to every location — a cumbersome, time-consuming, and error-prone course of that precipitated important downtime and elevated operational prices. To surmount these obstacles, Cisco gives quite a lot of community orchestrators. These included Cisco Catalyst Middle (previously Cisco DNA Middle), SD WAN Supervisor (previously Cisco vManage), and Meraki Dashboard, which help companies in automating their campus community administration together with Day 0 provisioning. These orchestrators enable community directors to remotely deploy numerous community units shortly and securely, with out requiring any human intervention. This not solely saves money and time but additionally liberates IT division assets, permitting them to redirect their efforts in the direction of different essential areas.
Utilizing Catalyst Middle PnP, Cisco IT was in a position to scale back annual deployment prices for some websites by roughly 25%, or greater than $1.6 million. Moreover, upgrading our 285 small and medium-sized places of work with Cisco Catalyst Middle saved 570 man-hours per improve[1].
Along with Cisco community orchestrators for patrons using a Do-It-Your self (DIY) method with homegrown instruments, Catalyst 9000 collection switches supply help for an assortment of open standard-based implementations for Day 0 community automation, reminiscent of Preboot eXecution Setting (PXE) and Zero Contact Provisioning (ZTP). So, if you end up nonetheless manually configuring community units, it might be time to contemplate stepping out of the stone age and exploring the advantages of automation.
Day 0 community automation
When delving into the realm of open standard-based Day 0 community automation, it turns into clear that PXE, whereas a helpful approach, comes with a set of limitations, reminiscent of solely permitting community units as well from a network-based supply and never having the ability to ship configurations to units throughout the PXE workflow. ZTP, alternatively, can be utilized to improve software program photographs and push configuration recordsdata, lowering the possibility of human error and making certain configuration consistency to be able to get community units up and operating.
Whereas ZTP and PXE are handy for automating the provisioning course of, they might inadvertently expose community units to potential threats. Lack of safe authentication and verification mechanisms throughout the provisioning course of is likely one of the major issues with these strategies. Moreover, ZTP and PXE make the most of HTTP/TFTP to obtain the software program picture or configuration recordsdata, that are inherently insecure protocols as a result of they lack encryption. Because of these limitations, these strategies might end in unauthorized entry to the system or a man-in-the-middle assault if the fitting safety measures aren’t put in place throughout the system provisioning.
Cyberattacks have elevated
In right this moment’s quickly evolving digital panorama, the place enterprises are present process substantial transformation, cyberattacks have elevated amid the rise of cloud computing, hybrid and multi-cloud networks, and the rise of distant work. In keeping with the most recent IBM Ponemon Institute 2023 Price of Knowledge Breach Research, the typical value of an information breach reached an all-time excessive in 2023 of USD 4.45 million [2]. Moreover, in line with ITIC’s 2022 World Server {Hardware} Safety report, 76% of corporations cite Knowledge Breaches and Human Error because the main purpose of server, OS, software, and community downtime, and the hourly value of downtime has risen to over $300,000[3].
Provided that cybercriminals are always devising new strategies to infiltrate networks, the normal safety method, which assumes that every part throughout the community perimeter is reliable, is now not enough. That is additionally true for Day 0 community automation, the place it’s essential to validate the trustworthiness of the newly deployed system, bootstrap server, and configurations pushed to the system. With out implementing these safety measures, our networks are weak to quite a lot of cyberattacks, together with the infamous zero-day exploits. To make sure maximal safety and decrease potential dangers, the Zero Belief precept of “by no means belief, all the time confirm” should be carried out all through your complete provisioning course of.
Keep safety all through the provisioning course of
That is the place Safe Zero Contact Provisioning comes into play. Safe ZTP, as described in RFC 8572, is an enhanced model of ZTP that emphasizes sustaining safety all through the provisioning course of by lowering the probability of safety breaches. Safe ZTP is a proactive method that employs strong authentication, a safe boot mechanism, and encrypted communication channels to reinforce the safety posture of a community whereas Day 0 community automation is in place.
How does Safe ZTP work?
Safe ZTP employs three-step validation, together with system validation, server validation, and artifact validation, to securely onboard the system. The diagram supplied beneath illustrates the assorted steps concerned within the system onboarding and provisioning course of inside a safe ZTP framework. Let’s take a more in-depth have a look at every of those steps:
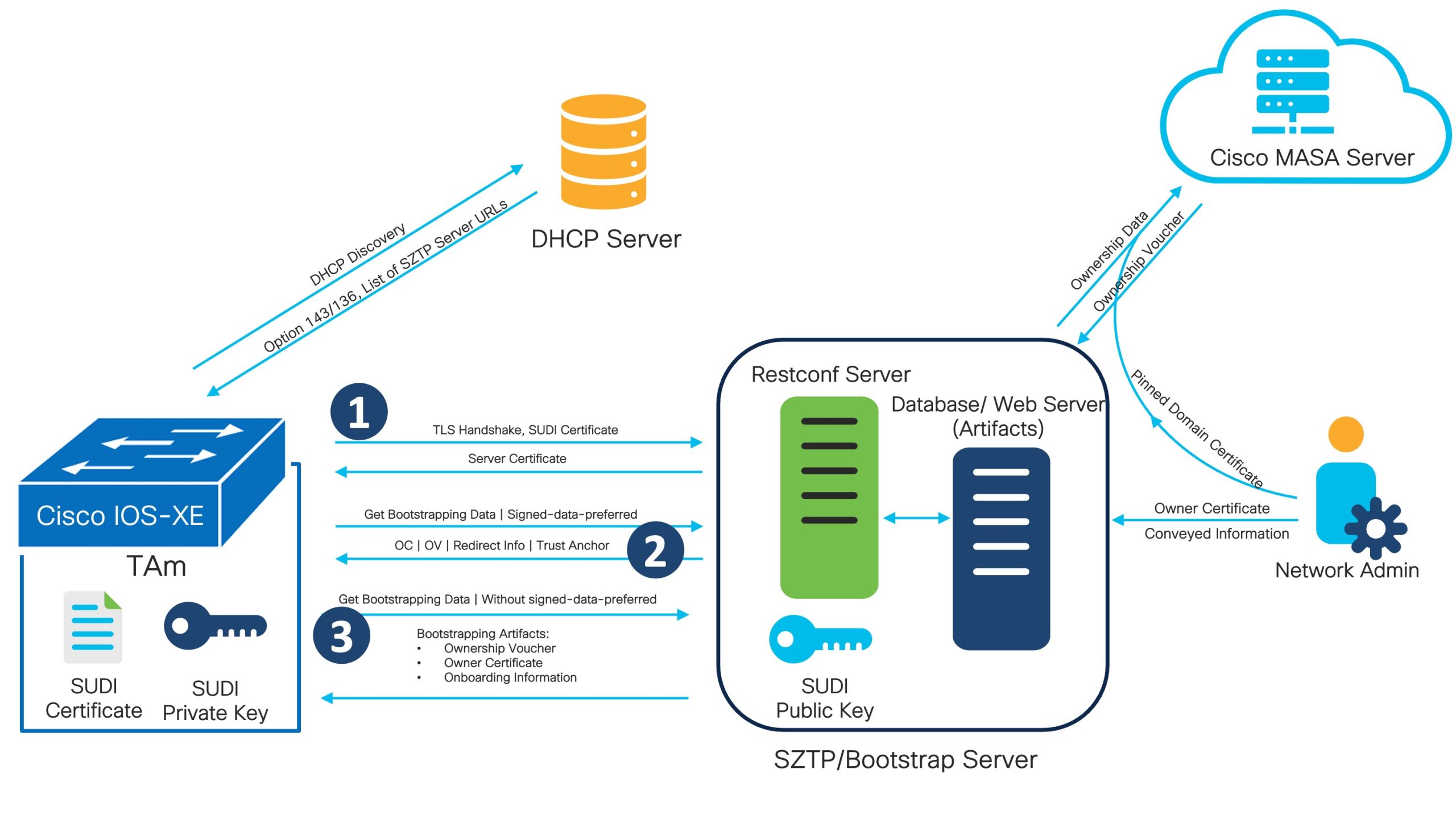
1. Gadget Validation
Earlier than onboarding a brand new system on the community, it’s essential to make sure that neither the system nor its firmware has been tampered with or compromised to forestall provide chain or some other assaults, during which malicious actors try to introduce modified or malicious units into the community. Based mostly on the latest IBM report, 15% of organizations recognized a provide chain compromise because the supply of an information breach [2].Safe ZTP performs system authentication previous to provisioning it to be able to confirm the integrity and authenticity of a tool and to permit solely licensed units to hitch the community.For system validation, Safe ZTP makes use of certificate-based authentication the place the system sends the Belief Anchor Certificates (often known as a SUDI certificates put in within the system throughout the manufacturing course of) to the Safe ZTP server, and the server validates it with the general public certificates (supplied by the producer) to make sure the system’s authenticity.
2. Server Validation
Server validation is one other important a part of the Safe ZTP. By confirming the server’s id, the system can guarantee that it’s speaking with an uncompromised, reliable server. This prevents unauthorized or malicious servers from intercepting or manipulating the provisioning course of. After verifying the system, bootstrap server sends server certificates. The system requests bootstrapping information with the flag “signed-data-preferred” after receiving the server certificates, indicating that the system doesn’t belief the server. On this case, needless to say server validation is optionally available in Safe ZTP. If the community administrator decides to carry out server validation (which entitles server to obtain bootstrapping progress report), the server will ship the “redirect-data” with different bootstrapping information to the system, offering its personal deal with and the belief anchor. The system verifies the server’s certificates and marks it as trusted server after receiving the belief anchor. Right here, if the system administrator opts to not validate the server, the server will as a substitute cross on bootstrapping information rather than the “redirect-data”. As well as, the system will proceed the bootstrapping course of assuming the server is untrusted.
3. Artifact Validation
Artifact validation is essential to make sure that the configuration recordsdata or software program photographs used to provision community units are genuine and haven’t been tampered with. As soon as the server validation is full (or skipped), the bootstrap server will ship the proprietor certificates, possession voucher, and onboarding info to the system as bootstrapping information. Let’s talk about them intently to realize a greater understanding.
- Possession Voucher (OV): The possession voucher artifact validates the proprietor certificates to confirm the id of the system’s proprietor. The system manufacture indicators the OV and offers it to the client primarily based on the request. To generate the OV, the client should present the pinned-domain-cert and serial variety of the system to the Cisco MASA server.
- Proprietor Certificates (OC): Proprietor Certificates is an X.509 certificates that binds an proprietor id to a public key, which a tool can use to validate signature over the conveyed info artifact. The proprietor certificates additionally holds all intermediate certificates that led to the “pinned-domain-cert” certificates specified within the possession voucher, permitting the OV to validate the OC.
- Conveyed Info/Onboarding Info: Onboarding info offers information mandatory for a tool to bootstrap itself and set up safe connections with different methods. Onboarding info specify particulars concerning the boot picture a tool should be operating, an preliminary configuration the system should commit, and scripts that the system should efficiently execute. The onboarding info should be signed by the system’s proprietor utilizing OC.
Zero Belief is essential when performing Day 0 provisioning
Along with its many options, Safe ZTP goes past by providing audit trails and monitoring capabilities. This consists of logging all provisioning occasions, configuration adjustments, and person actions. By monitoring ZTP actions, community directors can shortly detect any suspicious exercise and take applicable motion.
As we wrap up our dialogue, it turns into clear that Zero Belief can be essential when performing Day 0 provisioning, and Safe ZTP is one of the simplest ways to make sure that zero belief rules are utilized whereas performing Day 0 provisioning utilizing a Do-It-Your self (DIY) method.
With the IOS-XE 17.11.1 launch, customers can now benefit from the safe Zero Contact Provisioning (ZTP) capabilities with Catalyst 9000 collection switches. This thrilling function aligns with the specs outlined in RFC 8572, making certain a safe and seamless provisioning expertise. For extra particulars about the right way to implement Safe ZTP, please refer the IOS-XE 17.11.1 Configuration Information.
Maintain Studying with these assets
References
- Cisco DNA Middle: Early Outcomes from Intent-based Networking
- Safety, Knowledge Breaches Prime Reason for Downtime in 2022
- IBM – Price of a Knowledge Breach Report 2023
Share:
[ad_2]