
[ad_1]
In giant metropolitan areas, vacationers are sometimes straightforward to identify as a result of they’re much more inclined than locals to gaze upward on the surrounding skyscrapers. Safety consultants say this similar vacationer dynamic is a lifeless giveaway in nearly all pc intrusions that result in devastating assaults like information theft and ransomware, and that extra organizations ought to set easy digital tripwires that sound the alarm when licensed customers and gadgets are noticed exhibiting this conduct.

In a weblog put up printed final month, Cisco Talos mentioned it was seeing a worrisome “improve within the price of high-sophistication assaults on community infrastructure.” Cisco’s warning comes amid a flurry of profitable information ransom and state-sponsored cyber espionage assaults concentrating on a few of the most well-defended networks on the planet.
However regardless of their growing complexity, an excellent many preliminary intrusions that result in information theft could possibly be nipped within the bud if extra organizations began on the lookout for the telltale indicators of newly-arrived cybercriminals behaving like community vacationers, Cisco says.
“Probably the most essential issues to speak about right here is that in every of the circumstances we’ve seen, the risk actors are taking the kind of ‘first steps’ that somebody who needs to know (and management) your surroundings would take,” Cisco’s Hazel Burton wrote. “Examples we now have noticed embrace risk actors performing a ‘present config,’ ‘present interface,’ ‘present route,’ ‘present arp desk’ and a ‘present CDP neighbor.’ All these actions give the attackers an image of a router’s perspective of the community, and an understanding of what foothold they’ve.”
Cisco’s alert involved espionage assaults from China and Russia that abused vulnerabilities in ageing, end-of-life community routers. However at a vital stage, it doesn’t matter how or why the attackers received that preliminary foothold in your community.
It is likely to be zero-day vulnerabilities in your community firewall or file-transfer equipment. Your extra fast and first concern must be: How shortly are you able to detect and detach that preliminary foothold?
The identical vacationer conduct that Cisco described attackers exhibiting vis-a-vis older routers can also be extremely widespread early on in ransomware and information ransom assaults — which frequently unfurl in secret over days or perhaps weeks as attackers methodically determine and compromise a sufferer’s key community belongings.
These digital hostage conditions often start with the intruders buying entry to the goal’s community from darkish net brokers who resell entry to stolen credentials and compromised computer systems. Consequently, when these stolen sources first get utilized by would-be information thieves, virtually invariably the attackers will run a collection of fundamental instructions asking the native system to substantiate precisely who and the place they’re on the sufferer’s community.
This elementary actuality about fashionable cyberattacks — that cybercriminals virtually all the time orient themselves by “wanting up” who and the place they’re upon getting into a international community for the primary time — varieties the enterprise mannequin of an progressive safety firm referred to as Thinkst, which provides away easy-to-use tripwires or “canaries” that may fireplace off an alert each time all types of suspicious exercise is witnessed.
“Many individuals have identified that there are a handful of instructions which are overwhelmingly run by attackers on compromised hosts (and infrequently ever by common customers/utilization),” the Thinkst web site explains. “Reliably alerting when a person in your code-sign server runs whoami.exe can imply the distinction between catching a compromise in week-1 (earlier than the attackers dig in) and studying in regards to the assault on CNN.”
These canaries — or “canary tokens” — are supposed to be embedded inside common recordsdata, performing very like an internet beacon or net bug that tracks when somebody opens an e-mail.
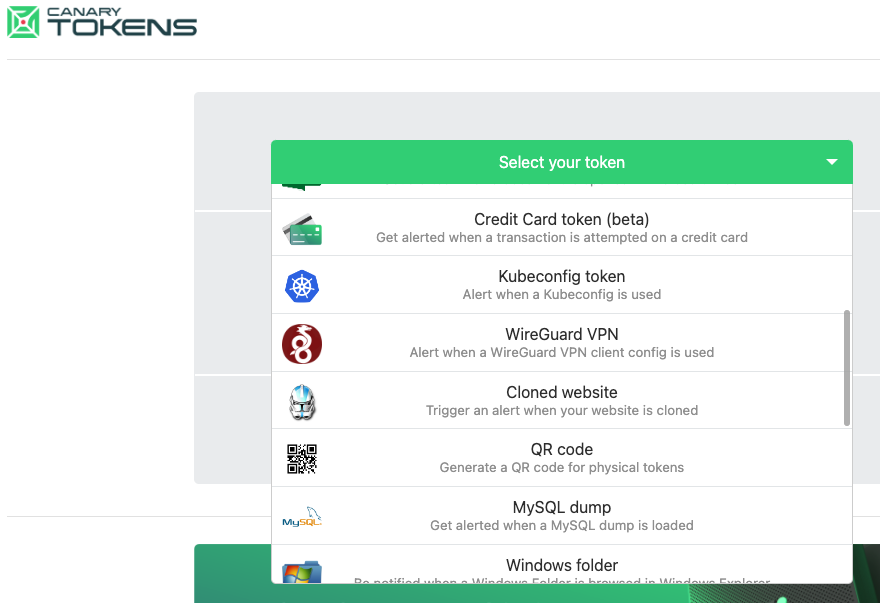
The Canary Tokens web site from Thinkst Canary lists almost two-dozen free customizable canaries.
“Think about doing that, however for file reads, database queries, course of executions or patterns in log recordsdata,” the Canary Tokens documentation explains. “Canarytokens does all this and extra, letting you implant traps in your manufacturing techniques relatively than organising separate honeypots.”
Thinkst operates alongside a burgeoning trade providing so-called “deception” or “honeypot” providers — these designed to confuse, disrupt and entangle community intruders. However in an interview with KrebsOnSecurity, Thinkst founder and CEO Haroon Meer mentioned most deception methods contain a point of hubris.
“Which means, you’ll have deception groups in your community enjoying spy versus spy with folks making an attempt to interrupt in, and it turns into this complete counterintelligence factor,” Meer mentioned. “No person actually has time for that. As a substitute, we’re saying actually the alternative: That you just’ve in all probability received all these [security improvement] tasks which are going to take perpetually. However when you’re doing all that, simply drop these 10 canaries, as a result of every little thing else goes to take a very long time to do.”
The thought right here is to put traps in delicate areas of your community or net functions the place few licensed customers ought to ever trod. Importantly, the canary tokens themselves are ineffective to an attacker. For instance, that AWS canary token positive appears just like the digital keys to your cloud, however the token itself affords no entry. It’s only a lure for the dangerous guys, and also you get an alert when and whether it is ever touched.
One good factor about canary tokens is that Thinkst provides them away without cost. Head over to canarytokens.org, and select from a drop-down menu of accessible tokens, together with:
-a net bug / URL token, designed to alert when a specific URL is visited;
-a DNS token, which alerts when a hostname is requested;
-an AWS token, which alerts when a particular Amazon Internet Providers key’s used;
-a “customized exe” token, to alert when a particular Home windows executable file or DLL is run;
-a “delicate command” token, to alert when a suspicious Home windows command is run.
-a Microsoft Excel/Phrase token, which alerts when a particular Excel or Phrase file is accessed.
Very similar to a “moist paint” signal usually encourages folks to the touch a freshly painted floor anyway, attackers usually can’t assist themselves after they enter a international community and encounter what seem like key digital belongings, Meer says.
“If an attacker lands in your server and finds a key to your cloud surroundings, it’s actually exhausting for them to not attempt it as soon as,” Meer mentioned. “Additionally, when these types of actors do land in a community, they must orient themselves, and whereas doing that they’re going to journey canaries.”
Meer says canary tokens are as more likely to journey up attackers as they’re “pink groups,” safety consultants employed or employed by firms searching for to repeatedly probe their very own pc techniques and networks for safety weaknesses.
“The idea and use of canary tokens has made me very hesitant to make use of credentials gained throughout an engagement, versus discovering various means to an finish aim,” wrote Shubham Shah, a penetration tester and co-founder of the safety agency Assetnote. “If the goal is to extend the time taken for attackers, canary tokens work nicely.”
Thinkst makes cash by promoting Canary Instruments, that are honeypots that emulate full blown techniques like Home windows servers or IBM mainframes. They deploy in minutes and embrace a customized, non-public Canarytoken server.
“Should you’ve received a complicated protection group, you can begin placing these items in actually fascinating locations,” Meer mentioned. “Everybody says their stuff is easy, however we obsess over it. It’s actually received to be so easy that folks can’t mess it up. And if it really works, it’s the perfect bang to your safety buck you’re going to get.”
Additional studying:
Darkish Studying: Credential Canaries Create Minefield for Attackers
NCC Group: Extending a Thinkst Canary to Develop into an Interactive Honeypot
Cruise Automation’s expertise deploying canary tokens
[ad_2]